New Ghost Tapped Attack Drains Your Android Bank Account
Chinese threat actors have engineered a novel and concerning attack vector, enabling them to directly drain bank accounts via specially designed Android Bank Account Known as Ghost Tapped Attack...
Chinese threat actors have engineered a novel and concerning attack vector, enabling them to directly drain bank accounts via specially designed Android Bank Account
Known as Ghost Tapped Attack Drainsmalicious apps exploit Near Field Communication (NFC) technology, the same wireless technology that powers contactless payments.
Instead of needing your physical bank card, criminals can complete transactions from anywhere in the world by simply relaying payment information through their own devices.
The attack works in a surprisingly simple yet effective manner. Victims are targeted through deceptive messages and phone calls, tricked into downloading malicious APK files that look like legitimate banking or payment apps.
Once installed, users are asked to tap their bank cards against their phones, believing they are registering the card for security purposes.
Unknown to them, the app captures card data and sends it to a command-and-control server operated by the criminals.
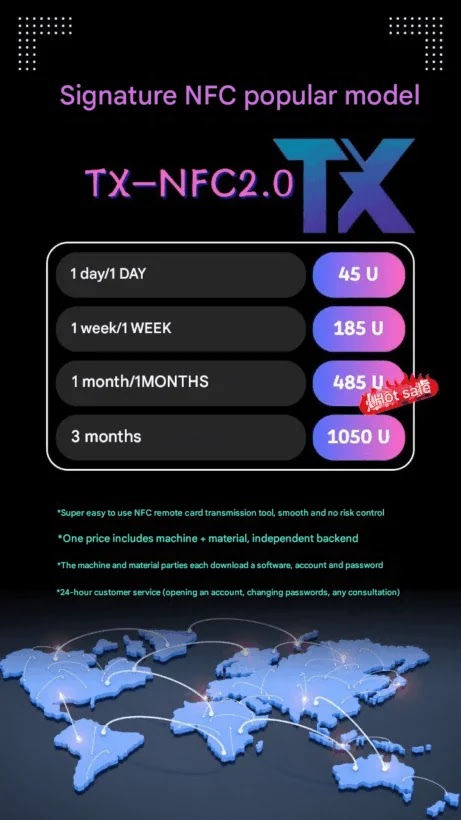
From August 2024 through August 2025, security experts identified over 54 different versions of these malicious applications, with more than half a dozen major variants actively being sold and promoted on Telegram.
Group-IB analysts identified that the malware operates through a two-part system: a “reader” application installed on the victim’s device that captures payment card information, and a “tapper” application used by criminals to complete unauthorized transactions at stores and ATMs.
The Infection Mechanism and Relay Attack
Group-IB researchers noted that the malware operates by establishing a direct relay between a victim’s payment card and a criminal’s device through internet-connected servers.
When a card is tapped to an infected Android phone running the reader app, the payment data is captured and encrypted.
This data travels through the C2 server and reaches the criminal’s tapper application, which then forwards it to real point-of-sale terminals stolen or fraudulently obtained from legitimate payment processors.
To the POS terminal, the transaction appears completely legitimate, as if the criminal’s device itself were a real bank card.
The technical implementation reveals sophisticated engineering. The applications request specific NFC permissions including android.permission.NFC and android.permission.INTERNET to function.
Upon installation, they collect device identifiers and authentication credentials, sending this information to remote servers using WebSocket or MQTT protocols.
Between November 2024 and August 2025, one associated group processed at least $355,000 in fraudulent transactions using this method.
Thousands of victims globally have already fallen victim to these schemes, with arrests occurring in multiple countries including the United States, Singapore, Czech Republic, and Malaysia, demonstrating the attack’s growing real-world impact.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.