31.4 Tbps DDoS Attack Via Aisuru Botnet Breaks Internet With New
The Aisuru/Kimwolf botnet launched the largest publicly disclosed distributed denial-of-service (DDoS) attack in history, peaking at an unprecedented 31.4 terabits per second (Tbps). The massive...
The Aisuru/Kimwolf botnet launched the largest publicly disclosed distributed denial-of-service (DDoS) attack in history, peaking at an unprecedented 31.4 terabits per second (Tbps).
Table Of Content
The massive attack, dubbed “The Night Before Christmas” campaign, targeted Cloudflare’s infrastructure and customers with hyper-volumetric attacks beginning December 19, 2025, combining Layer 4 DDoS attacks at record bandwidth alongside application-layer HTTP floods exceeding 200 million requests per second (rps).
The “Night Before Christmas” attack marked a significant escalation in the DDoS threat landscape, surpassing the previous record of 29.7 Tbps achieved by the same Aisuru botnet in September 2025.
The campaign leveraged compromised Android TV devices as attack sources, with threat actors exploiting millions of unofficial Android streaming boxes to generate unprecedented traffic volumes.
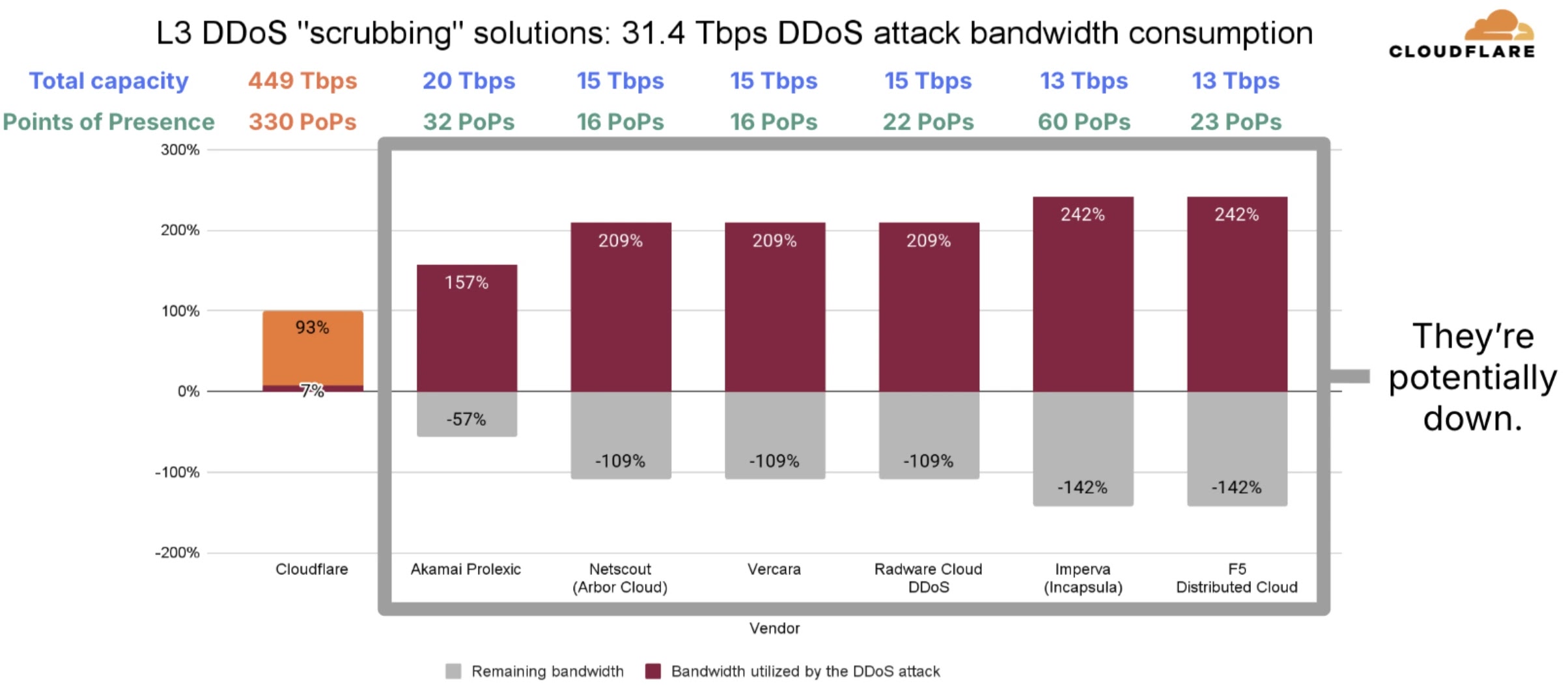
The 31.4 Tbps peak represents a scale that would have overwhelmed most DDoS mitigation providers, with competitor services like Akamai Prolexic (20 Tbps capacity), Netscout Arbor Cloud (15 Tbps), and Imperva (13 Tbps) facing theoretical bandwidth utilization rates exceeding 150-240%.
