Sophisticated ‘duer-js’ NPM Package Distributes ‘Bada
Thousands of developers and Windows users now face a significant threat following the emergence of a dangerous malware campaign on the NPM package registry. The malicious package, known as “duer-js,”...
Thousands of developers and Windows users now face a significant threat following the emergence of a dangerous malware campaign on the NPM package registry.
The malicious package, known as “duer-js,” was published by a user named “luizaearlyx” and disguised itself as a legitimate console visibility tool.
Despite having only 528 downloads, security experts warn that its sophisticated attack methods pose serious threats to anyone who installed it.
The malware, self-identified as “Bada Stealer,” remains active on NPM as of this publication, continuing to endanger unsuspecting developers who might include it in their projects.
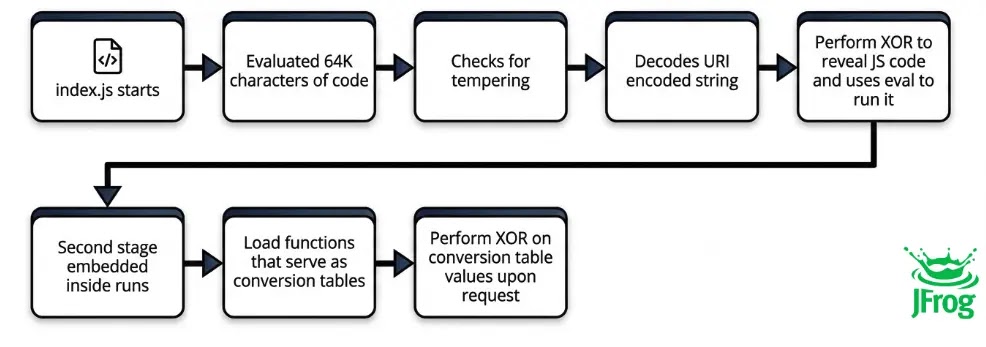
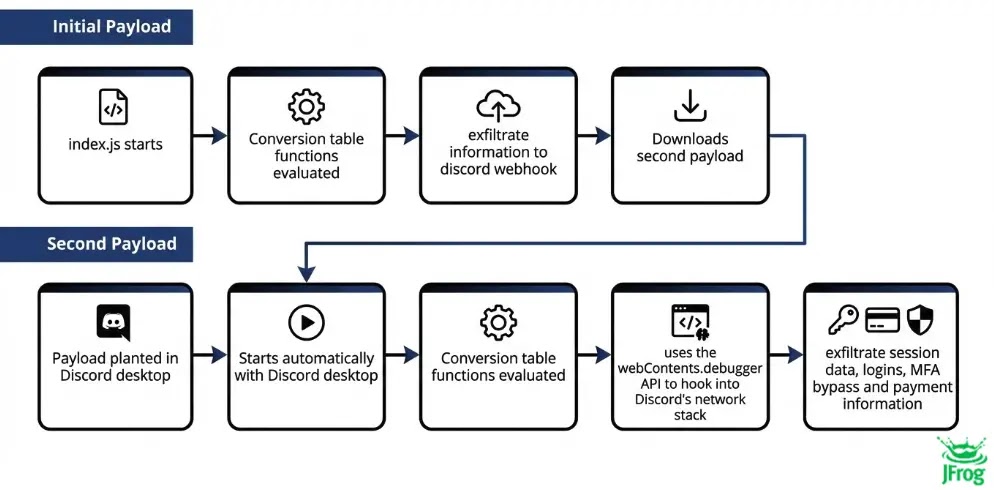
What makes this threat particularly alarming is its multi-stage attack strategy. Once installed, the malware doesn’t just steal data and disappear.
Instead, it downloads a second malicious payload specifically designed to target Discord users.
This secondary component hijacks the Discord desktop application by injecting itself into the app’s startup process, allowing it to continuously monitor and steal sensitive information every time Discord runs.
The malware can capture payment methods, authentication tokens, and even bypass two-factor authentication protections.
JFrog Security Research analysts identified the sophisticated package after conducting detailed analysis of its obfuscation techniques.
The researchers discovered that simply uninstalling the package wouldn’t be enough to remove the infection, as the malware establishes persistence mechanisms that survive basic removal attempts.
How the Malware Steals Your Sensitive Data
The Bada Stealer operates through a carefully designed information theft process. When first executed, it terminates running browser and Telegram processes to access locked files.
The malware then systematically scans the infected system for valuable data across multiple applications.
It targets Discord tokens stored in local databases, extracting not only authentication credentials but also Nitro subscription details, billing information, payment sources, friend lists, and two-factor authentication backup codes.
Browser data collection is equally comprehensive. The stealer extracts saved passwords from Chrome, Edge, Brave, Opera, and Yandex browsers by decrypting them using Windows Data Protection API (DPAPI).
It harvests cookies from multiple profile directories and steals autofill data including credit card numbers, expiration dates, and cardholder names before they’re encrypted.
Cryptocurrency wallet users face particular danger, as the malware specifically hunts for Exodus wallet files and various browser-extension wallets like MetaMask, BraveWallet, and AtomicWallet.
Even Steam users aren’t safe, with the malware compressing and exfiltrating Steam configuration files.
All stolen information gets transmitted to attackers through a Discord webhook, with a backup exfiltration method using Gofile cloud storage.
This dual-channel approach ensures that even if one communication method fails, the attackers still receive their stolen data. The malware creates text files containing passwords, credit card details, and autofill information before uploading them.
If you installed the duer-js package, immediate action is required beyond simple uninstallation. First, completely close Discord and uninstall it through Windows Settings or Control Panel.
Press Win+R, type “%LOCALAPPDATA%”, and delete all Discord-related folders including Discord, DiscordPTB, and DiscordCanary to remove the injected malicious code.
Reinstall Discord from the official website only. Remove any node.exe files from the Windows Startup folder located at “%APPDATA%MicrosoftWindowsStart MenuProgramsStartup”.
Change all passwords stored in your browsers, revoke Discord tokens, enable two-factor authentication if not already active, and review your Discord payment methods for unauthorized changes.
Check cryptocurrency wallets and Steam accounts for suspicious activity. This comprehensive cleanup process ensures complete removal of the infection and protects your accounts from further compromise.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.