APT28 Exploits Microsoft Office Vulnerability in Government
APT28, the Russian state-sponsored threat group, has launched a sophisticated cyber espionage campaign. This operation targets high-value government and military entities across Europe. The primary...
APT28, the Russian state-sponsored threat group, has launched a sophisticated cyber espionage campaign. This operation targets high-value government and military entities across Europe.
The primary targets include maritime and transport organizations in nations such as Poland, Ukraine, and Turkey. The attackers are actively exploiting a critical vulnerability in Microsoft Office, tracked as CVE-2026-21509.
This security flaw allows threat actors to bypass established protections and execute malicious code on compromised systems with alarming ease.
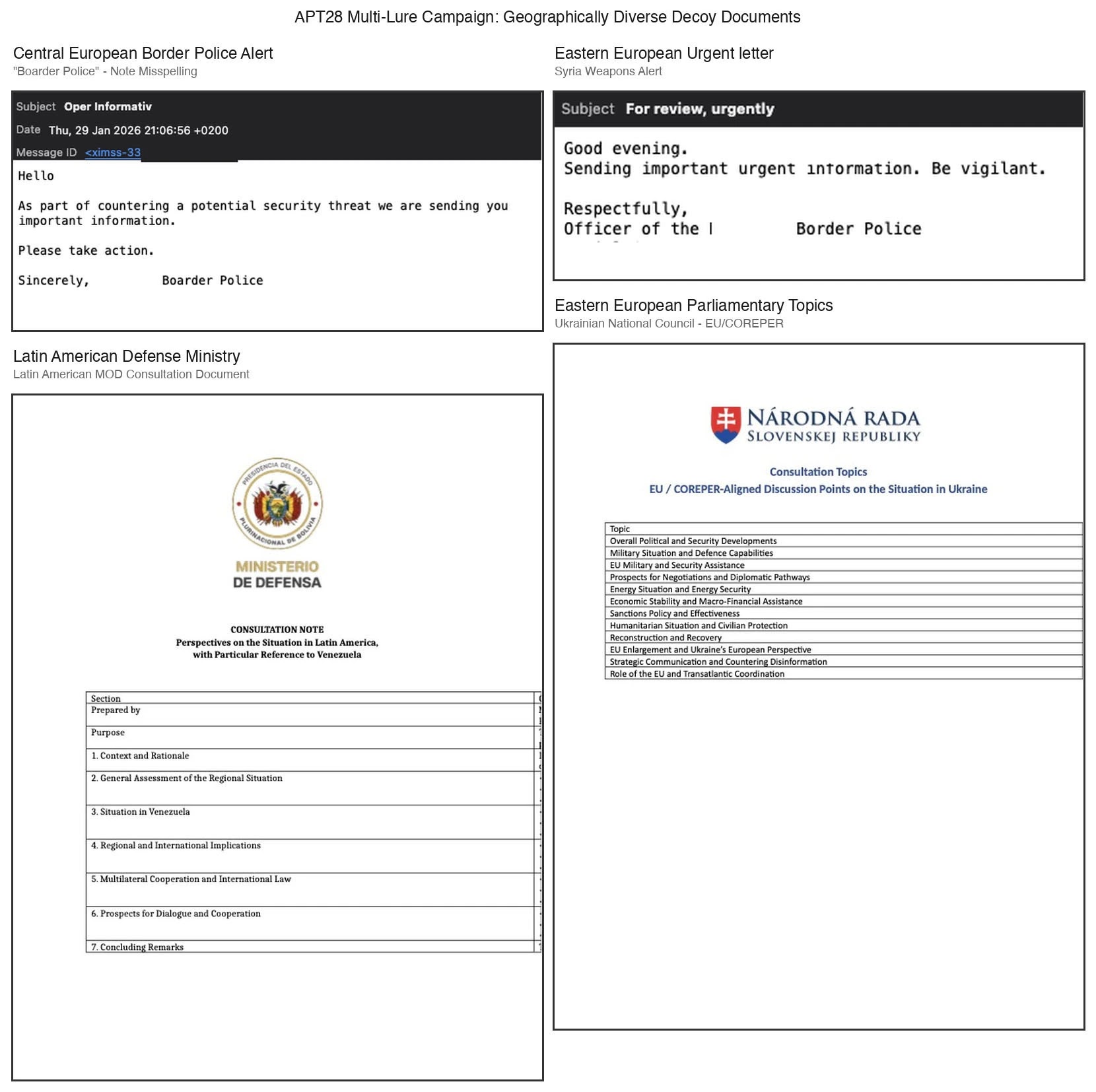
The assault commences with highly targeted spear-phishing emails crafted to mimic urgent official correspondence.
These deceptive messages employ geopolitical lures, such as alerts regarding weapons smuggling or invitations to military training programs, to trick recipients.
When a victim opens the weaponized document, the exploit triggers automatically without requiring any interaction, such as enabling macros.
This “zero-click” capability renders the attack particularly potent against defense ministries and diplomatic institutions.
Trellix analysts identified this malicious activity and highlighted the adversary’s speed, noting they weaponized the flaw within twenty-four hours of its public disclosure.
The attack documents utilize specially crafted embedded objects that leverage the WebDAV protocol to retrieve external payloads from attacker-controlled infrastructure.
