eSkimming Attacks: Persistent Threats & Unfinished Recovery
E-commerce websites globally face an ongoing threat from eSkimming attacks, widely recognized as Magecart. These persistent compromises target customer payment card data, illicitly acquiring it...
E-commerce websites globally face an ongoing threat from eSkimming attacks, widely recognized as Magecart. These persistent compromises target customer payment card data, illicitly acquiring it during the checkout process.
These malicious campaigns inject JavaScript code into compromised websites, capturing sensitive financial information as users complete their purchases.
Unlike traditional malware that requires system access, eSkimming operates entirely within the browser environment, making it especially difficult to detect and remove completely.
The attack has become increasingly sophisticated as threat actors refine their techniques to evade security defenses and maintain persistent access long after initial detection.
The emergence of eSkimming as a widespread threat coincided with the rise of third-party script dependencies on modern websites.
Attackers exploit these supply chain vulnerabilities by compromising payment processing services, analytics providers, and customer support platforms.
Once a malicious script is injected, it silently captures form data and payment credentials before sending them to attacker-controlled servers.
The attack’s scope extends beyond major retailers—small and medium-sized businesses remain equally vulnerable, often lacking the resources to implement robust client-side security controls.
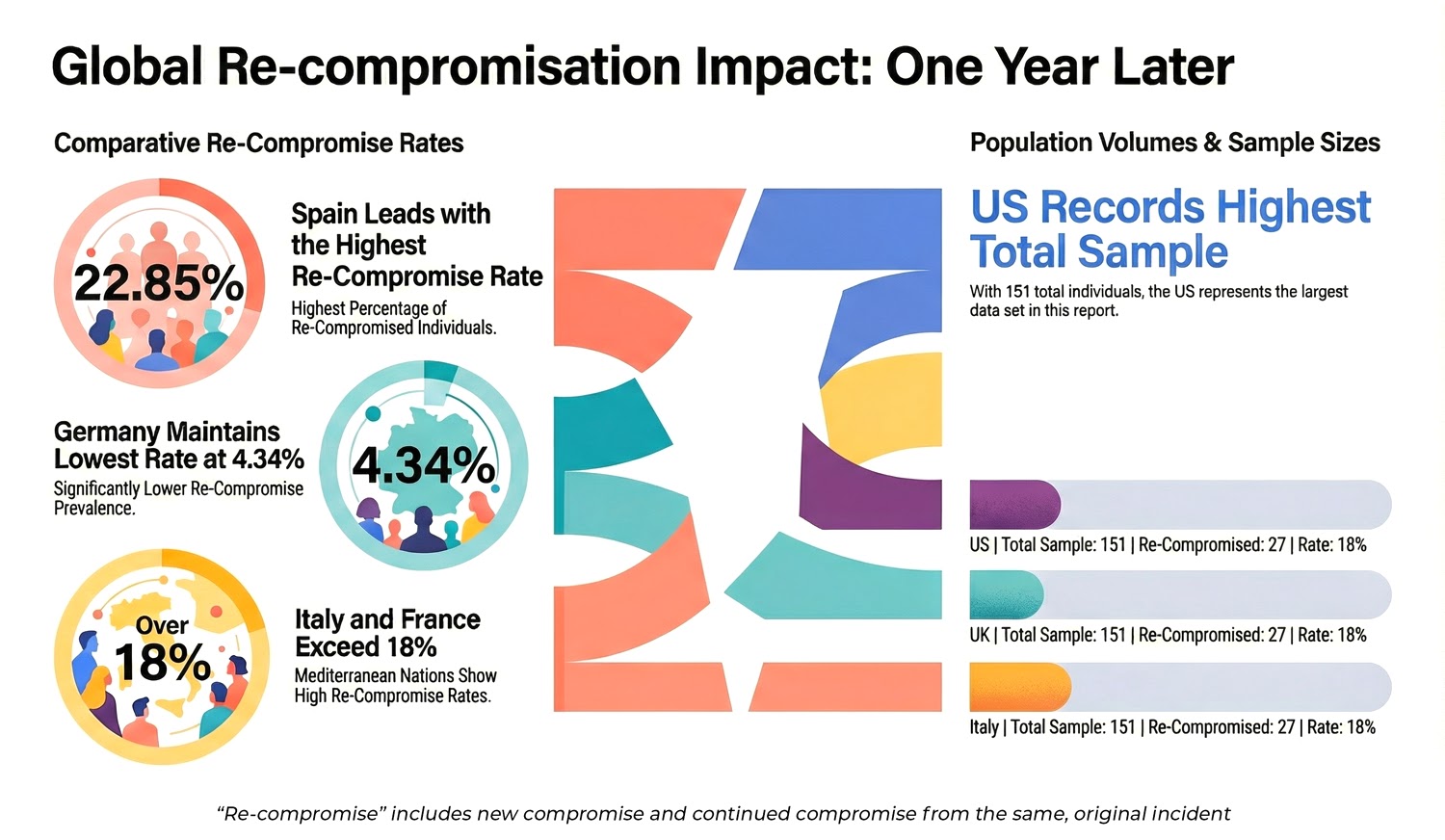
Source Defense analysts identified critical persistence patterns through a year-long study of 550 previously compromised e-commerce websites across 68 countries that fundamentally challenged conventional recovery assumptions.
Their research revealed that eighteen percent of previously infected sites remained actively compromised one year after initial detection.
Among those persistent infections, fifty-seven percent involved new or evolved attack paths rather than simple leftover code, indicating active adversary adaptation rather than passive residual threats.
Attacker Pivot Tactics: Moving Between Payment Processing Layers
The most concerning discovery was how attackers shifted between first-party and third-party scripts during remediation cycles.
When organizations removed the visible skimmer without addressing underlying vulnerabilities, attackers returned through different vectors.
Twelve percent of campaigns evolved from third-party execution into first-party JavaScript, embedding deeper into website core logic where traditional security controls proved ineffective.
This adaptation strategy reveals that attackers actively monitor defensive responses and deliberately seek harder-to-detect injection points.
The structural weakness lies in the browser blind spot. Most security tools focus on server-side protection—firewalls, content security policies, and code scanners—leaving client-side threats largely unmonitored.
Point-in-time cleanup removes visible malware but cannot prevent re-infection without continuous runtime visibility.
Organizations require real-time browser monitoring to detect unauthorized script behavior, block suspicious data access, and enforce controls before exfiltration occurs. Without addressing this gap, eSkimming persistence will remain the norm rather than the exception.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.