HoneyMyte Updates CoolClient Malware to Steal Browser Data
Also known as Mustang Panda or Bronze President, the HoneyMyte threat group continues to pose a significant risk to government organizations across Asia and Europe. Recent security research has...
Also known as Mustang Panda or Bronze President, the HoneyMyte threat group continues to pose a significant risk to government organizations across Asia and Europe.
Recent security research has revealed that this advanced hacker collective is actively upgrading its digital arsenal with enhanced versions of malware designed to steal sensitive information from targeted systems.
The group’s operations have been particularly concentrated in Southeast Asia, where government agencies remain the primary targets of their sophisticated campaigns.
In 2025, security experts discovered that HoneyMyte significantly expanded its toolset by improving the CoolClient backdoor malware with new capabilities.
Beyond the CoolClient upgrades, the group deployed several variants of a specialized browser login data stealer and utilized multiple scripts intended for harvesting confidential documents and gathering system details.
This evolution demonstrates the group’s commitment to developing more effective tools for extracting valuable data from compromised networks.
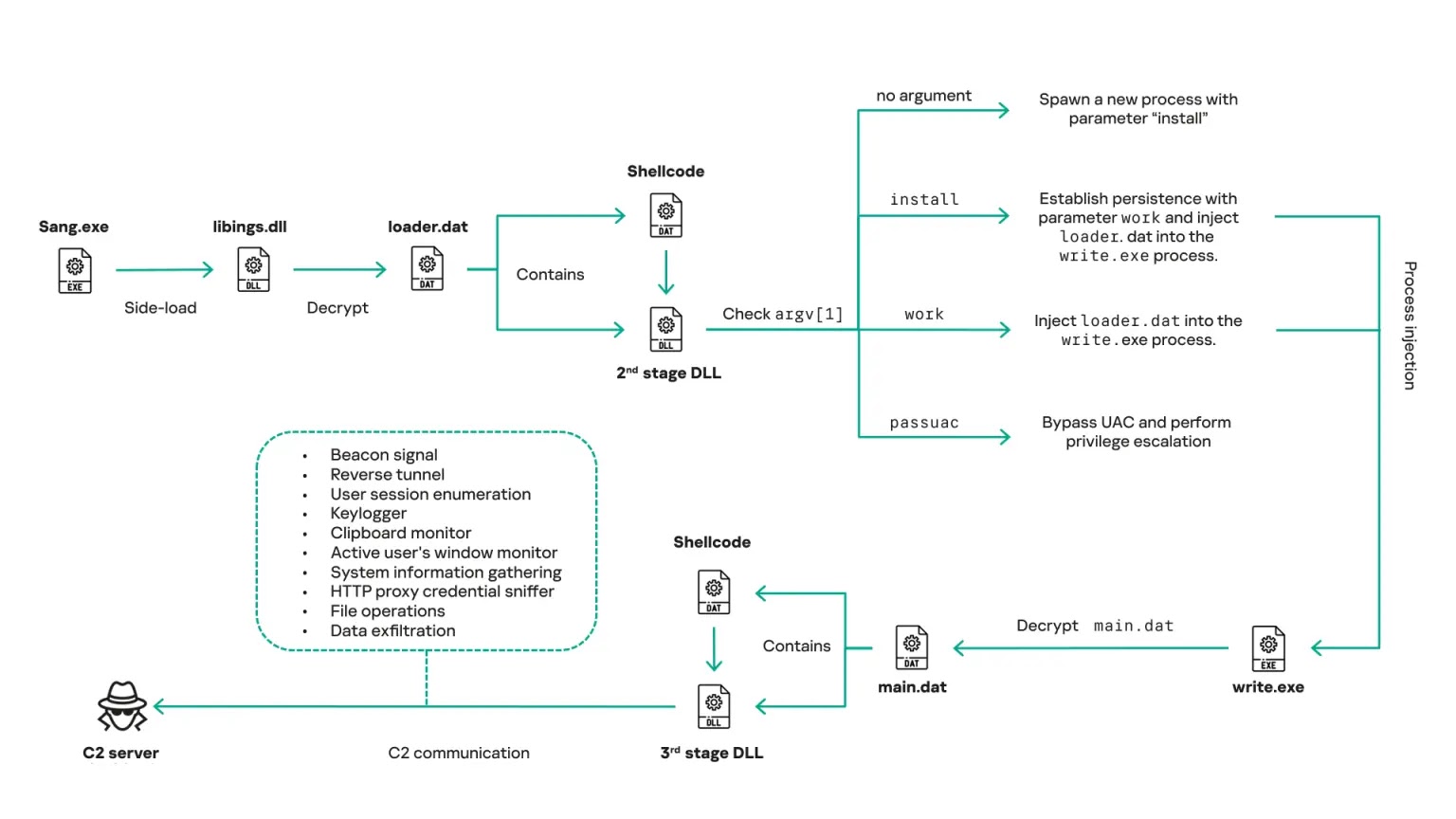
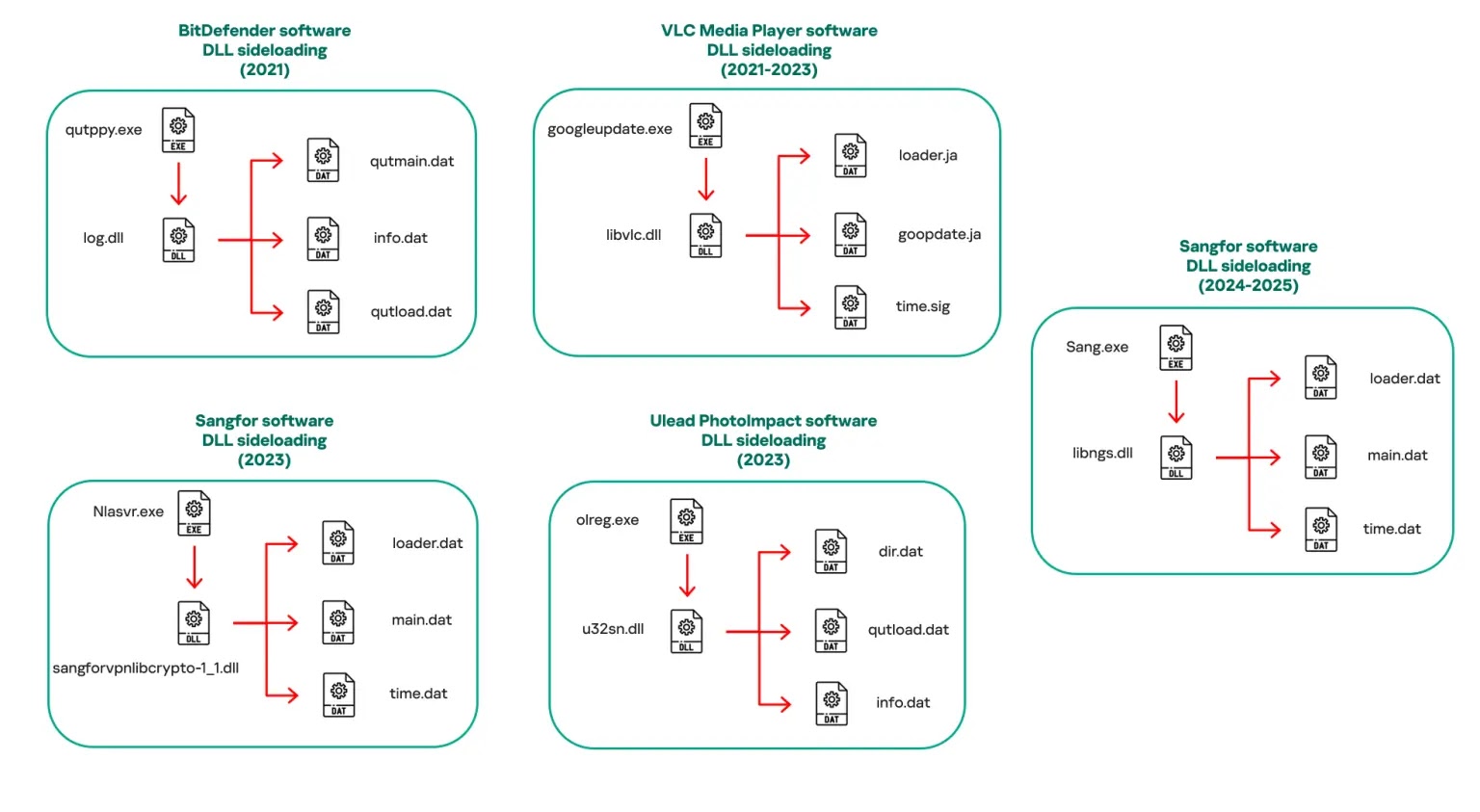
Securelist analysts noted that the malware operates through a multi-stage delivery system that relies on DLL sideloading, a technique where legitimate software files are hijacked to load malicious code.
