Threat Actors Claim 78M Discord User Files Allegedly Dataset
Threat actor HawkSec claims to be auctioning a Discord dataset comprising 78,541,207 files. This collection, organized into messages, voice sessions, actions, and servers, reportedly stems from an...
Threat actor HawkSec claims to be auctioning a Discord dataset comprising 78,541,207 files. This collection, organized into messages, voice sessions, actions, and servers, reportedly stems from an abandoned OSINT/CSINT project that spanned several months.
HawkSec promoted the dataset in their Discord server, titled “Hello Hawks Community,” announcing availability for purchase via designated channels.
Files purportedly cover public Discord interactions, with specifics like “ME files,” voice data, and server metadata highlighted in screenshots. No pricing details surfaced publicly, but the actor invited inquiries for samples.
Similar sales have appeared before, such as a 2025 listing of 348 million scraped messages from nearly 1,000 public servers on cybercrime forums.
Researchers have also released large public datasets, such as “Discord Unveiled,” which contains over 2 billion messages from 3,167 servers via Discord’s API.
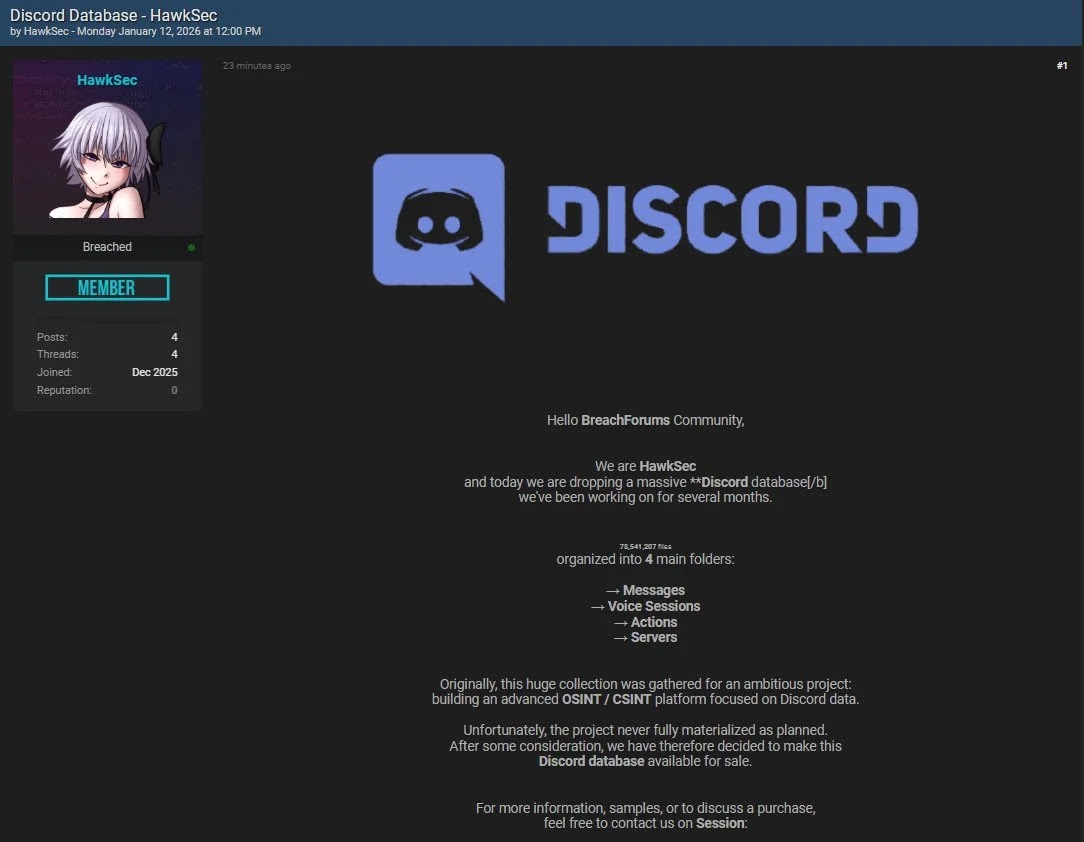
The 78 million files suggest extensive scraping, possibly targeting Discovery-listed public servers averaging 1,200 members each. HawkSec described the effort as originally aimed at advanced intelligence tools before pivoting to commercialization.
While no private data is confirmed, aggregated public logs raise re-identification risks when cross-referenced with other sources.
Discord has faced scrutiny over public scraping; past incidents involved tools like Spy.pet selling billions of messages. Legitimate academic scrapes emphasize anonymization and API compliance, unlike underground sales.
Public Discord data can fuel harassment, doxxing, or targeted phishing, even without a breach. Users in visible servers face amplified exposure, mirroring 2025 concerns over 2 billion-message datasets sparking privacy debates. No evidence ties this to Discord’s infrastructure; it aligns with API-accessible public content.
Discord maintains that public channels are openly accessible, distinguishing scrapes from breaches. In 2025, a third-party vendor incident exposed 70,000 government IDs via Zendesk, but attackers exaggerated the scope to 5.5 million users. Officials urged vigilance against phishing post-leak.
No response from Discord on HawkSec yet, as of January 12, 2026. Cybersecurity experts recommend reviewing server visibility settings and monitoring for misuse.
HawkSec’s claim remains unverified beyond the shared image, underscoring ongoing threats from data commodification in gaming communities.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.