Phishing Attack Leverages Vercel to Deliver Remote Access
A sophisticated phishing campaign, active between November 2025 and January 2026, has been exploiting Vercel’s legitimate hosting platform to distribute remote access tools to unsuspecting victims....
A sophisticated phishing campaign, active between November 2025 and January 2026, has been exploiting Vercel’s legitimate hosting platform to distribute remote access tools to unsuspecting victims.
The attack chain combines social engineering with trusted domain exploitation, making it particularly effective at bypassing traditional security layers.
Attackers craft phishing emails using financially themed lures such as overdue invoices, payment statements, and shipping documents to pressure users into clicking malicious links.
The campaign demonstrates a shift in threat actor tactics, moving beyond simple malware delivery to implement advanced evasion techniques.
Victims receive emails containing urgency-driven language like “43 days past due” or threats of service suspension, compelling them to interact with hyperlinked content.
The attacker relies on Vercel’s reputation as a trusted platform, which naturally bypasses email filters and creates a false sense of security for recipients.
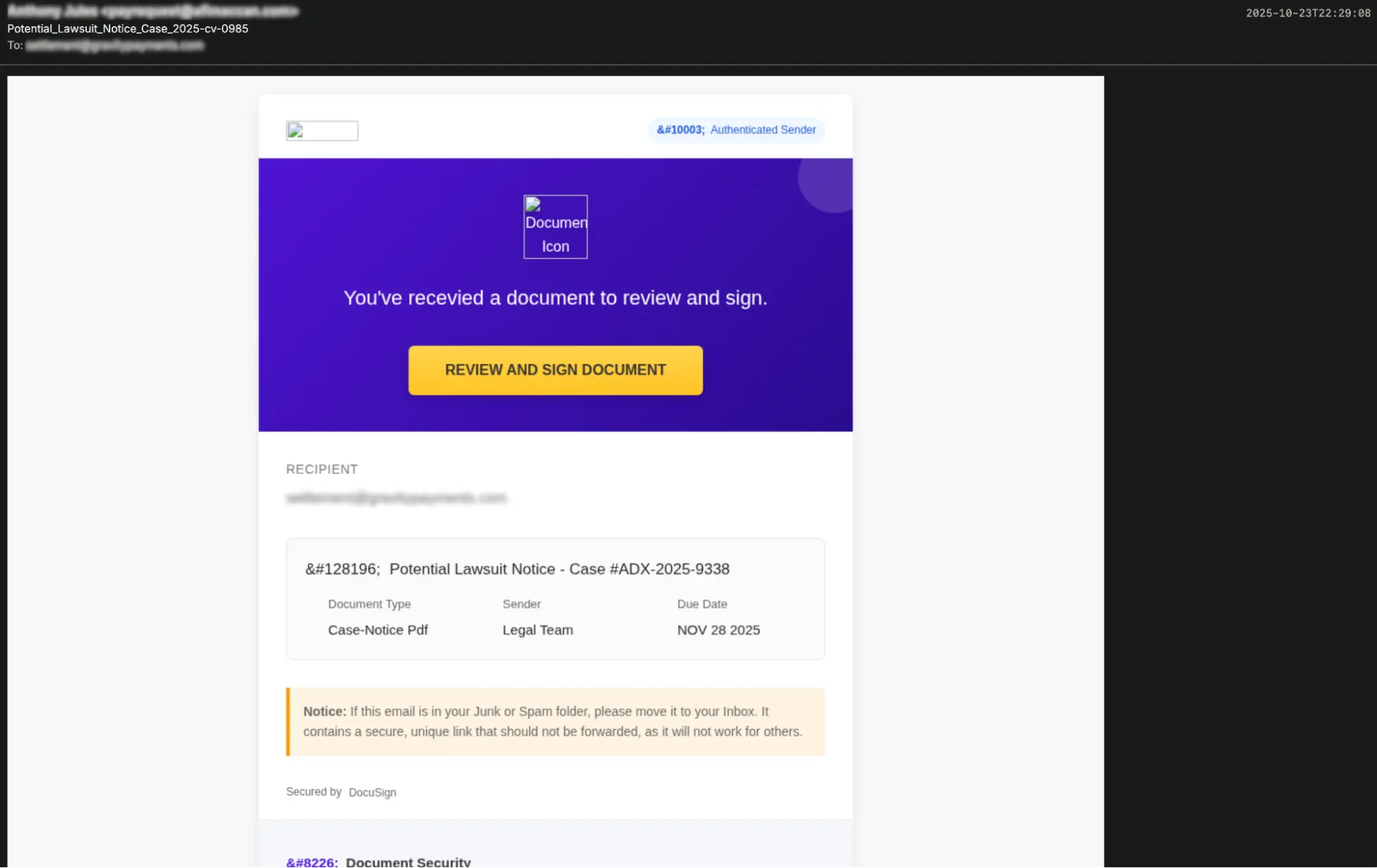
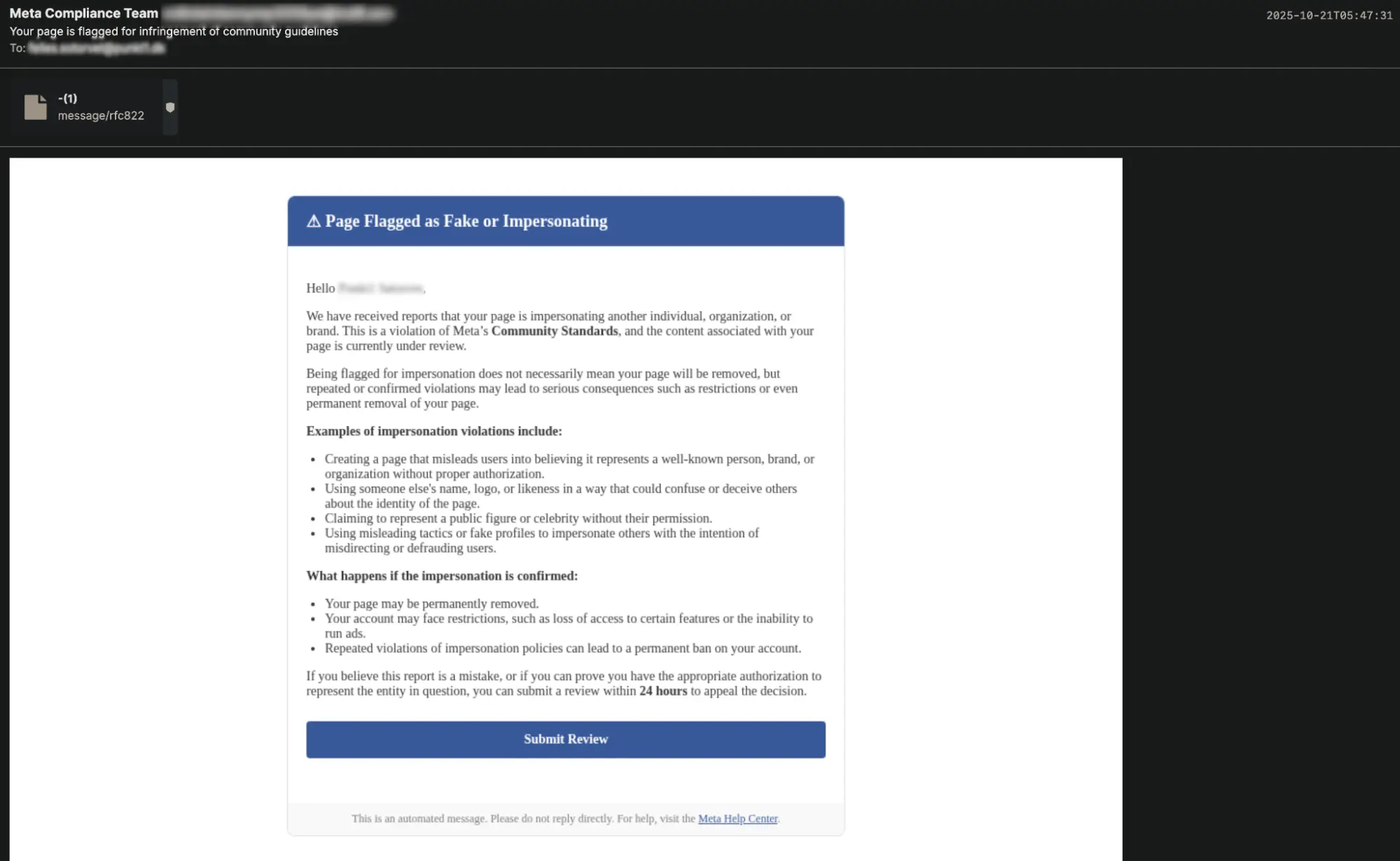
Some variants target specific regions, with Spanish-language emails posing as security update notifications, while others impersonate legitimate services like Adobe PDF viewers or financial portals.
Cloudflare analysts identified this threat while examining Vercel abuse patterns and discovered that the campaign had evolved significantly since its initial documentation in June 2025 by CyberArmor.
The researchers noted that threat actors implemented sophisticated Telegram-based filtering mechanisms designed to block security researchers and automated sandboxes from accessing the payload.
Infection Through Browser Fingerprinting and Conditional Delivery
When victims click the malicious Vercel link, they encounter a technically advanced evasion mechanism before payload delivery.
The attacker’s infrastructure performs browser fingerprinting, collecting IP addresses, device types, browser information, and geographic location.
This harvested data is exfiltrated to a threat-actor-controlled Telegram channel, where automated systems evaluate whether the victim represents a genuine target.
Security researchers and suspicious connections are filtered out, while approved victims proceed to a fake document viewer interface.
Users are then prompted to download files disguised as legitimate documents, with names like “Statements05122025.exe” or “Invoice06092025.exe.bin.”
The payload itself is not custom malware but rather a legitimate, signed copy of GoTo Resolve (formerly LogMeIn) remote access software. By leveraging this “Living off the Land” technique, attackers bypass signature-based antivirus detection systems.
Upon execution, the tool establishes connections to remote command servers, granting complete remote control and system access to threat actors.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.