TA584 Uses ClickFix Social Engineering Actors Leveraging
Leveraging deceptive social engineering tactics, the sophisticated cybercriminal group TA584 has expanded its attack toolkit, now deploying new malware known as Tsundere Bot. This threat actor,...
Leveraging deceptive social engineering tactics, the sophisticated cybercriminal group TA584 has expanded its attack toolkit, now deploying new malware known as Tsundere Bot.
This threat actor, tracked as an initial access broker, has significantly intensified operations throughout 2025, with campaign volumes tripling between March and December.
The malware targets organizations globally through carefully crafted phishing emails that impersonate trusted brands and government agencies, tricking victims into executing malicious commands.
TA584 operates with remarkable speed and adaptability, launching multiple campaigns simultaneously while constantly rotating lures, infrastructure, and delivery methods.
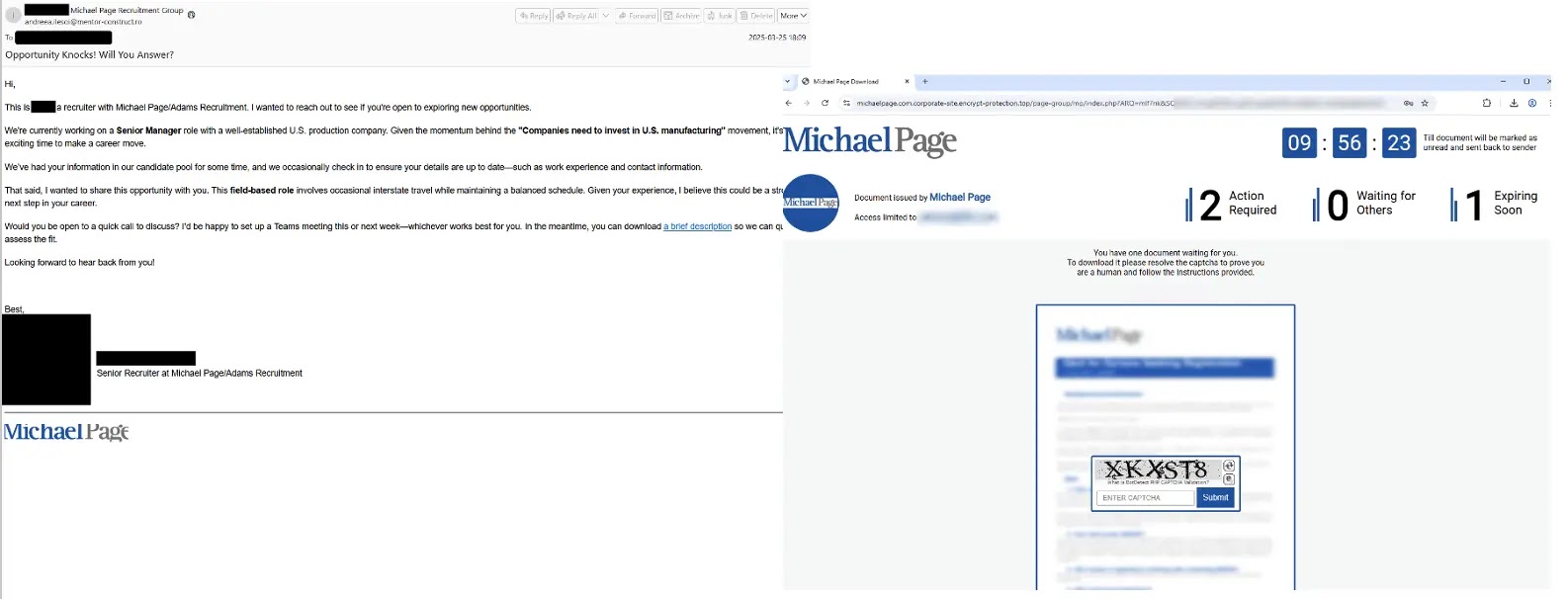
The threat actor sends emails from compromised accounts that appear legitimate, containing unique URLs designed to bypass security filters through geofencing and IP verification.
These messages often impersonate healthcare facilities, government entities, recruiting firms, and business services to establish credibility with potential targets.
