State-Backed Hackers Target Signal Messages of Officials
Germany’s top security agencies yesterday issued an urgent warning regarding a sophisticated cyber espionage campaign. This operation specifically targets high-ranking officials and journalists...
Germany’s top security agencies yesterday issued an urgent warning regarding a sophisticated cyber espionage campaign. This operation specifically targets high-ranking officials and journalists across Europe.
The Federal Office for the Protection of the Constitution (BfV) and the Federal Office for Information Security (BSI) revealed that state-sponsored hackers are hijacking Signal accounts to spy on private communications.
The joint advisory, released February 6, identifies the primary targets as military personnel, diplomats, politicians, and investigative journalists.
Unlike traditional hacks that use malware or exploit software bugs, this campaign relies entirely on “social engineering”, tricking victims into using legitimate features against themselves.
The “Fake Support” Trap
The first attack method involves hackers posing as “Signal Support” or a “Signal Security ChatBot.”
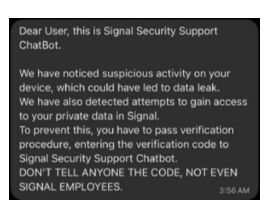
They contact targets directly within the app, claiming suspicious activity or a data leak has occurred on the victim’s device.
To “fix” the problem, the fake support bot asks the user to verify their identity by sending a PIN code.
If a victim shares this six-digit code, the hackers immediately register the victim’s phone number on a new device they control.
This locks the legitimate user out of their own account while giving the attackers complete control to impersonate the victim in future chats.
The Silent QR Code Spy
The second method is more subtle and allows hackers to spy on chats without locking the user out.
Attackers use a plausible pretext, such as a request to join a group or verify a device, to trick the victim into scanning a QR code.
Technically, this QR code is a “device linking” request. When a victim scans it, they inadvertently authorize the hacker’s tablet or computer to link to their account.
Once connected, the attacker can silently read all new messages and view chat history from the past 45 days.
This access often persists for weeks because the victim’s phone usually continues to work, masking the intrusion.
Authorities believe a “state-controlled cyber actor” is behind the campaign, given the specific focus on high-value intelligence targets rather than financial theft.
The goal appears to be espionage, involving the mapping of social networks and the interception of sensitive political and military discussions.
Because the attacks use valid Signal features rather than viruses, they bypass most antivirus software.
Security officials urge all users to check their “Linked Devices” list in Signal settings immediately and never to share verification PINs with anyone, even accounts claiming to be support staff.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.