Hackers Exfiltrating NTDS.dit File to Gain Full Active Directory
Active Directory serves as the indispensable backbone of enterprise authentication, securing critical data for user accounts, passwords, and domain configurations. Recently, security experts have...
Active Directory serves as the indispensable backbone of enterprise authentication, securing critical data for user accounts, passwords, and domain configurations.
Recently, security experts have observed a surge in attacks targeting the NTDS.dit database file, which contains encrypted password hashes for every domain account.
When attackers successfully steal this file, they gain the ability to crack passwords offline and potentially take over entire corporate networks.
This type of attack represents one of the most severe threats to Windows domain infrastructures, as it gives adversaries complete visibility into an organization’s identity framework.
The attack begins when hackers gain administrative access to a domain controller. Once inside, they use built-in Windows utilities like vssadmin to create Volume Shadow Copies, which allows them to bypass file locking mechanisms that normally protect the NTDS.dit database.
After creating the shadow copy, attackers extract the NTDS.dit file along with the SYSTEM registry hive, which contains the encryption keys needed to decrypt the password hashes.
Tools like PsExec enable remote execution of these commands, making the theft operation quick and efficient.
After the second stage of the attack, Trellix researchers identified sophisticated credential dumping techniques being deployed across multiple enterprise environments.
The security team observed attackers using tools such as SecretsDump and Mimikatz to process the stolen database files.
These credential extraction utilities can recover password hashes from the NTDS.dit file, enabling attackers to perform pass-the-hash attacks or crack the passwords entirely.
The stolen credentials provide unlimited access to domain resources, including sensitive data, financial systems, and administrative controls.
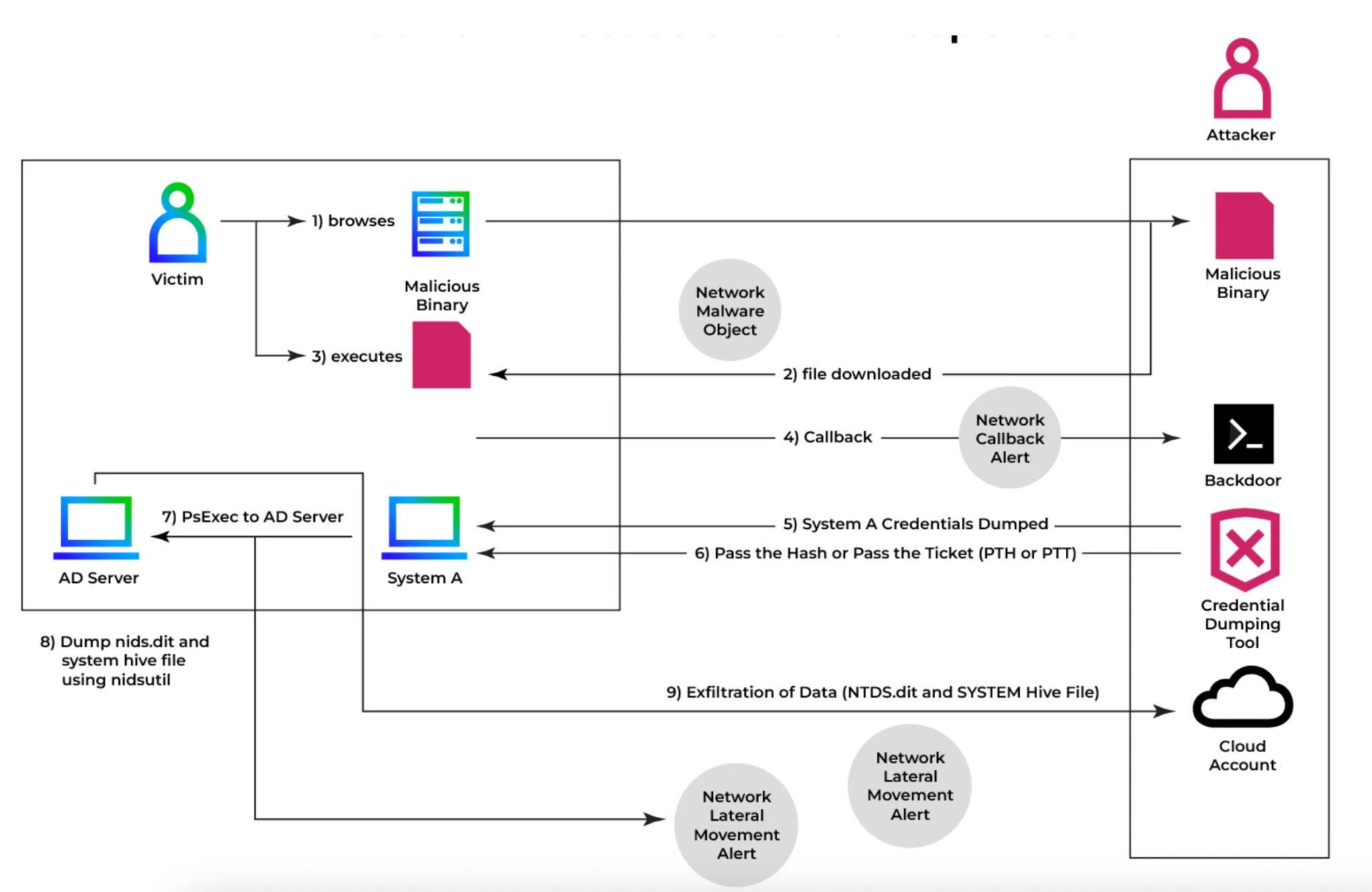
What makes this threat particularly dangerous is its stealth. Attackers often use legitimate administrative tools that blend in with normal network activity, making detection challenging for traditional security solutions.