Proofpoint analysts identified Tsundere Bot as a malware-as-a-service platform first delivered by TA584 in late November 2025. The malware represents a concerning evolution in threat delivery, combining backdoor capabilities with advanced evasion techniques.
Early campaign analysis revealed that infections could escalate to ransomware deployment, posing severe risks to enterprise networks.
The threat actor’s operational consistency since 2020, combined with connections to Russian cybercriminal markets, underscores the organized and persistent nature of these attacks.
The malware distinguishes itself through its use of blockchain technology for command-and-control communications, leveraging the Ethereum network via a technique called EtherHiding.
This approach retrieves configuration data from Web3 smart contracts, making detection and disruption significantly more challenging for security teams.
Tsundere Bot requires Node.js installation, which the malware handles automatically through PowerShell scripts generated from its control panel.
ClickFix Social Engineering Mechanism
TA584 employs the ClickFix technique to manipulate victims into executing malicious PowerShell commands on their own systems.
After recipients click embedded URLs and pass through multiple verification layers, they encounter a fake CAPTCHA verification page.
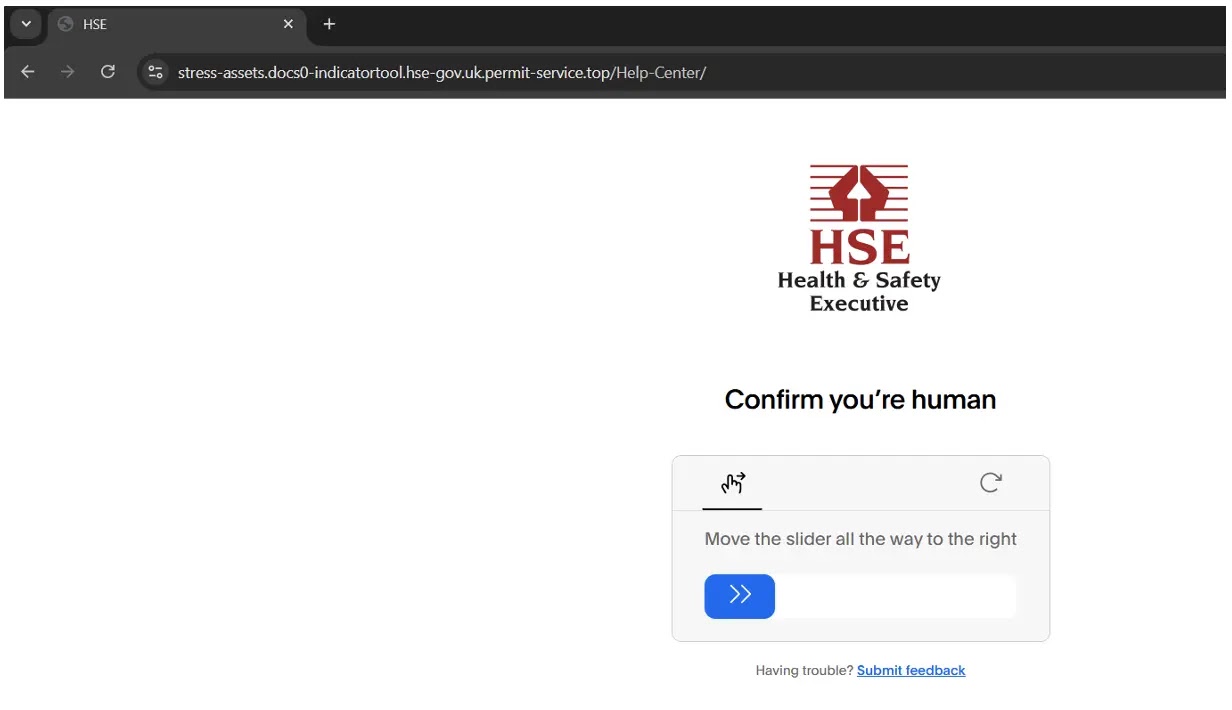
Upon solving the CAPTCHA, users are presented with fabricated error messages that instruct them to copy and paste specific commands into Windows Run dialog boxes.