The malware has been observed in countries including Myanmar, Mongolia, Malaysia, Russia, and Pakistan.
Between 2021 and 2025, HoneyMyte abused legitimate applications from vendors such as BitDefender, VLC Media Player, and Sangfor to execute its malicious payload.
The Browser Credential Stealer and Detection Evasion
One of the most concerning developments involves HoneyMyte’s new browser credential stealer, which specifically targets login information stored in popular web browsers.
The group deployed at least three variants of this stealer across different campaigns. Variant A targets Google Chrome, Variant B focuses on Microsoft Edge, and Variant C supports multiple Chromium-based browsers including Brave and Opera.
This flexibility allows attackers to harvest credentials regardless of which browser users prefer on compromised machines.
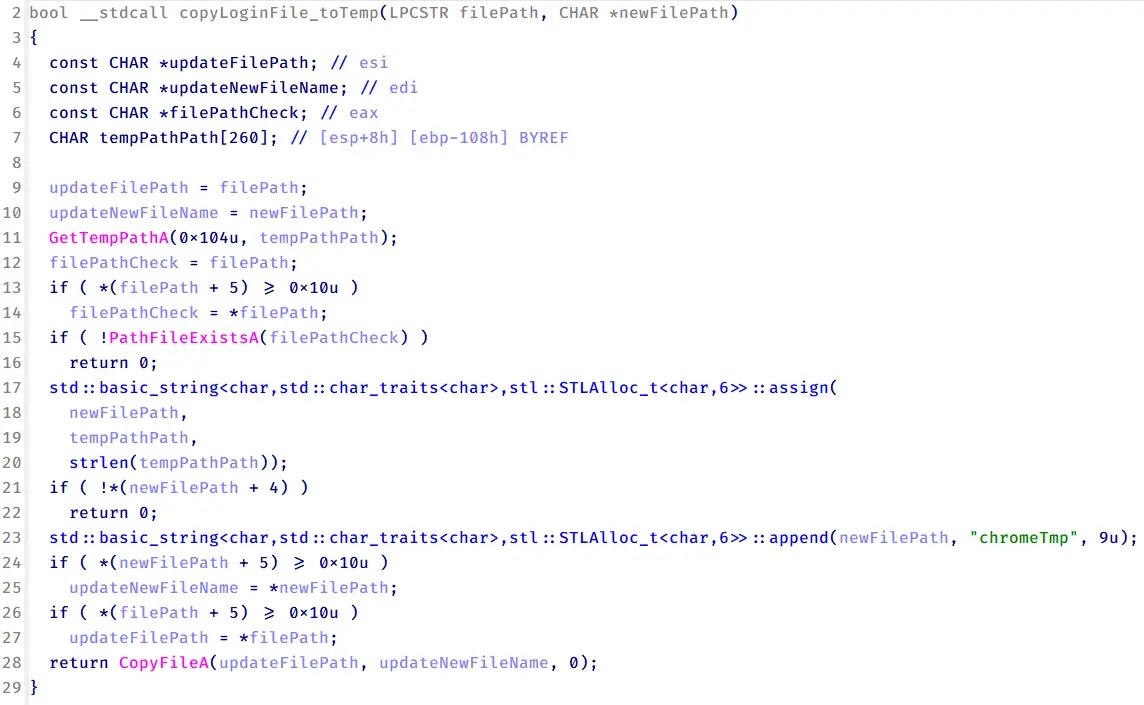
The stealer operates by copying the target browser’s login database and configuration files to temporary folders, then using Windows security features to decrypt stored passwords.
The malware extracts encrypted master keys from browser files, decrypts them using Windows Data Protection Application Programming Interface functions, and reconstructs complete login records containing usernames and passwords.
After gathering this sensitive information, the malware saves the harvested credentials to hidden system folders for later exfiltration to attacker-controlled servers.
This capability, combined with other features like keylogging and clipboard monitoring, reveals HoneyMyte’s transition toward active surveillance of victim systems beyond traditional espionage objectives.
Organizations operating in government sectors should implement strong detection measures and maintain vigilant monitoring for signs of CoolClient backdoor infections, browser stealer activity, and related malware families used by this determined threat actor.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.