Attack Distribution and Characteristics
The hyper-volumetric assault consisted of thousands of individual attacks with distinct patterns that revealed sophisticated coordination by the botnet operators.
Analysis of the attack distribution showed that 90.3% of attacks peaked at 1-5 Tbps, 5.5% at 5-10 Tbps, and only 0.1% exceeded 30 Tbps. From a packet rate perspective, 94.5% of attacks generated between 1-5 billion packets per second (Bpps), with 4% peaking between 5-10 Bpps and 1.5% reaching 10-15 Bpps.
Attack duration patterns demonstrated a preference for short, intense bursts designed to overwhelm defenses before triggering mitigation responses. Only 9.7% of attacks lasted under 30 seconds, while 27.1% sustained for 30-60 seconds, and a majority of 57.2% persisted between 60-120 seconds.
Merely 6% of attacks exceeded two minutes in duration, suggesting the botnet operators optimized for rapid-fire volleys rather than sustained campaigns.
The campaign demonstrated clear strategic targeting of critical infrastructure and high-value sectors. Gaming companies bore the brunt of the attacks, accounting for 42.5% of hyper-volumetric attacks, followed by Information Technology and Services organizations at 15.3%.

Telecommunications providers represented 2.2% of targets, while Internet service providers, gambling operations, and computer software firms comprised the remaining top-tier targets.
