Qilin Ransomware Evades EDR Solutions with Mal Uses Malicious
The Qilin ransomware group is deploying a sophisticated, multi-stage infection chain that effectively bypasses many endpoint detection and response (EDR) solutions. This complex attack leverages a...
The Qilin ransomware group is deploying a sophisticated, multi-stage infection chain that effectively bypasses many endpoint detection and response (EDR) solutions. This complex attack leverages a malicious msimg32.dll to disable over 300 EDR drivers from virtually every major security vendor.
As organizations increasingly rely on EDR solutions, which offer far greater behavioral visibility than legacy antivirus, threat actors have adapted by weaponizing EDR killers as a core component of their attack chain.
By disabling telemetry collection across process creation, memory activity, and network behavior, attackers can operate undetected long enough to deploy their ransomware payload.
Qilin, also tracked as Agenda, Gold Feather, and Water Galura, has claimed over 40 victims per month and is considered one of the most active ransomware-as-a-service (RaaS) operations.
DLL Sideloading as the Entry Point
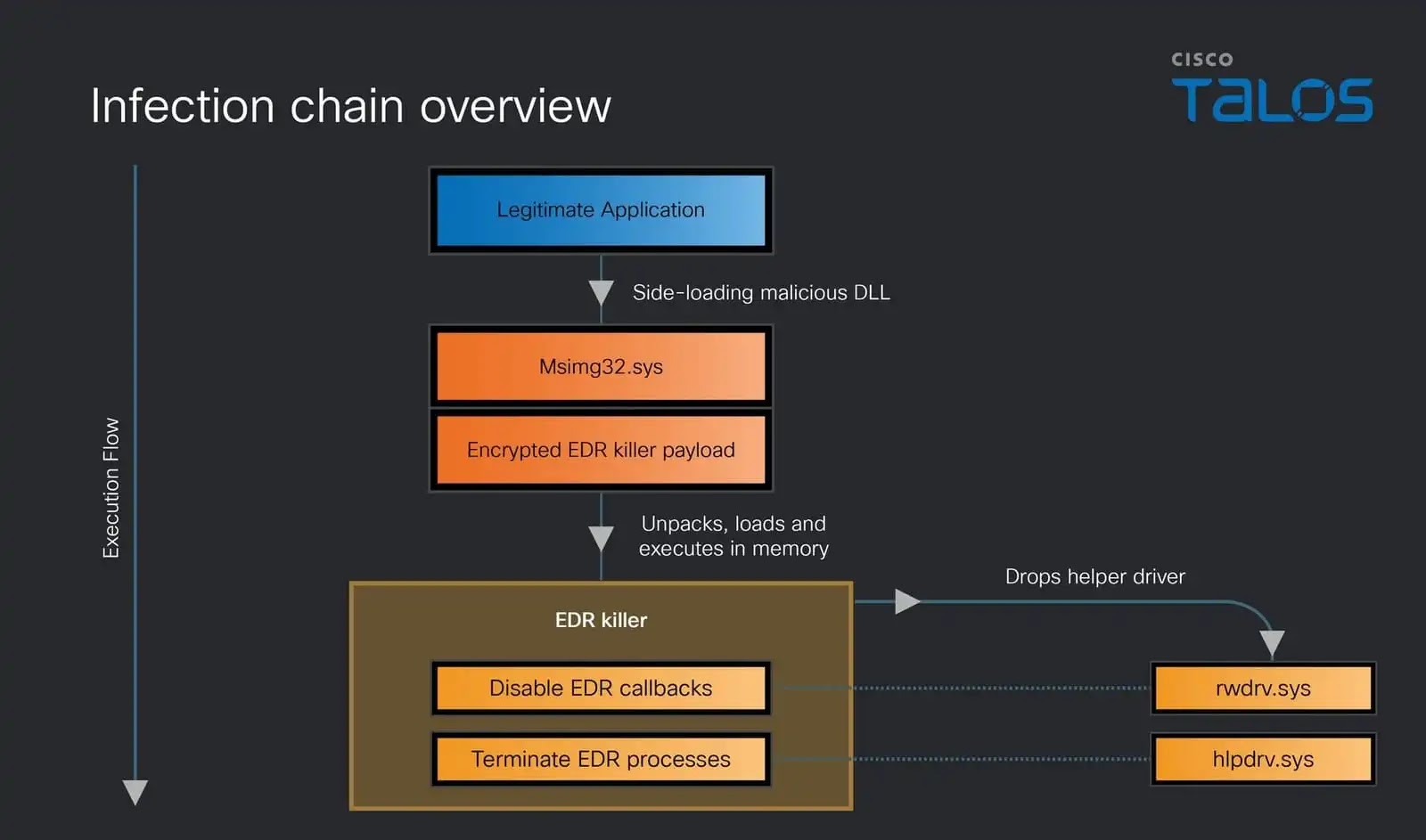
Cisco Talos researchers uncovered that the attack begins when a legitimate application, such as FoxitPDFReader.exe, sideloads the malicious msimg32.dll in place of the genuine Windows library.