This method effectively circumvents standard network defenses by disguising malicious traffic as legitimate web requests, allowing the intruders to establish a foothold undetected.
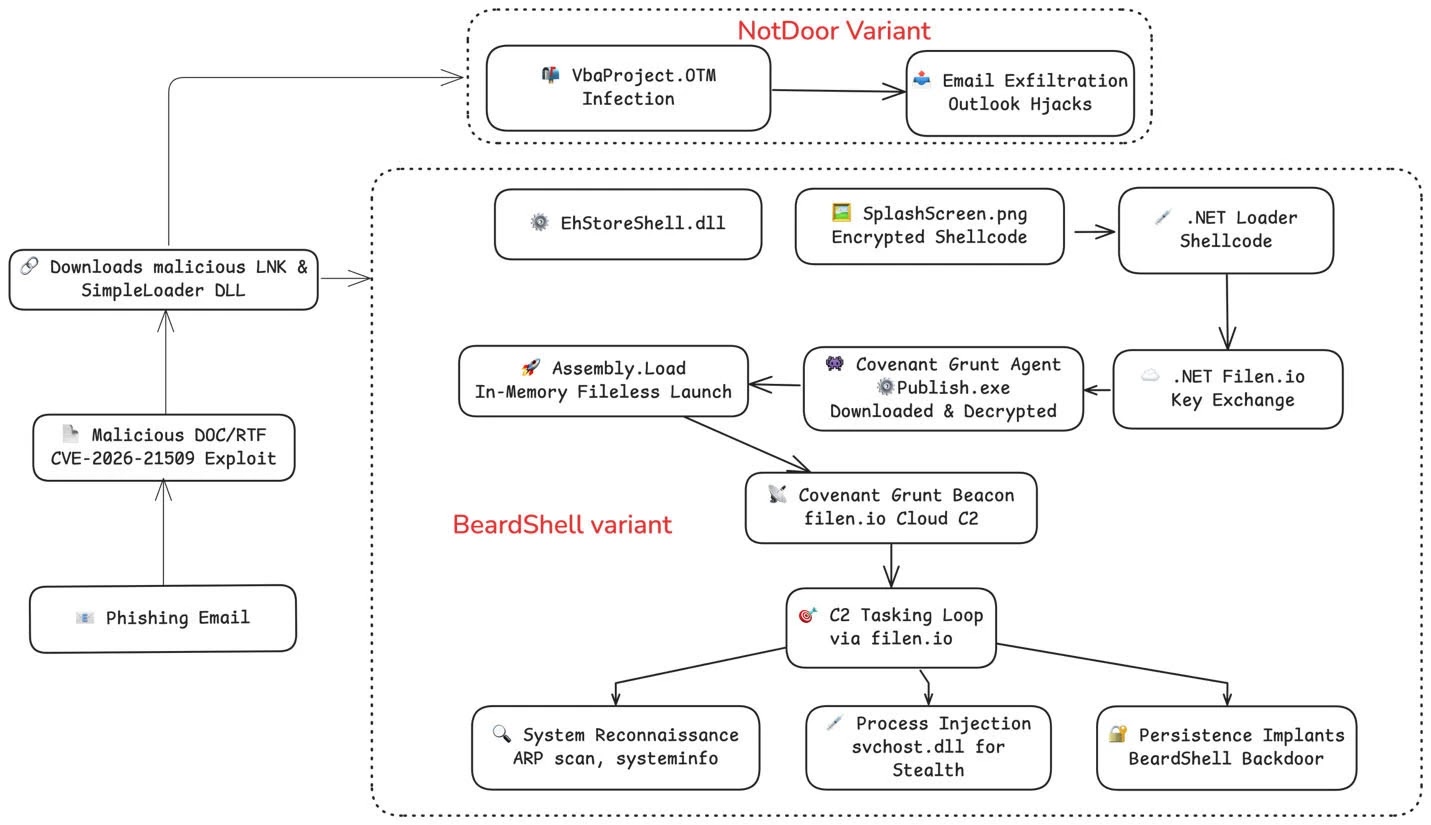
Upon successful exploitation, the hackers deploy a diverse arsenal of custom malware to secure their position.
The primary payloads include a C++ implant dubbed “BeardShell” and a specialized Outlook backdoor named “NotDoor.”
These sophisticated tools enable the attackers to maintain persistent access, steal sensitive intelligence, and move laterally across the victim’s network.
The campaign’s reliance on legitimate cloud services for command and control further complicates detection efforts.
Deep Dive: Evasion and Persistence Mechanisms
The infection chain is meticulously engineered for resilience and stealth, employing multiple layers of obfuscation to bypass security controls.
Following the initial breach, a loader retrieves an encrypted image file containing hidden shellcode. This payload executes the BeardShell backdoor directly in the system’s memory, avoiding disk-based artifacts that traditional antivirus solutions might flag.
The malware also includes anti-analysis routines, such as timing checks, to determine if it is running in a security sandbox.
Furthermore, the attackers abuse the legitimate cloud storage service filen.io to manage their command and control communications.
By encrypting traffic and routing it through this trusted platform, they effectively blend malicious directives with normal user data.
To mitigate these threats, organizations are strongly advised to apply emergency Office patches immediately and restrict the WebDAV protocol. Implementing strict email filtering rules can also help block the initial delivery vectors.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.