Hackers Exploit Microsoft Office 0-day Exploiting Vulnerability
A critical zero-day vulnerability in Microsoft Office is currently under active exploitation by the Russia-linked threat group UAC-0001, also known as APT28. The group is using this flaw to deploy...
A critical zero-day vulnerability in Microsoft Office is currently under active exploitation by the Russia-linked threat group UAC-0001, also known as APT28.
The group is using this flaw to deploy sophisticated malware against Ukrainian government entities and European Union organizations.
The vulnerability, identified as CVE-2026-21509, was disclosed by Microsoft on January 26, 2026, with warnings about active exploitation in the wild.
Within 24 hours of Microsoft’s public disclosure, threat actors had already weaponized the vulnerability.
Rapid Exploitation After Disclosure
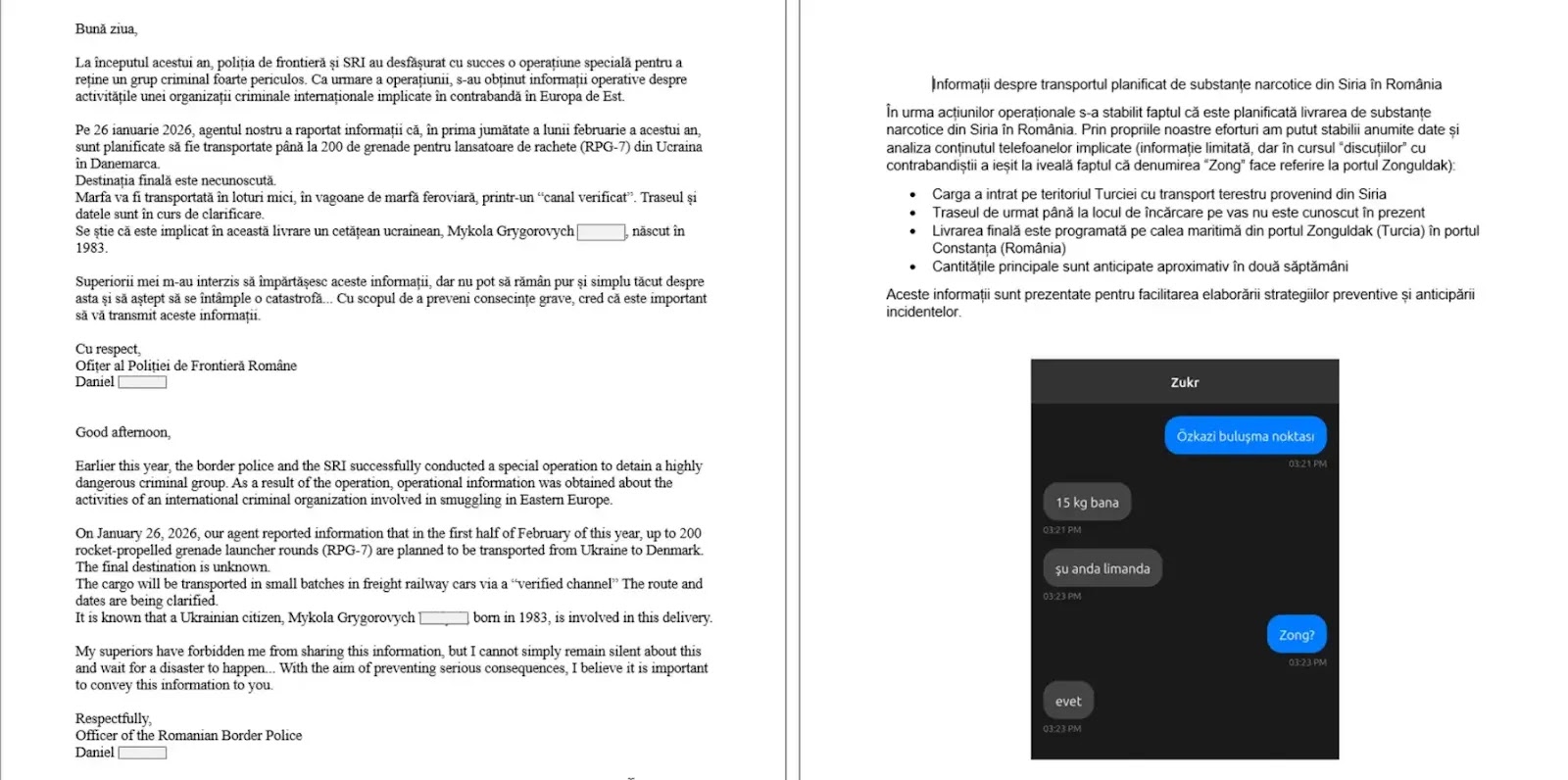
On January 27, 2026, security researchers discovered a malicious DOC file titled “Consultation_Topics_Ukraine(Final).doc” containing an exploit for CVE-2026-21509.
