1-Click Clawdbot Flaw Allows Mal Vulnerability Enable
A critical vulnerability affecting OpenClaw, the open-source AI personal assistant widely adopted by over 100,000 developers, has been identified. This flaw has been weaponized into a devastating...
A critical vulnerability affecting OpenClaw, the open-source AI personal assistant widely adopted by over 100,000 developers, has been identified. This flaw has been weaponized into a devastating one-click remote code execution (RCE) exploit.
Security researchers at depthfirst General Security Intelligence uncovered a logic flaw that, when combined with other vulnerabilities, could trigger a chain reaction.
Allows attackers to gain complete control of victim systems via a single malicious link, requiring no user interaction.
Vulnerability Overview: Technical Attack Mechanics
OpenClaw’s architecture grants AI agents “god mode” access to messaging apps, API keys, and unrestricted control of the local computer.
While community enthusiasm surrounding the platform has driven rapid adoption, the security margin for error in such a high-privilege environment becomes razor-thin.
| Attribute | Details |
|---|---|
| Product | OpenClaw (formerly ClawdBot/Moltbot) |
| Vulnerability Type | Unsafe URL Parameter Handling + Cross-Site WebSocket Hijacking |
| Impact | Unauthenticated Remote Code Execution with System-Level Access |
| CVSS Score | Critical (9.8+) |
| Attack Vector | Network (Single Malicious Link) |
The newly disclosed vulnerability exploits three distinct components working in sequence: unsafe URL parameter ingestion, immediate gateway connection without validation, and automatic transmission of authentication tokens.
The exploitation chain begins with three seemingly benign operations occurring independently across the codebase.
The app-settings.ts module blindly accepts the gatewayUrl query parameter from the URL without validation, then stores it directly in localStorage.
Upon setting the application, the app-lifecycle.ts immediately triggers connectGateway(), which automatically bundles the security-sensitive authToken into the connection handshake to the attacker-controlled gateway server.
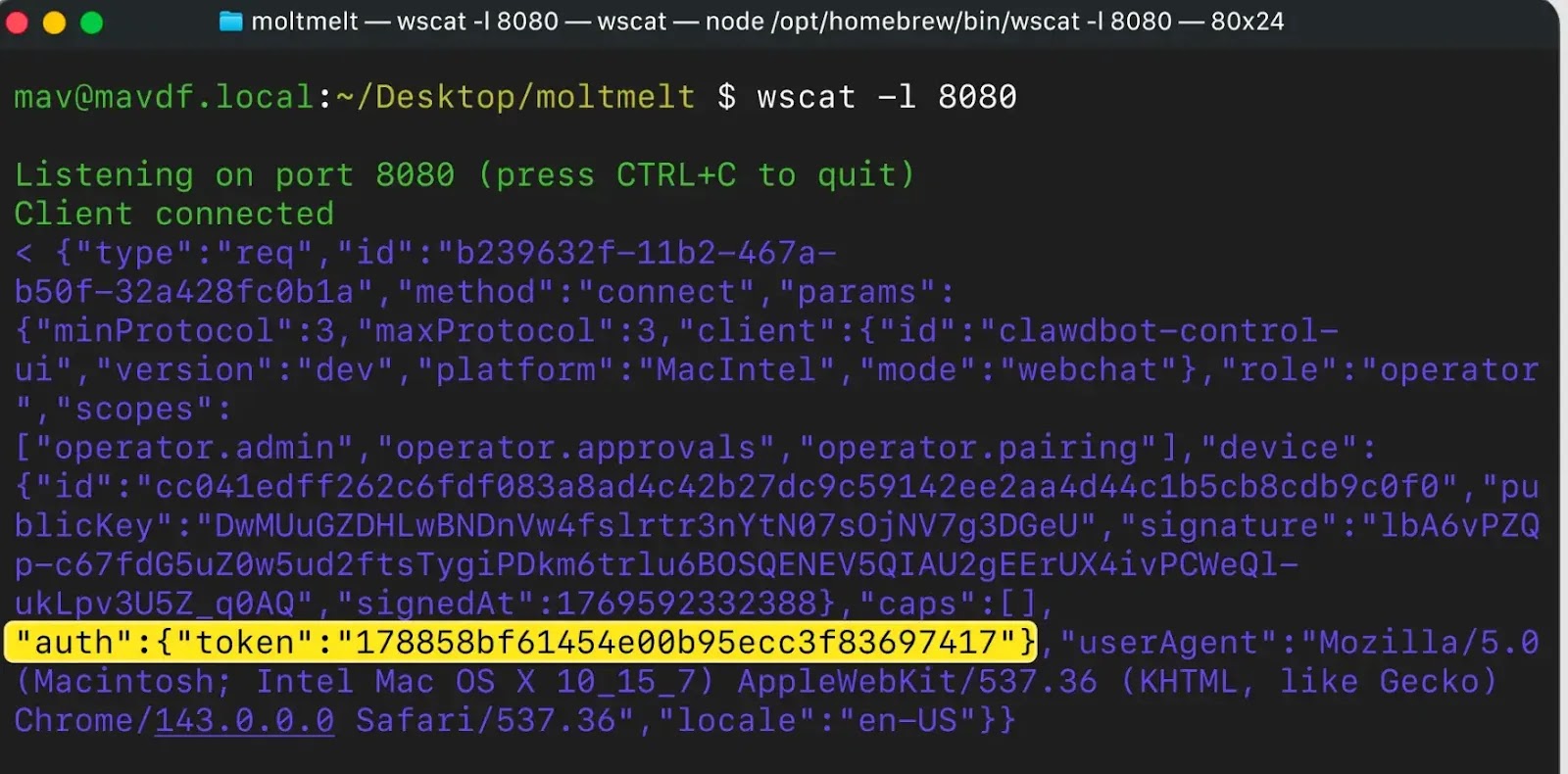
This pattern creates a critical information disclosure vulnerability. The kill chain exploits an additional WebSocket origin validation flaw.
