Vortex Werewolf Attacking Organizations to Gain Tor-Enabled Remote
A new cyber espionage cluster has recently emerged, aggressively targeting Russian government and defense organizations. Active since at least December 2025, the group, designated as Vortex Werewolf,...
A new cyber espionage cluster has recently emerged, aggressively targeting Russian government and defense organizations.
Active since at least December 2025, the group, designated as Vortex Werewolf, employs a combination of social engineering and legitimate software utilities to breach secure networks.
Their primary objective appears to be establishing persistent, covert remote access to sensitive systems using anonymized protocols.
The attacks typically commence with phishing emails that deceive recipients into interacting with malicious links.
These lures mimic legitimate file-sharing notifications, often disguised as Telegram or other trusted services.
Once a victim engages with the bait, the infection chain initiates, leading to the deployment of tools designed to bypass standard network defenses.
The malware facilitates unauthorized control by configuring remote desktop and file transfer protocols to route traffic through the Tor network.
BI.ZONE researchers identified this activity cluster in early 2026, highlighting the group’s unique operational methods.
While sharing some behavioral similarities with other threat actors like Core Werewolf, this adversary utilizes specific obfuscation bridges for command and control communications.
The impact of a successful breach is significant, as it grants attackers the ability to execute commands and transfer files via RDP, SMB, SFTP, and SSH, all while remaining hidden behind Tor Hidden Services.
To maintain their foothold within compromised environments, the attackers implement persistence mechanisms that survive system reboots.
The malware creates scheduled tasks within the Windows operating system to ensure that the Tor client and the SSH server launch automatically.
This setup allows the threat actors to retain long-term access to the victim’s infrastructure, enabling them to exfiltrate data or pivot to other critical systems at will without triggering immediate alarms.
Infection Mechanism and Phishing Tactics
The infection process is characterized by a high degree of social engineering sophistication designed to steal user credentials before delivering the payload.
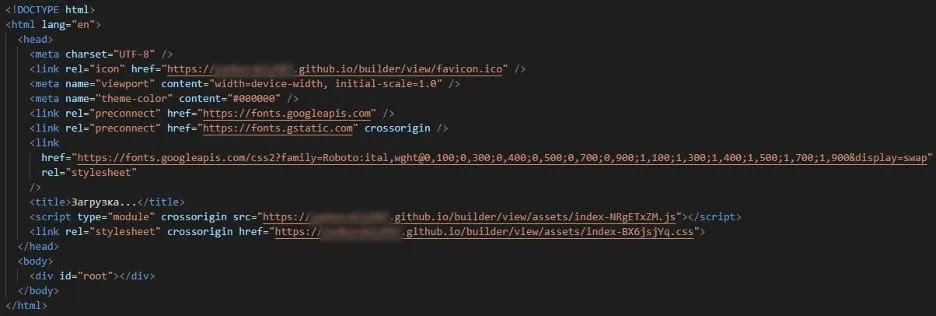
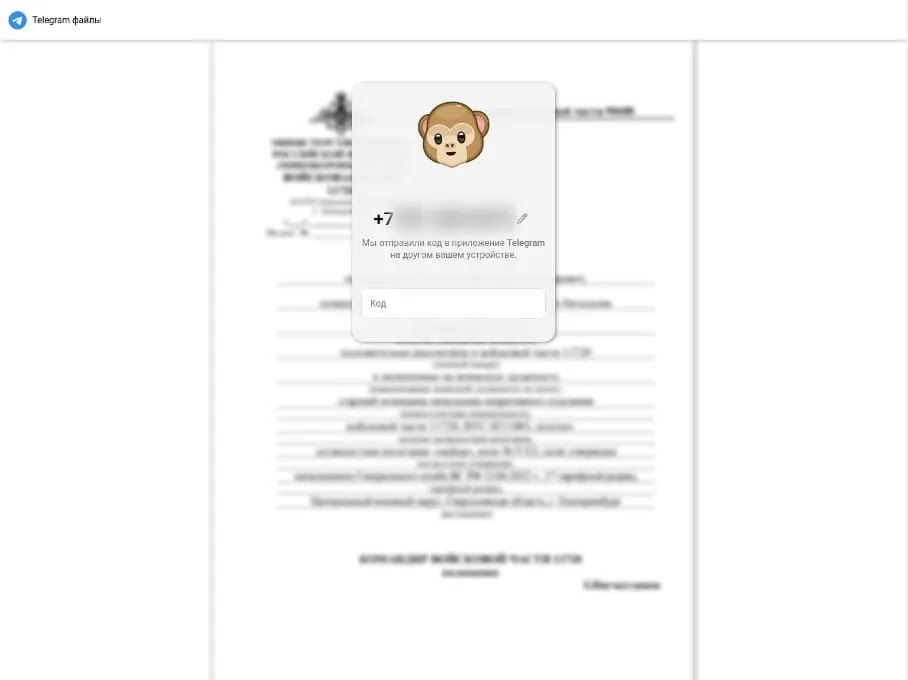
When a user clicks the initial phishing link, they are directed to a fraudulent webpage that convincingly replicates the interface of a Telegram file download portal.
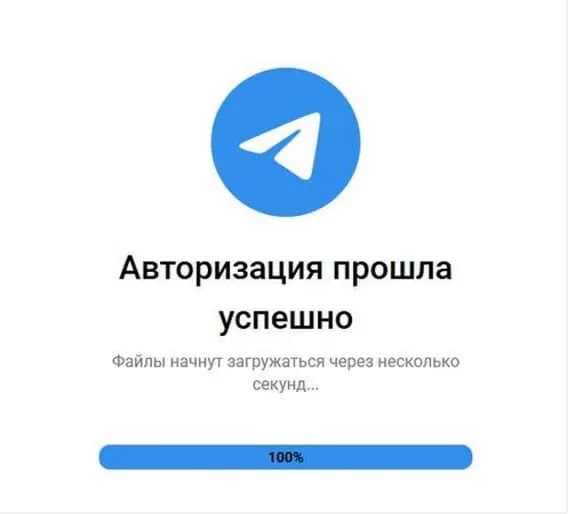
This site prompts the victim to enter their phone number and the subsequent login confirmation code, effectively hijacking their active session.
Upon successfully capturing the victim’s session data, the phishing page redirects the user to a legitimate file hosting service, such as Dropbox, to download a malicious ZIP archive.
This archive contains a deceptive LNK file which, when executed, triggers a PowerShell script. This script performs checks to evade sandbox environments before installing the Tor and OpenSSH components required for the encrypted command tunnel.
Organizations are advised to implement robust email filtering solutions that utilize machine learning to detect spoofed links and phishing anomalies.
Security teams should strictly verify the destination of all incoming URLs and block traffic to known malicious domains.
Furthermore, continuous monitoring of network logs for unauthorized Tor or SSH connections is essential for early threat detection.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.