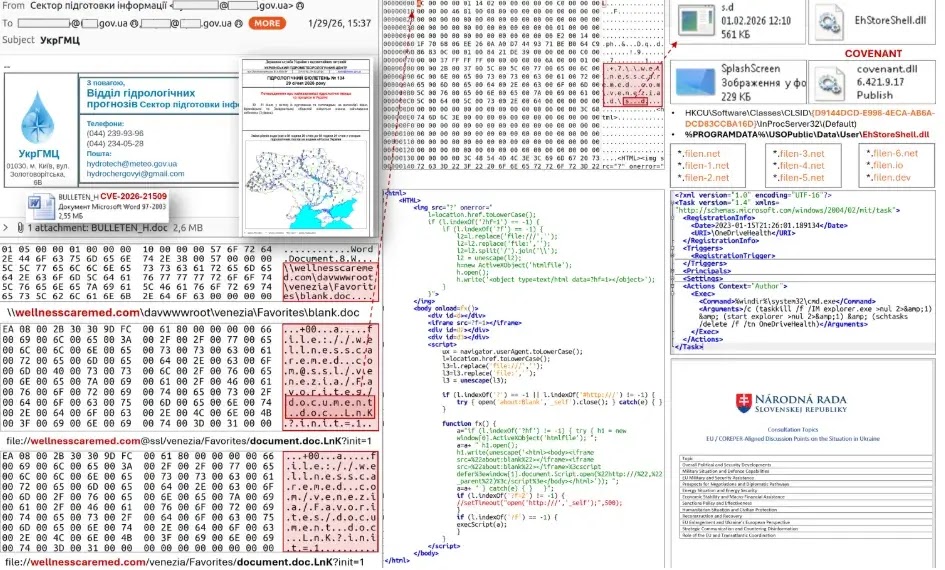
The document was themed around consultations of the Committee of Permanent Representatives to the EU (COREPER) regarding Ukraine, demonstrating the attackers’ use of geopolitically relevant social engineering tactics.
On January 29, 2026, the Ukrainian Computer Emergency Response Team (CERT-UA) detected a widespread phishing campaign distributing malicious documents purporting to be weather bulletins from the Ukrhydrometeorological Center.
The campaign targeted over 60 email addresses, primarily belonging to Ukrainian central executive bodies.
Attack Chain and Technical Details
When victims open the weaponized document in Microsoft Office, the exploit establishes a network connection to the attacker’s infrastructure via the WebDAV protocol.
The malware downloads a shortcut file containing executable code that deploys multiple malicious components, including “EhStoreShell.dll” and “SplashScreen.png”, containing shellcode.
The attack leverages COM hijacking techniques by modifying Windows registry entries and creates a scheduled task named “OneDriveHealth” for persistence.
The final payload is COVENANT, a sophisticated post-exploitation framework that uses legitimate Filen cloud storage (filen.io) for command-and-control communications.
This approach helps evade detection by blending malicious traffic with legitimate cloud service activity. Additional malicious documents targeting EU countries were discovered in late January 2026.
In one case, attackers registered attack infrastructure domain names on the same day as the attack, indicating rapid operational capabilities.
CERT-UA security experts warn that exploitation attempts are likely to increase due to slow patching cycles and users’ inability to update Microsoft Office installations promptly.
Organizations should immediately implement Microsoft’s recommended registry-based mitigations, monitor network connections to FileCloud storage infrastructure, and block identified indicators of compromise.
Users should exercise extreme caution when opening unsolicited Office documents, particularly those with geopolitical or administrative themes.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.