| Stage | Description |
|---|---|
| Visit | User lands on malicious site. |
| Load | JS loads OpenClaw with malicious gatewayUrl. |
| Leak | authToken sent to attacker. |
| Connect | WebSocket opened to localhost. |
| Bypass | Safety guardrails disabled. |
| Execute | Attacker runs arbitrary commands. |
When victims visit a malicious webpage, attacker-injected JavaScript executes within their browser context, establishing a local connection to the victim’s OpenClaw instance running on localhost:18789.
Unlike standard HTTP connections, browser WebSocket implementations do not enforce Same-Origin Policy protections; instead, they rely on server-side origin header validation, which OpenClaw omits entirely.
This Cross-Site WebSocket Hijacking (CSWSH) enables the attacker to pivot through the victim’s browser as a proxy.
Once authenticated via the stolen token, the attacker leverages the operator. admin and operator roles. approvals, and scopes to turn off safety mechanisms.
An exec. approvals.set request turns off user confirmation prompts, while a config. patch request sets tools.exec.host to “gateway,” forcing command execution directly on the host machine rather than within containerized sandboxes.
The final payload invokes node. invoke with arbitrary bash commands, achieving complete system compromise.
Mitigations
The OpenClaw development team rapidly addressed the vulnerability by implementing a gateway URL confirmation modal, eliminating the auto-connect without prompt behavior that enabled the attack.
DepthFirst advises all users running versions before v2026.1.24-1 remain vulnerable and should upgrade immediately.
Administrators should rotate authentication tokens and audit command execution logs for suspicious activity.
This incident underscores the security risks inherent in granting AI agents unrestricted system access without robust validation of configuration changes and network connections.
Organizations deploying OpenClaw should implement additional network segmentation, restrict outbound WebSocket connections from AI agent processes, and maintain strict audit logging for authentication token usage and privilege modifications.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.