Arsink RAT Attacks Android: Exfiltrates Attacking Devices
Arsink RAT, a recently identified Android malware, poses a significant threat to mobile devices globally. This cloud-native Remote Access Trojan (RAT) grants attackers complete control over...
Arsink RAT, a recently identified Android malware, poses a significant threat to mobile devices globally. This cloud-native Remote Access Trojan (RAT) grants attackers complete control over compromised devices, enabling the stealthy exfiltration of personal information.
The malware spreads through social media platforms like Telegram, Discord, and file-sharing sites such as MediaFire, disguising itself as popular apps to trick users into installation.
Arsink operates by pretending to be legitimate applications from well-known brands including Google, YouTube, WhatsApp, Instagram, Facebook, and TikTok.
Attackers distribute fake “mod” or “pro” versions of these apps, convincing victims they are downloading enhanced features.
Once installed, the malware requests excessive permissions and begins its surveillance activities without providing any real functionality.
The threat affects users globally, with approximately 45,000 unique victim IP addresses identified across 143 countries.
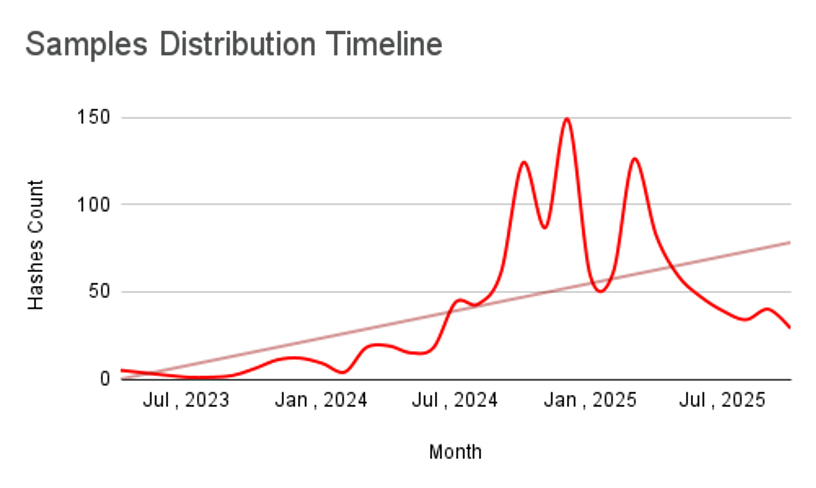
Zimperium analysts identified the malware campaign after tracking its rapid expansion over several months. The research team discovered 1,216 distinct malicious APK files and 317 Firebase Realtime Database endpoints used for command-and-control operations.
Most concerning is the scale of data theft occurring silently in the background. The malware captures SMS messages including one-time passwords, call logs, contacts, device location, and even audio recordings through the microphone.
The heaviest concentrations of infections appear in Egypt with roughly 13,000 compromised devices, followed by Indonesia with 7,000 cases, and Iraq and Yemen each reporting 3,000 infections.
Countries like Pakistan, India, and Bangladesh also show significant victim numbers, demonstrating the widespread nature of this threat.
Social Engineering Distribution Methods
Arsink’s distribution strategy relies heavily on social engineering techniques rather than technical exploits.
The attackers use multiple cloud services for different purposes, making detection more challenging. Some variants upload stolen files to Google Drive using Google Apps Script, while others send information directly to Telegram bots controlled by the attackers.
A third variant hides a secondary malicious payload inside the initial app, which gets extracted and installed without needing internet connectivity.
The malware maintains persistence on infected devices by hiding its app icon and running a foreground service that resists termination.
This allows continuous monitoring and data collection even when users think they have closed all apps.
Remote operators can trigger various actions including toggling the flashlight, making phone calls, uploading files, and even wiping all data from external storage as a destructive measure.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.