ValleyRAT Mimics LINE Installer to Steal User Attacking Users
A sophisticated malware campaign is now distributing the ValleyRAT backdoor, which threat actors are disguising as a legitimate installer for the popular messaging application, LINE. This targeted...
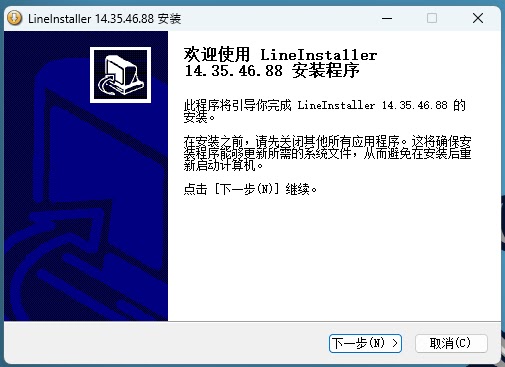
A sophisticated malware campaign is now distributing the ValleyRAT backdoor, which threat actors are disguising as a legitimate installer for the popular messaging application, LINE.
This targeted attack primarily focuses on Chinese-speaking users, leveraging a deceptive executable to infiltrate systems and compromise sensitive login credentials.
The malware employs a complex loading chain involving shellcode execution and legitimate system binaries to evade detection while establishing a firm foothold on the victim’s machine for long-term surveillance.
Upon execution, the fake installer triggers a multi-stage infection process designed to bypass endpoint security controls.
It immediately attempts to neutralize Windows Defender by using PowerShell commands to exclude entire system drives from antivirus scanning protocols.
.webp)
Simultaneously, it deploys a malicious library, identified as intel.dll, which performs rigorous environmental checks. These checks involve file locking and mutex creation to determine if the code is running within a sandbox.
If the environment is deemed safe, the malware unpacks its primary payload, effectively transforming the device into a fully compromised node.
Cybereason analysts identified this campaign and noted that the malware utilizes the advanced PoolParty Variant 7 injection technique.
This method allows the attackers to hide malicious activity within trusted system processes, significantly complicating detection.
By abusing Windows I/O completion ports, the malware injects code into legitimate processes, ensuring it can operate stealthily while harvesting user credentials and maintaining persistent communication with command-and-control servers.
Advanced Injection and Persistence Mechanisms
The technical complexity of this ValleyRAT variant is most evident in its evasion and persistence strategies.
The malware injects code into Explorer.exe and UserAccountBroker.exe, utilizing the latter process as a watchdog to ensure malicious components remain active.
This injection relies on manipulating system handles via specific Windows APIs like ZwSetIoCompletion, allowing the threat actors to execute code within the memory space of trusted processes.
Additionally, the malware actively scans for security products from vendors like Qihoo 360 and terminates their network connections to blind local defenses.
.webp)
To maintain persistence, the malware registers scheduled tasks via Remote Procedure Call (RPC) protocols, ensuring automatic execution upon user login.
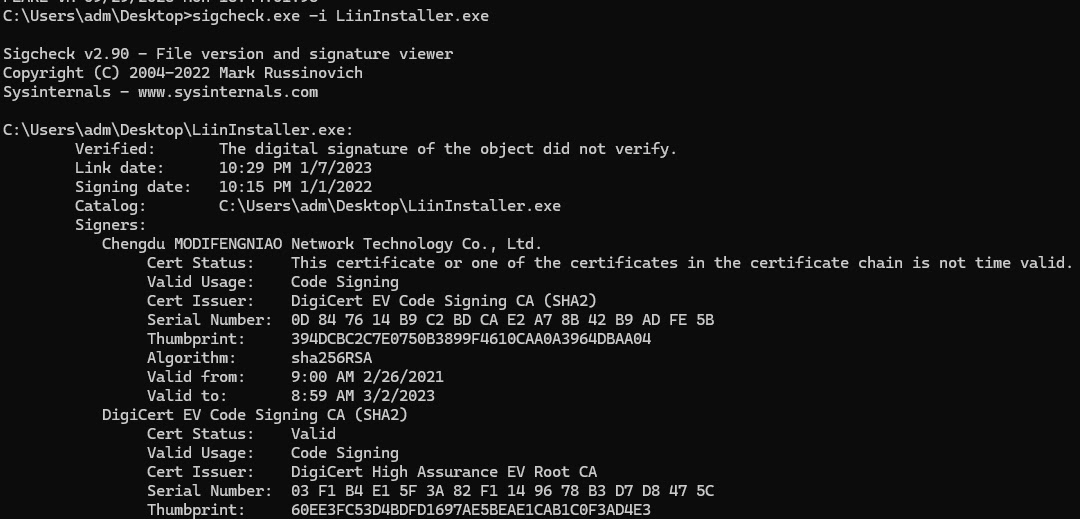
It also utilizes a digital certificate issued to “Chengdu MODIFENGNIAO Network Technology Co., Ltd” to appear legitimate, though the signature is cryptographically invalid.
To prevent infection, users must only download installers from official sources.
Security teams should configure detection rules to flag invalid certificates and monitor for suspicious child processes spawned by Explorer.exe, such as UserAccountBroker.exe, which indicates potential process hollowing activity.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.