To avoid immediate suspicion, the rogue DLL forwards all expected API calls to the real C:WindowsSystem32msimg32.dll, preserving normal application behavior while triggering its malicious logic directly from the DllMain function.
Embedded within the DLL is an encrypted EDR killer payload that goes through three loader stages before the final component is executed entirely in memory, never touching disk in its decrypted form.
The loader employs a series of advanced anti-detection techniques specifically designed to blind EDR products before they can raise an alert:
- SEH/VEH-based control flow obfuscation — Structured Exception Handling (SEH) and Vectored Exception Handling (VEH) are weaponized to conceal API invocation patterns and transfer execution covertly between stages.
- ETW suppression — Event Tracing for Windows is neutralized at runtime, depriving defenders of telemetry needed for behavioral detection.
- Halo’s Gate syscall bypass — The loader scans
ntdll.dllboth forward and backward to locate clean, unhooked neighboring syscall stubs. It then repurposes those stubs to invoke desired system calls, bypassing EDR-hooked APIs without modifying any hooked code. - Kernel object manipulation — The loader overwrites the
.mrdatasection ofntdll.dll— which holds the exception dispatcher callback pointer — to redirect exception handling to its own custom routine. - Anti-debugging measures — The malware checks for breakpoints on
KiUserExceptionDispatcherand deliberately crashes the process if one is detected.
The loader also implements geo-fencing, terminating execution if the system locale matches a post-Soviet country a deliberate exclusion list that mirrors patterns seen in other Russian-affiliated ransomware operations.
The EDR Killer
Once the multi-stage loader delivers its final payload (Stage 4), the EDR killer PE loads two kernel-level helper drivers.
- rwdrv.sys — A renamed version of
ThrottleStop.sys, legitimately signed by TechPowerUp LLC and used in tools like GPU-Z. Despite its benign origin, the driver exposes powerful IOCTLs for physical memory read/write, MSR access, and PCI configuration exploited here to directly manipulate kernel structures without going through protected virtual memory. - hlpdrv.sys — Used exclusively to terminate protected EDR processes via IOCTL code
0x2222008, bypassing Windows process protection mechanisms.