The exfiltration process typically occurs over encrypted channels, further hiding the data theft from network monitoring tools. Organizations may not discover the breach until attackers have already established persistent access throughout the network.
NTDS.dit Exfiltration
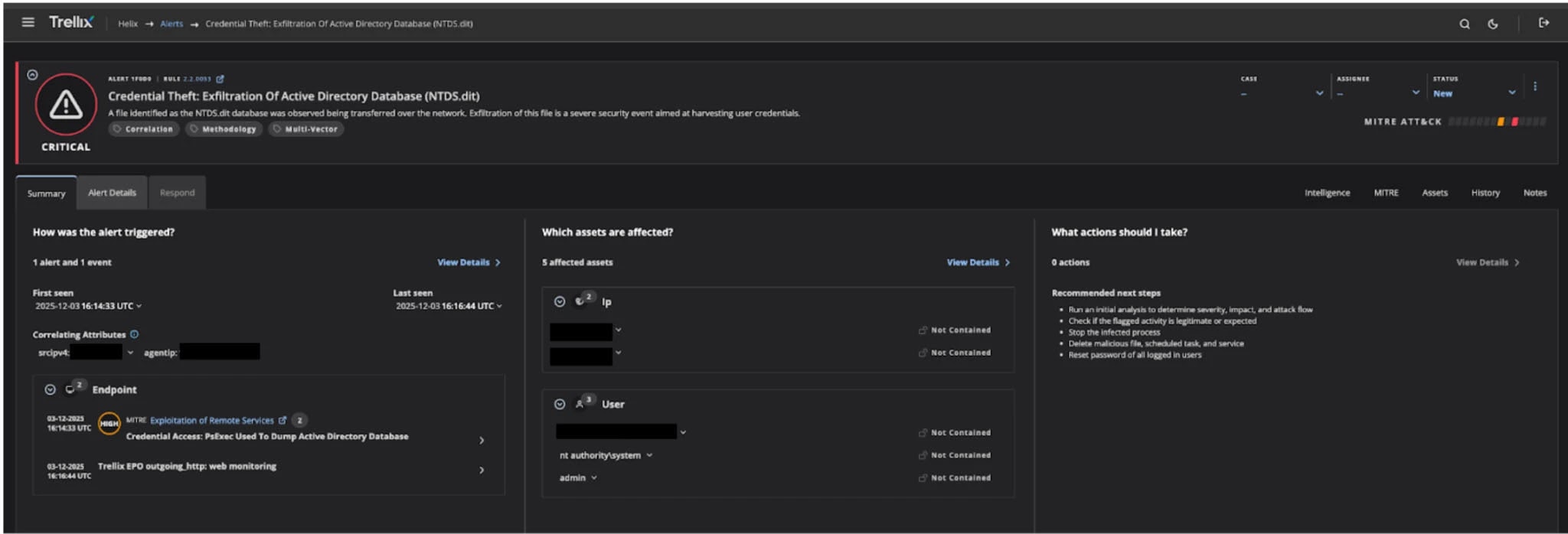
Trellix Helix provides advanced detection capabilities by correlating multiple security signals across endpoint, network, and cloud environments.
The platform automatically connects suspicious activities such as PsExec execution, Volume Shadow Copy creation, and unusual SMB file transfers into a single, coherent alert.
Unlike traditional security tools that generate isolated notifications, Helix builds a complete attack narrative by analyzing timestamps, IP addresses, and behavioral patterns.