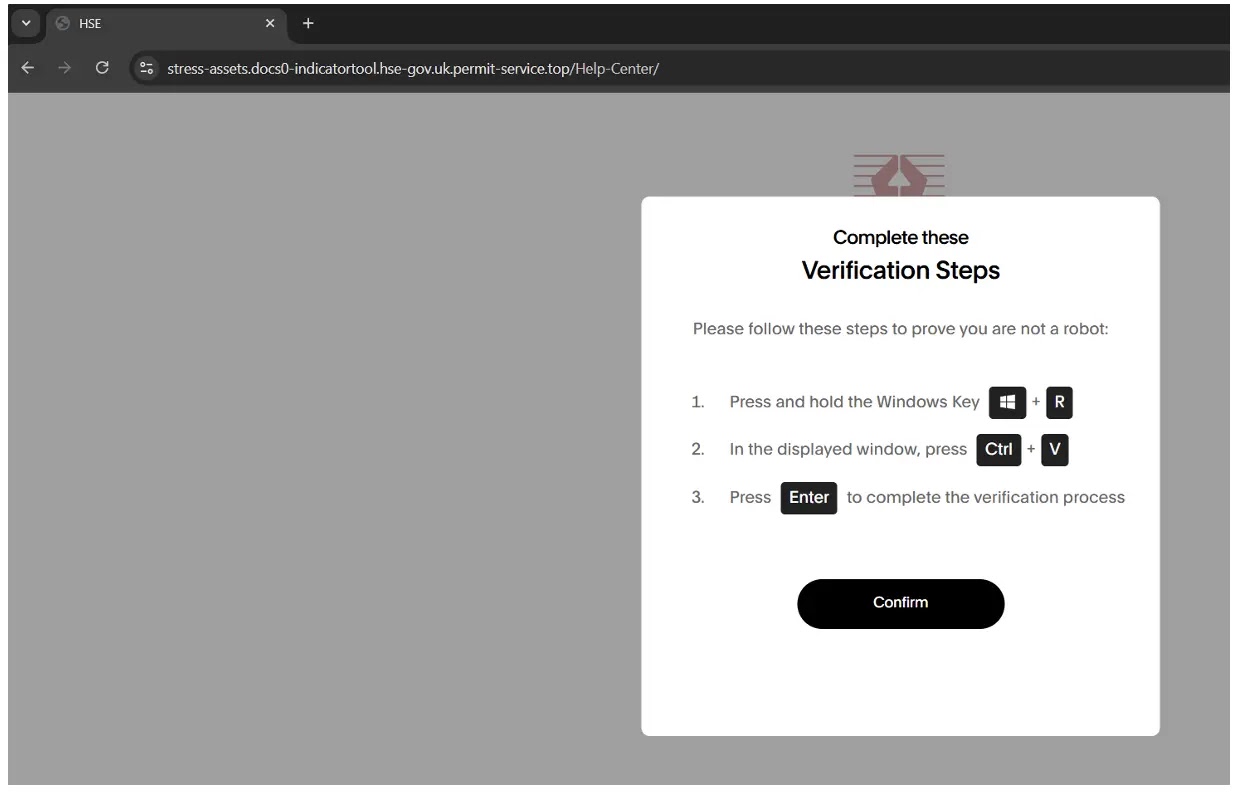
When victims follow these instructions, they unknowingly execute a PowerShell command that downloads and runs a remote script from attacker-controlled infrastructure.

This intermediate script installs Node.js and its dependencies directly from legitimate sources, then decrypts two AES-encrypted Node.js files embedded within the payload. The first file serves as a loader, which subsequently executes the second file containing Tsundere Bot itself.
The infection chain incorporates multiple anti-analysis features, including IP-based restrictions that prevent security researchers from retrieving payloads unless they access from the same address that viewed the landing page.
Once installed, Tsundere Bot connects to its command-and-control server at 193.17.183.126:3001, transmitting system profiling information and awaiting further instructions.
The malware includes geographic restrictions that prevent execution on systems using CIS country languages, suggesting operational boundaries aligned with Russian cybercriminal conventions.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.