Geographic distribution revealed concentrated attacks against major internet hubs and economic centers. The United States absorbed 30.8% of all hyper-volumetric network-layer attacks, making it the primary target, while China faced 7.7% and Hong Kong received 3.2%.
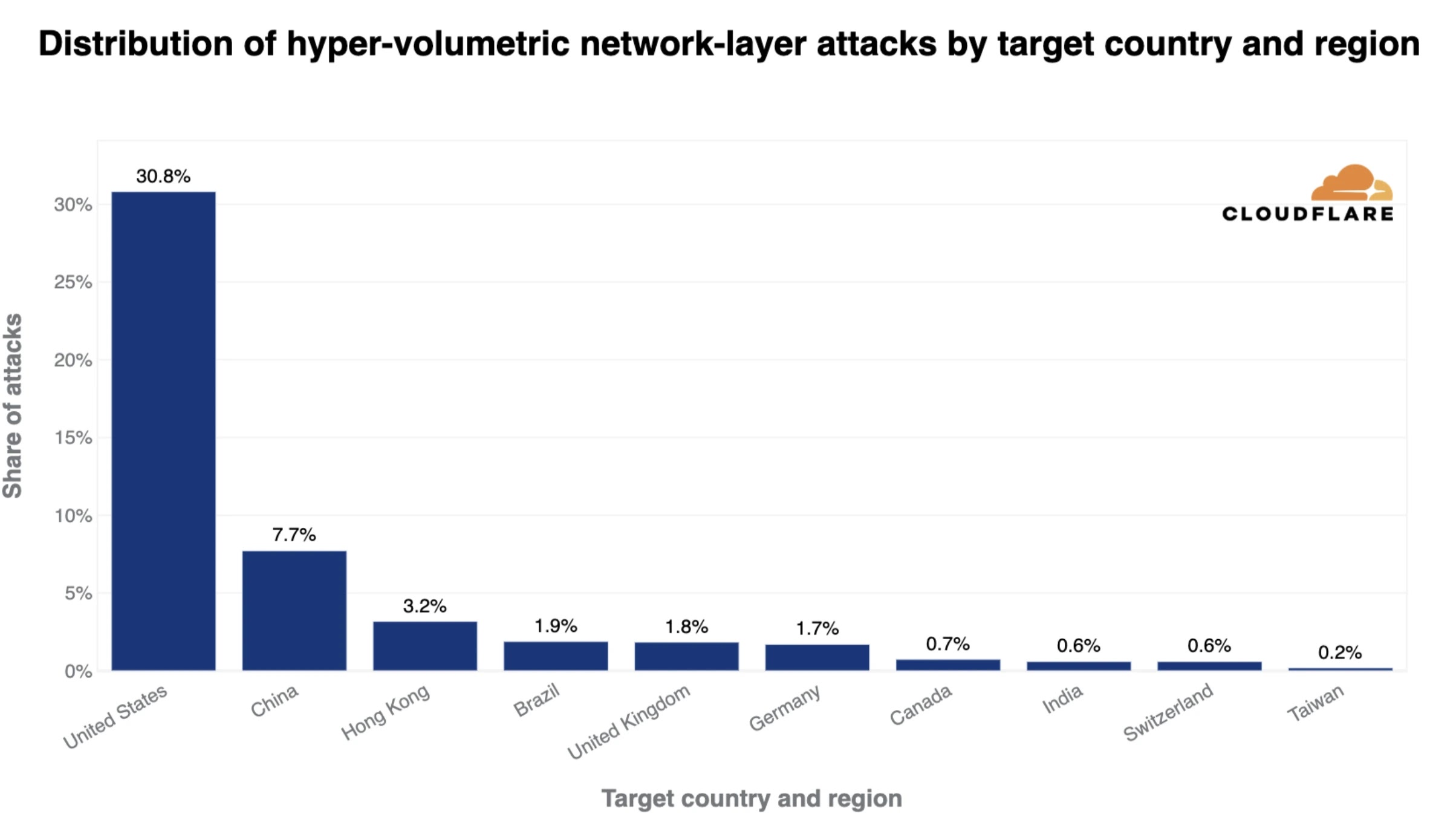
Brazil (1.9%), the United Kingdom (1.8%), Germany (1.7%), Canada (0.7%), India (0.6%), Switzerland (0.6%), and Taiwan (0.2%) rounded out the top-10 most-targeted countries.
Aisuru/Kimwolf Botnet Evolution
The Aisuru botnet has evolved into one of the most formidable DDoS threats in modern internet history, with its Android-focused variant, Kimwolf, splintering off in August 2025. Security researchers at Synthient documented that Kimwolf infected over 2 million unofficial Android TV devices, exploiting residential proxy networks to establish a distributed command-and-control infrastructure.
The botnet gained widespread attention in October 2025 when it temporarily claimed the top position in Cloudflare’s global domain rankings through massive traffic generation.
Lumen Technologies’ Black Lotus Labs has been actively disrupting the botnet’s operations since early October 2025, null-routing traffic to more than 550 command-and-control servers associated with both Aisuru and Kimwolf infrastructure.
Despite these mitigation efforts, the botnet demonstrated resilience by rapidly shifting C2 nodes to new infrastructure, particularly leveraging Resi Rack LLC IP addresses and common autonomous system numbers (ASNs).