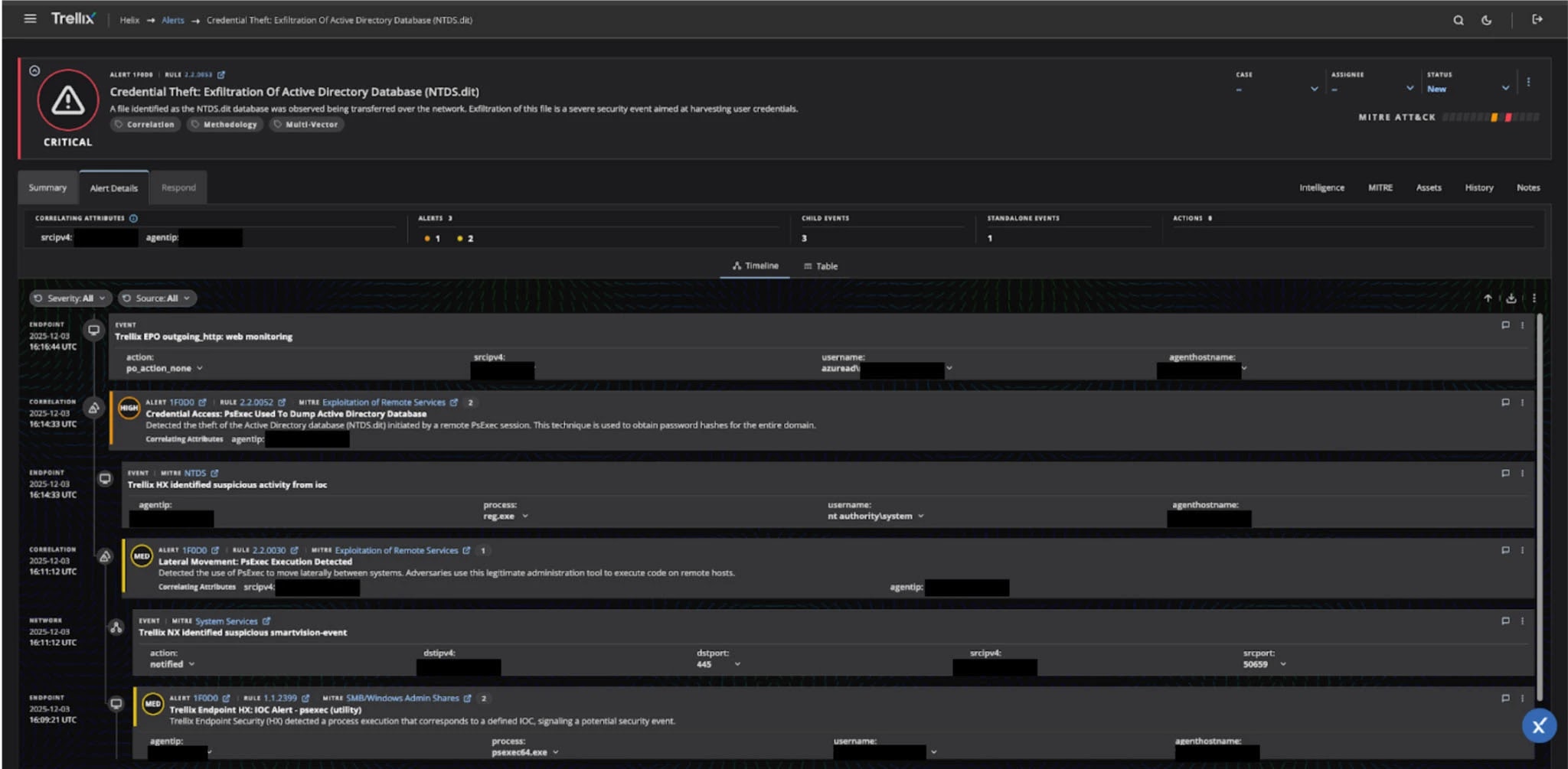
The system maps each detected activity to the MITRE ATT&CK framework, specifically identifying credential access techniques like T1003.003, which covers OS credential dumping from security account managers.
The Helix correlation engine tracks the entire attack chain from initial lateral movement through credential dumping and exfiltration attempts.
When the platform detects NTDS.dit file movement across the network, it triggers a critical severity alert titled “Credential Theft: Exfiltration Of Active Directory Database.”
This alert immediately identifies compromised systems, affected user accounts, and the scope of the breach.
Security teams receive actionable intelligence about which domain administrators and privileged accounts have been compromised, enabling rapid containment before attackers can leverage stolen credentials across the broader network environment.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.