Threat Actors Phish with LogMeIn Resolve & Screen Abuse ScreenConnect
A sophisticated phishing campaign is actively targeting organizations across the United States, leveraging trusted remote monitoring and management (RMM) tools like LogMeIn Resolve and ScreenConnect...
A sophisticated phishing campaign is actively targeting organizations across the United States, leveraging trusted remote monitoring and management (RMM) tools like LogMeIn Resolve and ScreenConnect to bypass security defenses and gain unauthorized access to victim systems, according to a recent analysis
The campaign appears to have begun as early as April 2025, with the bulk of malicious activity occurring between October and November of the same year.
In total, more than 80 organizations across multiple industry sectors in the US were affected. Attackers initiated contact through phishing emails — some sent from compromised third-party accounts belonging to known and trusted contacts, making the messages appear credible, while others came from completely unknown senders.
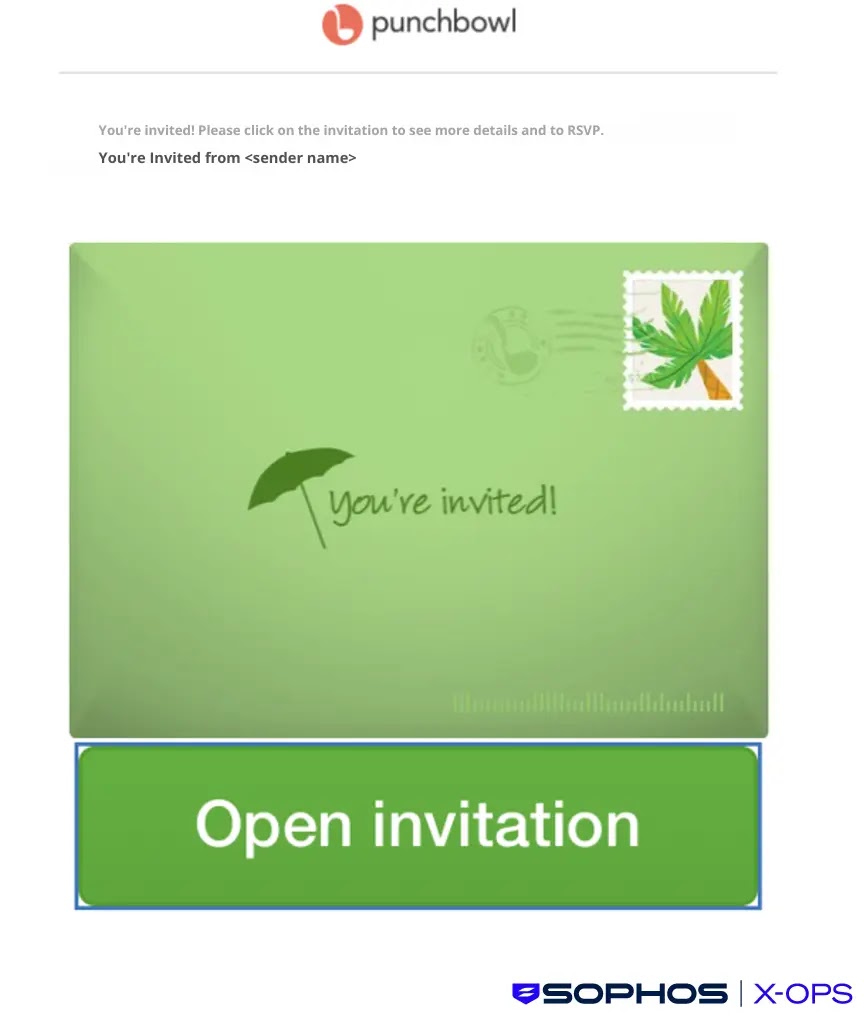
Many of these emails were designed to look like Punchbowl event invitations, carrying subject lines such as “SPECIAL INVITATION,” while others mimicked tender solicitation notices.
Each email contained a link pointing to attacker-controlled distribution sites that hosted legitimate LogMeIn Resolve installers preconfigured to register the victim’s device to an account fully owned and controlled by the attacker.
