UAT-8099 Targets Vulnerable IIS Servers Using Web Shells,
A new wave of targeted attacks is underway, with threat actors deploying sophisticated malware against Internet Information Services (IIS) servers across Asia to compromise vulnerable systems. The...
A new wave of targeted attacks is underway, with threat actors deploying sophisticated malware against Internet Information Services (IIS) servers across Asia to compromise vulnerable systems.
The campaign, active from late 2025 through early 2026, focuses primarily on victims in Thailand and Vietnam, marking a strategic shift toward region-specific operations.
The attackers exploit unpatched IIS servers to inject malicious web shells, execute PowerShell scripts, and deploy the BadIIS malware, which now includes hardcoded regional configurations tailored to specific countries.
The threat campaign demonstrates operational overlap with the previously documented WEBJACK operation, sharing common indicators such as malware signatures, command and control infrastructure, and targeted victim profiles.
Attackers leverage web shells as their initial foothold, allowing them to execute commands remotely on compromised servers.
Following successful infiltration, they deploy PowerShell scripts to download and execute the GotoHTTP remote access tool, granting persistent control over infected systems.
This multi-stage infection chain enables threat actors to maintain long-term access while avoiding detection through the use of legitimate administrative tools.
Cisco Talos analysts identified the campaign after observing suspicious activity across multiple IIS deployments in South and Southeast Asia.
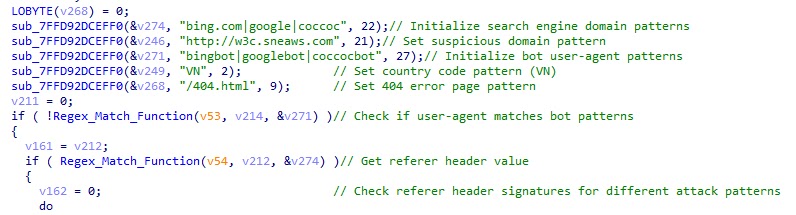
The researchers noted that BadIIS variants now embed country codes directly into their source code, creating specialized versions for Vietnam (identified by “VN” tags) and Thailand (marked with “TH” designations).
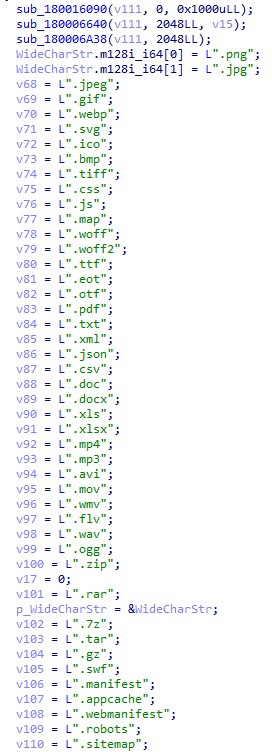
These customized variants include region-specific file extensions, dynamic page configurations, and localized HTML templates that facilitate search engine optimization fraud targeting specific language preferences.
The malware’s evolution reflects a more targeted approach compared to earlier versions. Each BadIIS variant filters web traffic based on the “Accept-Language” header to verify the visitor’s region before delivering malicious payloads.

When search engine crawlers visit infected sites, they are redirected to fraudulent gambling websites, while regular users receive injected JavaScript that silently redirects their browsers to malicious destinations.
Persistence Mechanisms and Hidden Account Creation
After establishing initial access, the threat actors create hidden user accounts to maintain persistent control over compromised servers.
The attackers initially used an account named “admin$” but shifted to alternative names like “mysql$,” “admin1$,” “admin2$,” and “power$” after security products began detecting the original naming pattern.
These accounts are assigned administrative privileges and used to deploy updated versions of BadIIS malware to specific regional directories such as “C:/Users/mssql$/Desktop/VN/” for Vietnam-targeted operations and “C:/Users/mssql$/Desktop/newth/” for Thailand-focused attacks.
The threat actors also deploy anti-forensic tools including Sharp4RemoveLog to erase Windows event logs, CnCrypt Protect to hide malicious files, and OpenArk64 to terminate security processes at the kernel level, ensuring their operations remain undetected for extended periods.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.