Threat Actors Fake BSODs & Tools to Deploy DCR Trusted Build
Threat actors have launched a new malware campaign, delivering a dangerous remote access trojan. This sophisticated operation exploits fake Blue Screen of Death warnings and leverages trusted...
Threat actors have launched a new malware campaign, delivering a dangerous remote access trojan. This sophisticated operation exploits fake Blue Screen of Death warnings and leverages trusted Microsoft build tools to compromise systems.
The operation, tracked as PHALT#BLYX, targets hospitality businesses with deceptive reservation cancellation emails that manipulate victims into running malicious code on their systems.
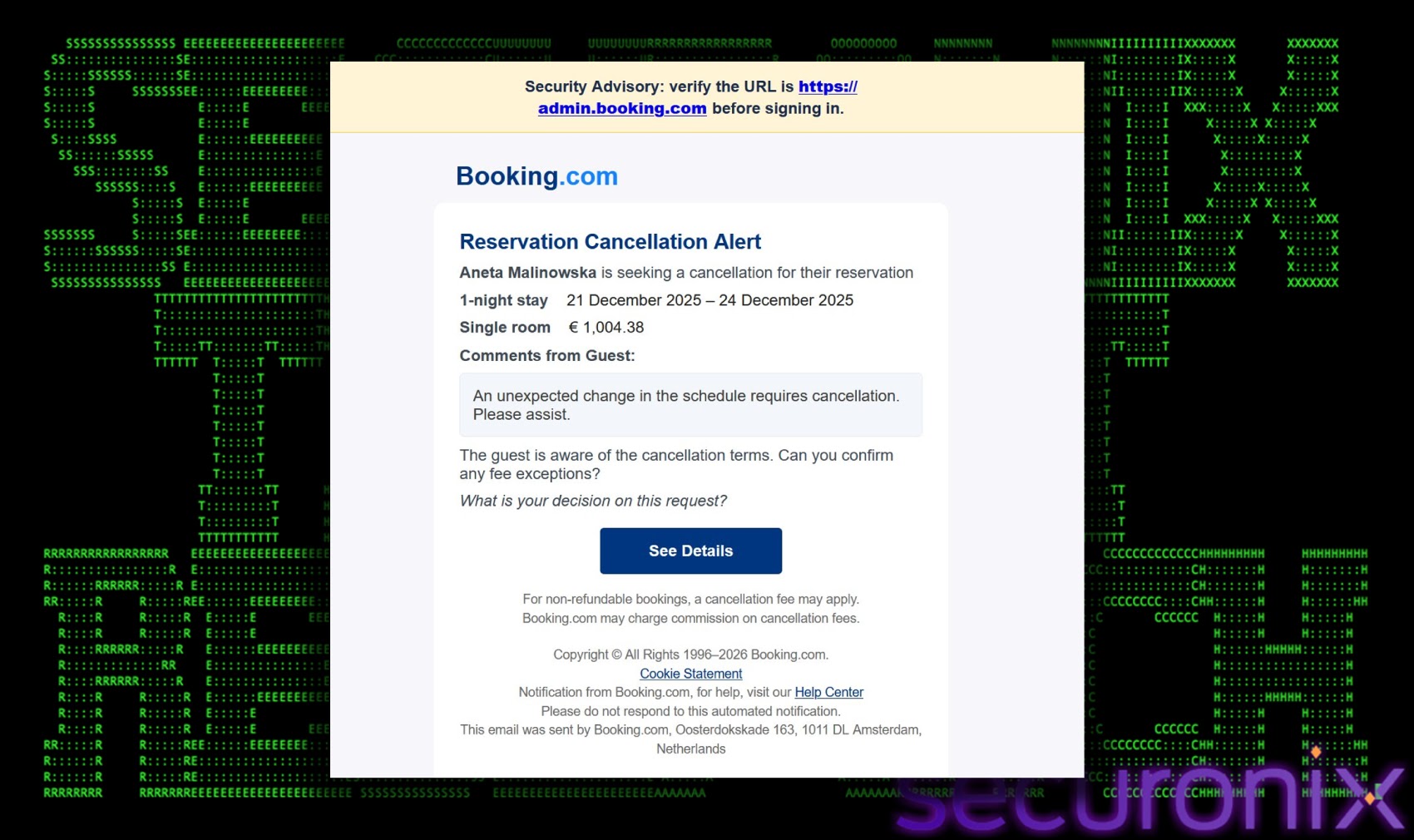
The attack begins when unsuspecting employees receive convincing phishing emails disguised as Booking[.]com reservation alerts.
These messages display alarming charges exceeding €1,000, creating immediate panic and prompting recipients to click “See Details” for verification.
Instead of reaching legitimate booking information, victims land on professionally crafted fake websites that mirror the authentic Booking.com interface down to its colors, fonts, and logos.
The psychological manipulation capitalizes on urgency and financial concern, making targets more likely to bypass normal security caution.