The record-breaking attack occurred against a backdrop of explosive growth in DDoS attacks throughout 2025. The total number of DDoS attacks more than doubled to 47.1 million in 2025, up 121% from 21.3 million in 2024 and 236% from 14 million in 2023. Cloudflare’s systems mitigated an average of 5,376 DDoS attacks every hour during 2025, comprising 3,925 network-layer attacks and 1,451 HTTP DDoS attacks.
Network-layer DDoS attacks drove the majority of this growth, more than tripling year-over-year from 11.4 million in 2024 to 34.4 million in 2025. The fourth quarter alone saw 8.5 million network-layer attacks, representing a 152% year-over-year increase and 43% quarter-over-quarter growth, with these attacks accounting for 78% of all DDoS activity in Q4 2025.
The threat landscape demonstrated concerning trends in attack sophistication and scale. Network-layer attacks exceeding 100 million packets per second (Mpps) surged by 600%, while attacks exceeding 1 Tbps increased 65% quarter-over-quarter. Nearly one in 100 network-layer DDoS attacks exceeded 1 Mpps, indicating a shift toward higher-intensity attack patterns.
On the application layer, known DDoS botnets accounted for 71.5% of all HTTP DDoS attacks, with suspicious HTTP attributes accounting for 18.8%, fake or headless browsers for 5.8%, and generic floods for 1.8%.
Attack duration analysis revealed that 78.9% of HTTP DDoS attacks concluded within 10 minutes, demonstrating a preference for rapid attack cycles.
Attack magnitude distribution showed that 69.4% of HTTP DDoS attacks remained under 50,000 requests per second, while 2.8% exceeded 1 million rps, meaning approximately three out of every 100 HTTP attacks qualified as hyper-volumetric.
Cloudflare’s new real-time botnet detection system successfully identified and mitigated over 50% of HTTP DDoS attacks automatically without human intervention.
Attack Infrastructure Sources
