GlassWorm Attacks Developers via 22K+ Infiltrated Extensions
Developers relying on the Open VSX Registry now face a serious new threat: GlassWorm. This campaign silently weaponizes popular VSX extensions, transforming them into delivery vehicles for malware....
Developers relying on the Open VSX Registry now face a serious new threat: GlassWorm. This campaign silently weaponizes popular VSX extensions, transforming them into delivery vehicles for malware.
Threat actors compromised a trusted publisher account and pushed poisoned updates that looked like routine releases but actually carried a staged loader.
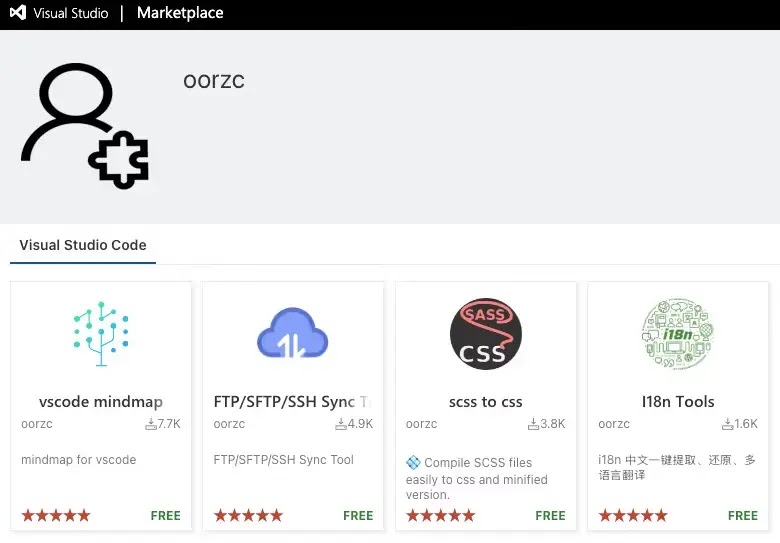
These extensions, which had more than 22,000 downloads, were widely adopted tools used for file sync, internationalization, mind mapping, and CSS workflows, turning everyday development tasks into potential entry points for attackers.
Socket.dev analysts identified this campaign as a developer-compromise supply chain attack, likely triggered by leaked publishing tokens or other unauthorized access to the oorzc publisher account.
Once the malicious versions were live, any developer who installed or updated the affected extensions risked pulling down the GlassWorm loader without any obvious warning.
The Open VSX security team later confirmed the compromise, removed the malicious releases, and revoked the publisher’s tokens, but the exposure window was long enough to raise serious concerns about stolen credentials and downstream abuse.
GlassWorm is not a new name in the ecosystem, but this wave marks a clear escalation in tradecraft.
Instead of relying on fake or cloned projects, the attackers hid inside real, long-standing extensions with a history of legitimate use.
The malware focuses heavily on macOS systems, where it steals browser data, cryptocurrency wallets, and sensitive files, while also going after developer material such as SSH keys, AWS credentials, and GitHub or npm tokens.
Simple theft to deep supply chain access
This shift from simple theft to deep supply chain access means one compromised laptop can quickly become a stepping stone into cloud environments and CI pipelines.
.webp)
This shows the oorzc namespace listing the four compromised extensions: FTP/SFTP/SSH Sync Tool, I18n Tools, vscode mindmap, and scss to css, all appearing completely benign to the average user.
This visual highlights how normal the extensions looked at the time of the attack, reinforcing how hard it is for developers to spot such threats by eye.
While this illustrates the staged execution chain that powers GlassWorm’s infection mechanism.
The first stage decrypts and runs an embedded payload, which then profiles the host, avoids Russian-locale systems, and retrieves its next command-and-control instructions from Solana transaction memos.
A final macOS-focused stage collects credentials, keychains, and documents, compresses them into an archive, and exfiltrates the data to attacker-controlled infrastructure, while a LaunchAgent entry ensures the malware survives reboots and continues to run in the background.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.