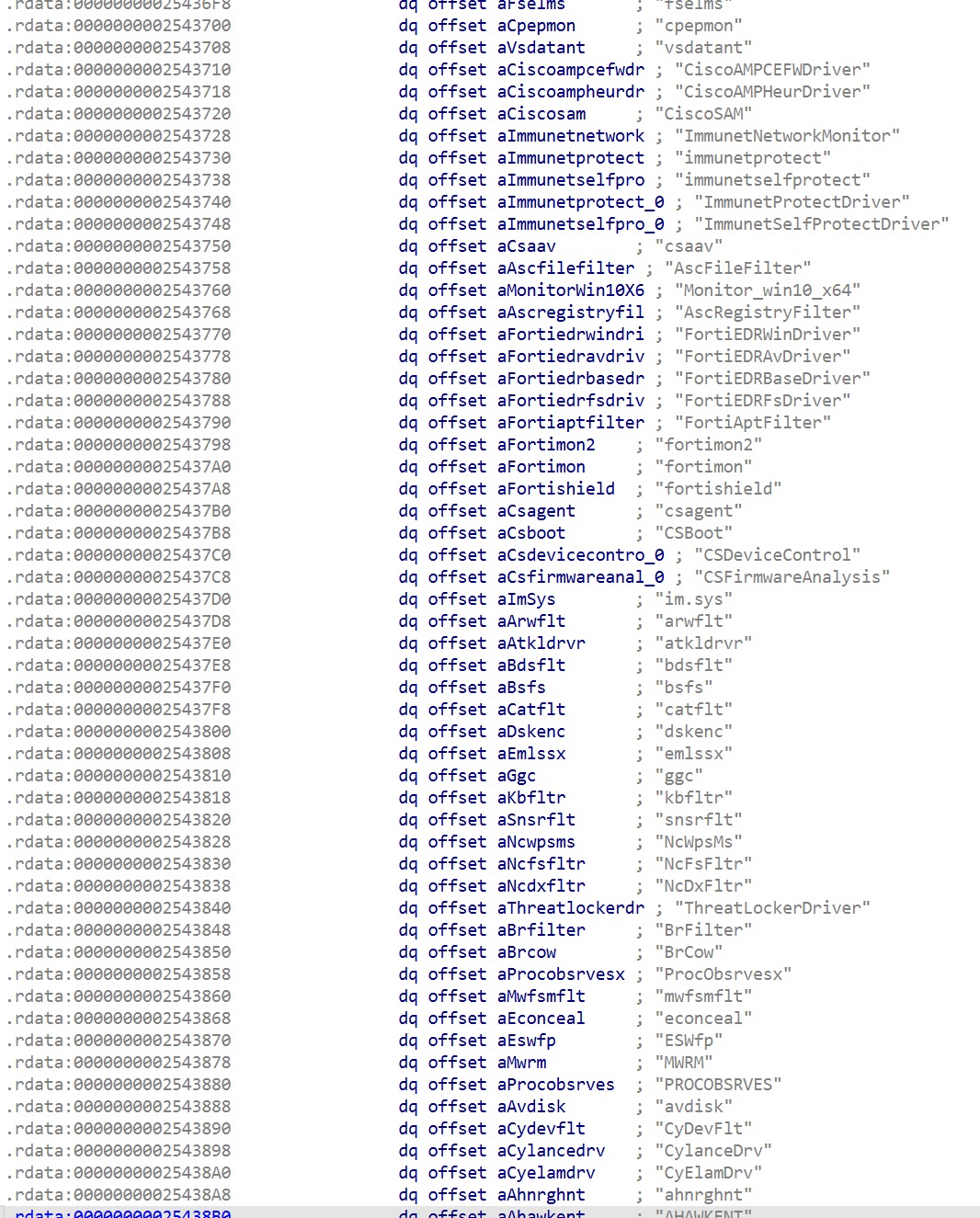
The EDR killer iterates through a hardcoded list of over 300 EDR driver names, using physical memory writes via rwdrv.sys to unregister monitoring callbacks for process creation, thread creation, and image loading events, disabling EDR visibility at the kernel level.
Notably, the malware temporarily overwrites the CiValidateImageHeader callback with a function that always returns true, disabling Code Integrity enforcement while the attack proceeds, then restores it afterward to reduce forensic traces.
Cisco Talos notes that while these techniques are not entirely novel, they remain highly effective and should be detectable by properly configured, multi-layered defense stacks.
The campaign demonstrates that targeting the defense layer itself before ransomware is ever deployed is now a standard operational phase for sophisticated ransomware groups like Qilin.
Organizations are strongly advised to monitor for suspicious DLL sideloading activity, unexpected driver installations (rwdrv.sys, hlpdrv.sys), and any attempts to write to physical memory from user-mode processes. Relying on a single security product is no longer sufficient against adversaries engineered specifically to neutralize it.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.