Sophos analysts and researchers identified and tracked this threat activity cluster as STAC6405.
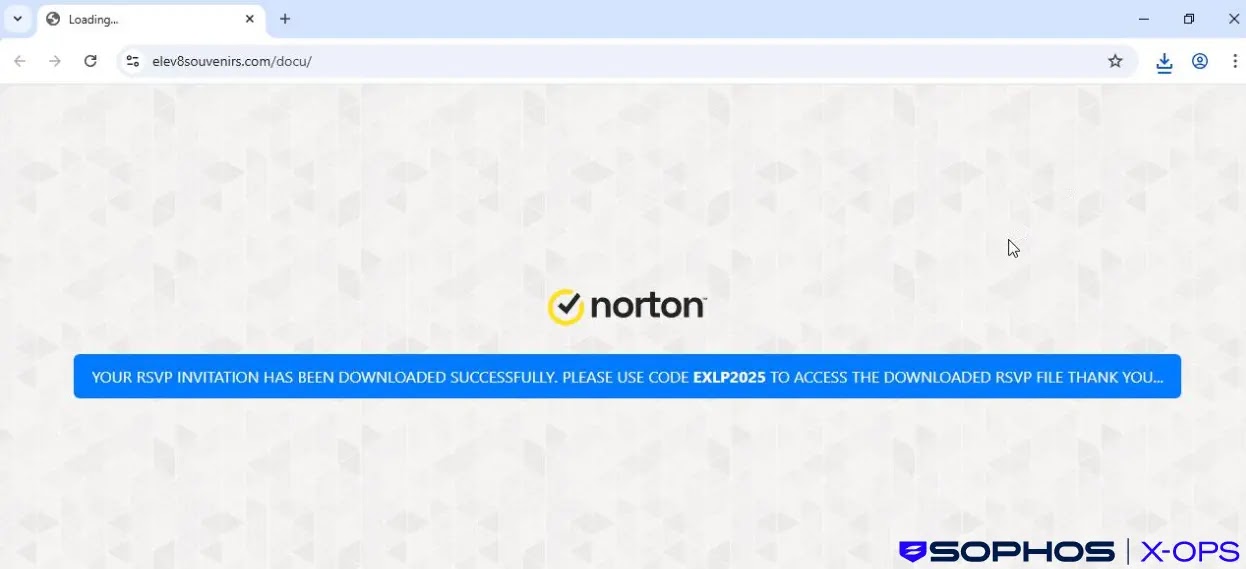
Their ongoing investigation revealed that the campaign’s distribution infrastructure shifted repeatedly over time, with the threat actor rotating between themed landing pages — including one mimicking Microsoft Teams and another styled after Norton security software — possibly to tailor delivery based on user location or browser attributes.
The malicious installer files carried names carefully designed to appear routine, such as Invitation.exe, ContractAgreementToSign.exe, and statmtsPDF10.25.exe.
Once a victim executed the downloaded file, the attacker gained unattended remote access through the LogMeIn Resolve platform.