The global attack source distribution revealed significant shifts in the geographic origins of malicious traffic during Q4 2025. Bangladesh emerged as the largest source of DDoS attacks, dethroning Indonesia, which had held the top position for the previous year, and dropped to third place. Ecuador ranked second, while Argentina rose 20 places to become the fourth-largest source.
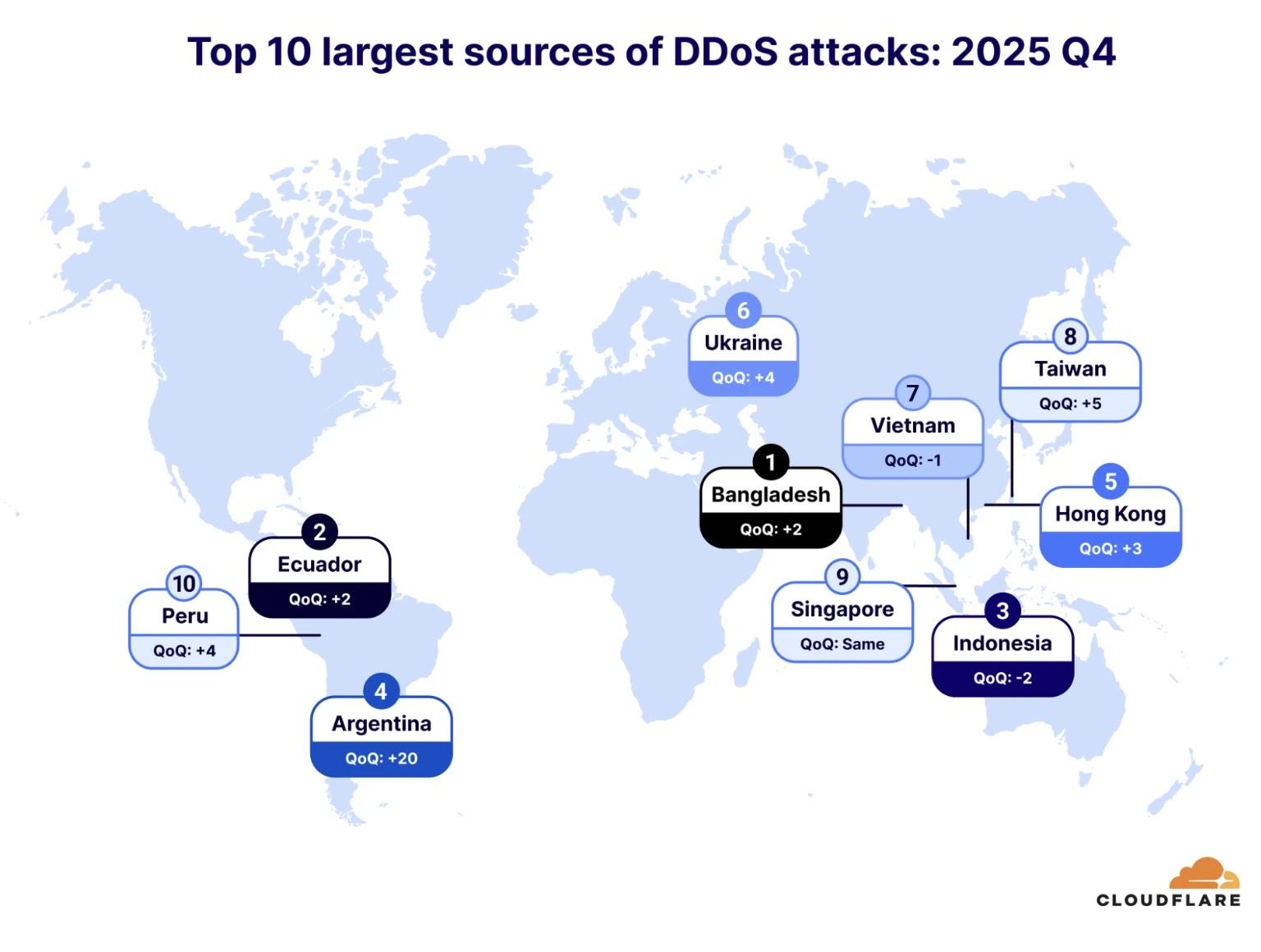
Other significant attack sources included Hong Kong (5th), Ukraine (6th), Vietnam (7th), Taiwan (8th), Singapore (9th), and Peru (10th). Russia experienced a notable decline, dropping five ranks to tenth place, while the United States fell four positions to sixth.
Analysis of attack source networks revealed that threat actors primarily exploited cloud computing platforms and telecommunications infrastructure.
Cloud providers, including DigitalOcean (AS 14061), Microsoft (AS 8075), Tencent, Oracle, and Hetzner, dominated as attack sources, representing half of the top 10 source networks and demonstrating the exploitation of easily-provisioned virtual machines for high-volume attacks.
Traditional telecommunications providers from the Asia-Pacific region, particularly Vietnam, China, Malaysia, and Taiwan, comprised the remaining top-tier sources.
Despite the unprecedented scale of the “Night Before Christmas” campaign, Cloudflare’s infrastructure demonstrated resilience with its 449 Tbps total mitigation capacity across 330 points of presence (PoPs).
The 31.4 Tbps attack consumed only 7% of Cloudflare’s available bandwidth, leaving 93% remaining capacity. The automated detection and mitigation systems successfully neutralized the hyper-volumetric attacks without triggering internal alerts or requiring human intervention, highlighting the effectiveness of machine-learning-based defense mechanisms.
The campaign underscores the critical importance of massive-scale DDoS mitigation infrastructure as attack volumes continue their exponential growth trajectory.
Organizations relying on providers with limited capacity face existential risks, as the attack would have theoretically exceeded the total mitigation capacity of multiple competing services simultaneously.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.