Sophisticated AiTM Phishing Attacks Target SharePoint Services
Researchers at Microsoft have exposed a sophisticated adversary-in-the-middle (AiTM) phishing campaign targeting energy sector organizations through the abuse of SharePoint file-sharing services. The...
Researchers at Microsoft have exposed a sophisticated adversary-in-the-middle (AiTM) phishing campaign targeting energy sector organizations through the abuse of SharePoint file-sharing services.
The multi-stage attack compromised multiple user accounts and evolved into widespread business email compromise (BEC) operations across several organisations.
Initial Compromise Through Trusted Vendor
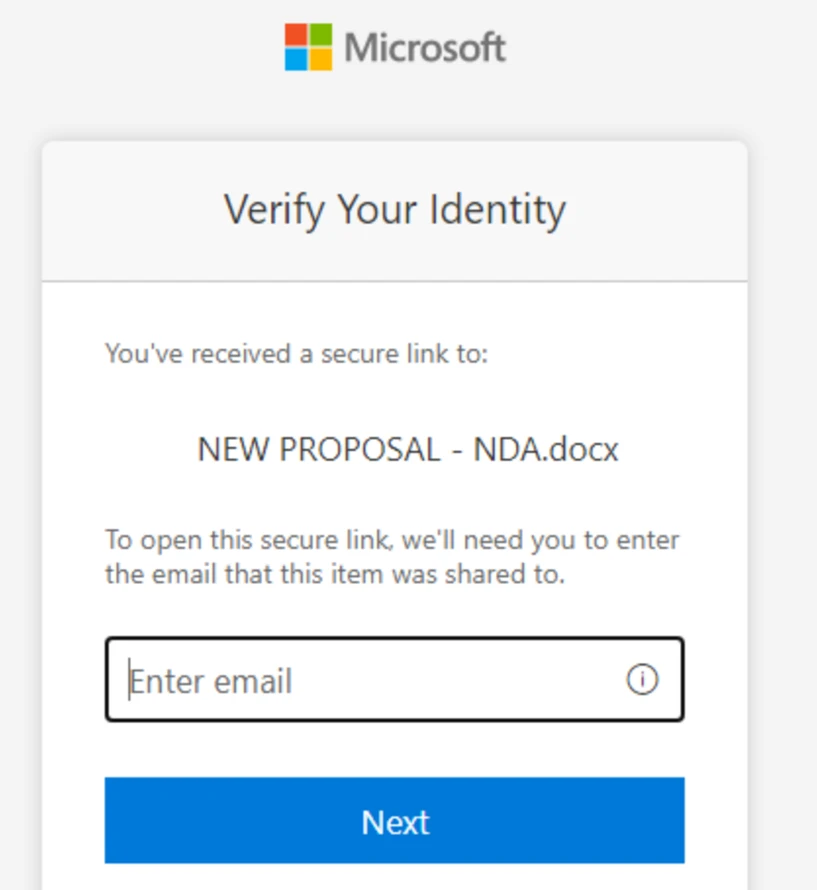
The attack began with phishing emails sent from a compromised trusted vendor’s email address. Threat actors leveraged SharePoint URLs requiring authentication, mimicking legitimate document-sharing workflows to evade suspicion.
Attackers exploited the widespread trust in Microsoft SharePoint and OneDrive services, which are ubiquitous in enterprise environments and frequently bypass traditional email security filters.
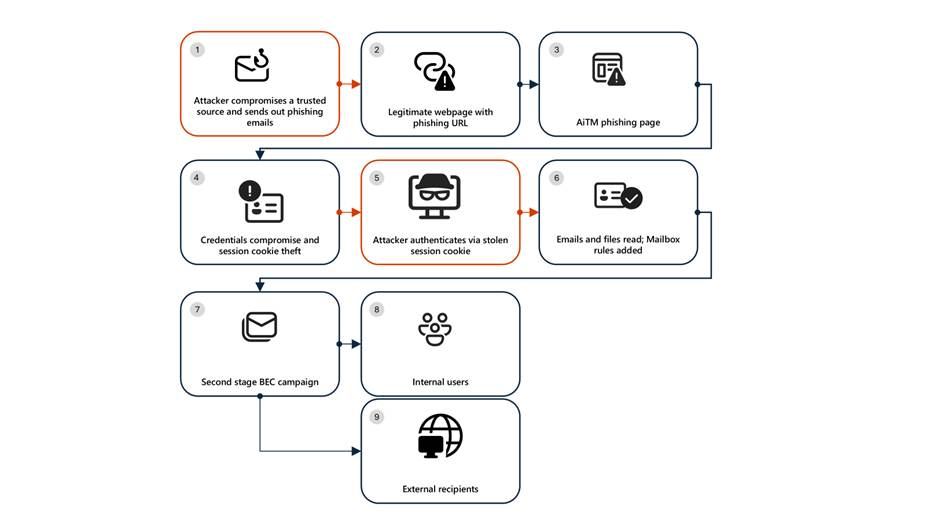
After victims clicked malicious SharePoint links and entered credentials on fake login pages, attackers gained access to user sessions.
The threat actors immediately created inbox rules to delete incoming emails and mark messages as read, maintaining stealth while monitoring compromised accounts. This tactic prevented victims from discovering suspicious activity or receiving security alerts.
Following initial compromise, attackers launched a massive phishing campaign exceeding 600 emails to contacts within and outside the victim organization.
The campaign targeted recipients identified from recent email threads in compromised inboxes, significantly expanding the attack surface.
Attackers actively monitored victim mailboxes, deleting undelivered and out-of-office notifications to avoid detection.
When recipients questioned suspicious emails, threat actors responded from compromised accounts to falsely confirm legitimacy before deleting the conversation threads.
These techniques helped maintain persistence while keeping victims unaware of ongoing operations.
Microsoft Defender Experts identified additional compromised users based on landing IP and sign-in patterns, revealing the campaign’s extensive reach across multiple organizations in the energy sector.
Microsoft emphasizes that password resets alone are insufficient for AiTM attack remediation. Organizations must revoke active session cookies, remove attacker-created inbox rules, and reset any MFA settings modified by threat actors.
Attackers can maintain access through stolen session cookies even after password changes, as they may register alternative MFA methods using attacker-controlled phone numbers.
Microsoft recommends implementing conditional access policies that evaluate sign-in requests using identity signals like IP location, device status, and user group membership.
Continuous access evaluation, security defaults in Azure Active Directory, and advanced anti-phishing solutions provide additional layers of defense.
Organizations should deploy Microsoft Defender XDR, which detects suspicious activities including multiple account sign-in attempts and malicious inbox rule creation.
Indicators of Compromise:
- 178.130.46.8 (Attacker infrastructure)
- 193.36.221.10 (Attacker infrastructure)
Energy sector organizations should immediately hunt for these IP addresses in authentication logs and investigate any associated sign-in activity.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.