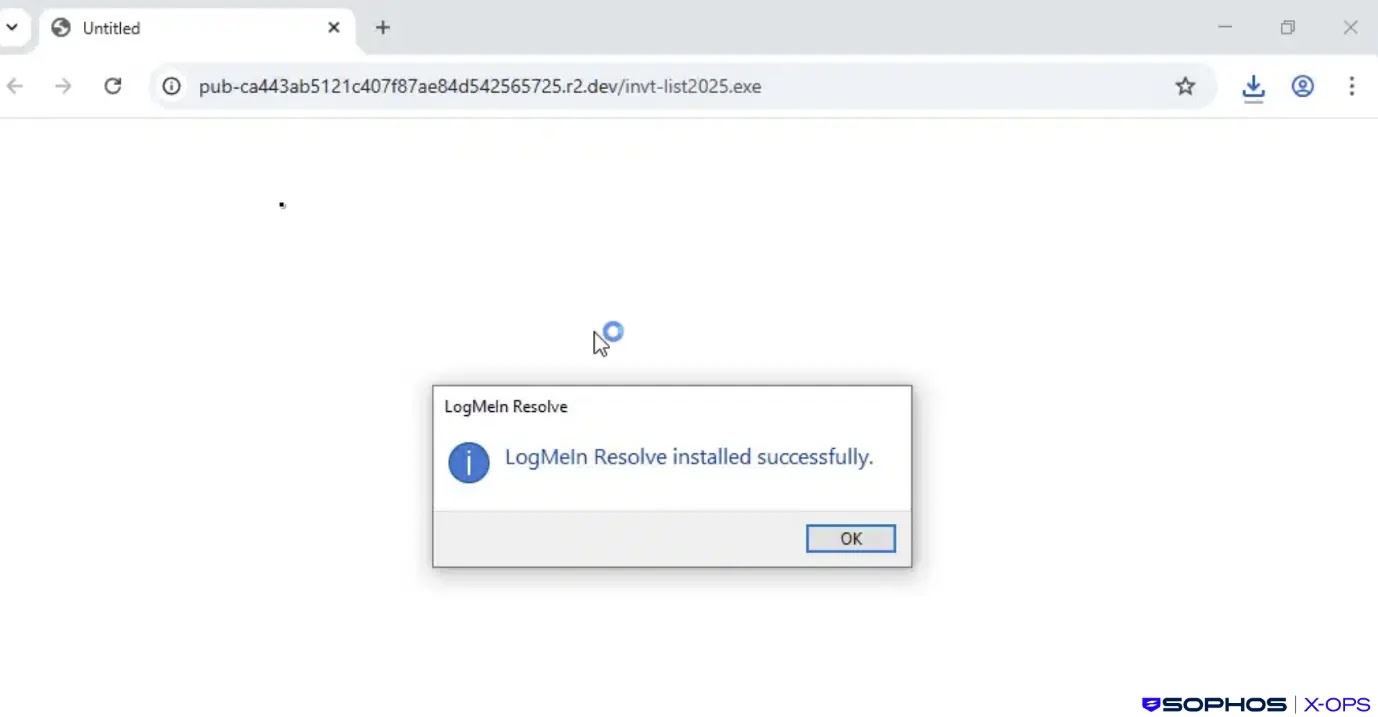
The installed agent wrote a configuration file to disk with a hard-coded relay domain controlled by the attacker and registered a Windows service using a unique ID tied to that specific configuration.
In most observed cases, the attack stopped at this point — threat actors appeared to remain idle after gaining initial access, a pattern commonly linked to initial access broker (IAB) operations, where stolen access is quietly sold on criminal marketplaces for further exploitation.
Multi-Stage Payload Delivery
In two incidents, however, the threat actors moved to a second stage very quickly. In the first case, they exploited a pre-existing installation of ScreenConnect — already running on the victim machine — to download a ZIP archive packed with the HeartCrypt Packer-as-a-Service tool.
The archive held two files: HideMouse.exe, a utility that replaces the visible mouse cursor with a transparent one to conceal remote on-screen activity from the user, and 87766713.exe, a piece of malware that Sophos researchers assessed as behaviorally similar to ValleyRAT.
Once executed, the infostealer sat idle for four to nine minutes — a deliberate delay designed to bypass sandbox analysis and heuristic detection tools — before injecting code into csc.exe, a legitimate Microsoft binary regularly abused as a living-off-the-land binary (LOLbin).
The malware then connected to a command-and-control server and began harvesting browser-stored credentials, session tokens, cryptocurrency wallet data, and system details. An embedded encrypted payload was decrypted at runtime using TripleDES cryptography.
In the second incident, the downloaded binary launched a ScreenConnect client as a service alongside a Java-based remote access tool, and the attacker began enumerating firewall rules before Sophos and the affected organization successfully contained the breach.
Organizations should restrict software installations to an approved list, enforce strong credential hygiene through secure password managers or passkeys, and remove RMM tools like LogMeIn if they are not needed for daily business use.
Unauthorized RMM tools should also be blocked through application control policies. Any URLs and indicators of compromise associated with this campaign should be blocked promptly across all network entry points.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.