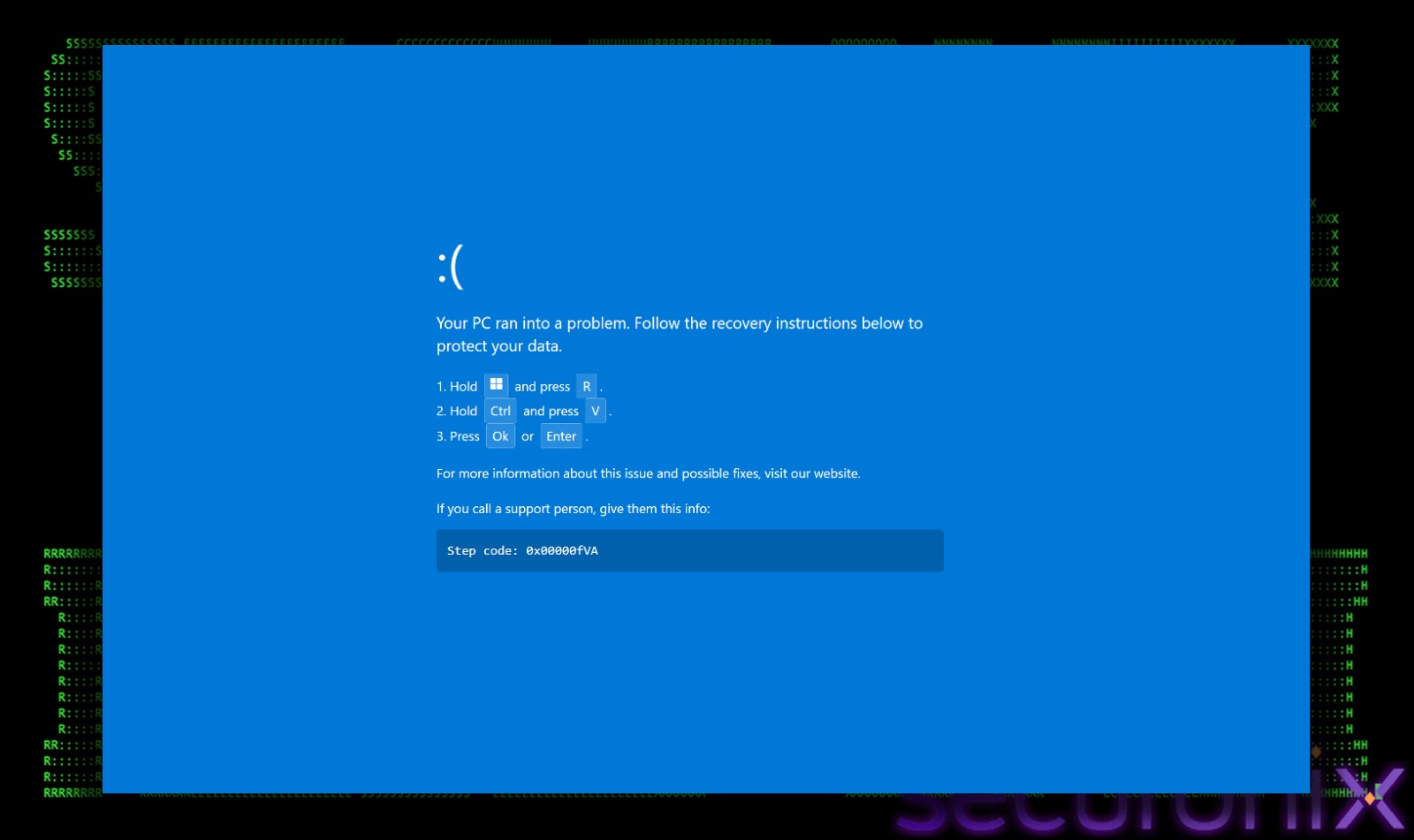
Once on the fraudulent page, victims encounter a fake browser loading error followed by a simulated Blue Screen of Death that appears alarmingly authentic.
The page instructs users to “fix” the problem by pressing Windows key + R, then pasting clipboard content and pressing Enter.
This ClickFix technique tricks people into manually executing PowerShell commands that download malicious project files and launch them through MSBuild.exe, a legitimate Microsoft compilation tool.
Securonix researchers identified this campaign after tracking the evolution of tactics from simpler HTML application delivery methods to the current sophisticated MSBuild-based infection chain.
The shift represents a strategic adaptation toward Living off the Land techniques that abuse trusted system utilities to evade traditional antivirus detection.
Analysis revealed Russian language strings embedded in the malware code, suggesting connections to Russian-speaking threat groups who commonly use DCRat in underground forums.
Multi-Stage Infection Process and Defense Evasion
The malicious PowerShell dropper executes several critical operations simultaneously.
It opens the legitimate Booking.com admin page as a decoy while secretly searching the entire system for MSBuild.exe, downloading a project file named v.proj from attacker infrastructure, and launching it through the Microsoft tool.
Because MSBuild.exe carries a valid Microsoft signature, application whitelisting and endpoint security solutions often fail to flag the execution as suspicious.
The v.proj file contains embedded PowerShell scripts that immediately target Windows Defender by adding exclusions for the entire ProgramData directory and specific file extensions including .exe, .ps1, and .proj.
This preparation ensures the final payload can land on disk without triggering quarantine alerts.
The malware then attempts privilege escalation through UAC spam tactics, repeatedly prompting users to grant administrator rights through repetitive pop-ups designed to exhaust their resistance.
After establishing persistence through Internet Shortcut files in the Startup folder, the malware deploys staxs.exe, a heavily obfuscated DCRat variant.
This payload uses AES-256 encryption with PBKDF2 key derivation and connects to command-and-control servers at asj77.com, asj88.com, and asj99.com over port 3535.
The trojan injects itself into legitimate system processes like aspnet_compiler.exe through process hollowing, effectively masking malicious activity behind trusted Windows binaries.
DCRat capabilities include keylogging, remote desktop access, process injection, and the ability to download secondary payloads such as cryptocurrency miners.
The malware collects comprehensive system fingerprints including hardware identifiers, installed antivirus software, active window titles, and domain membership status before sending this intelligence back to operators.
This information enables attackers to assess victim value and deploy appropriate follow-on tools for credential theft, lateral movement, or ransomware deployment.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.