Pulsar RAT Steals Data from Windows via Run Registry
Pulsar RAT, a sophisticated remote access trojan, is behind a new wave of attacks currently targeting Windows systems. This malware establishes persistence using the per-user Run registry key,...
Pulsar RAT, a sophisticated remote access trojan, is behind a new wave of attacks currently targeting Windows systems.
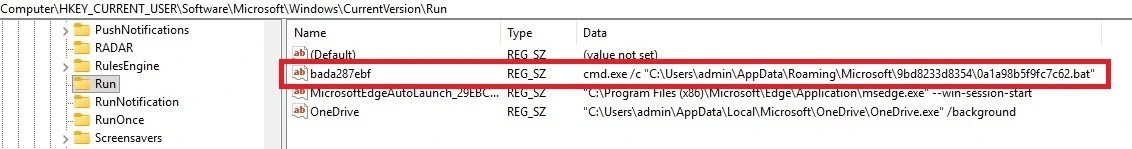
This malware establishes persistence using the per-user Run registry key, enabling automatic execution each time an infected user logs into their system.
The threat represents a dangerous combination of stealth, persistence, and data theft capabilities designed to evade traditional security controls.
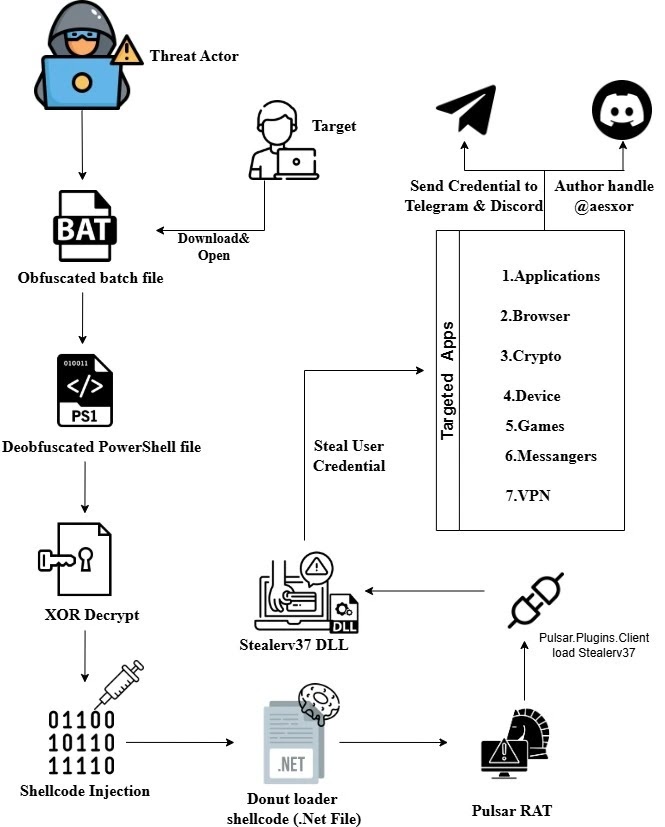
The attack begins with an obfuscated batch file that quietly copies itself to a hidden folder within the user’s AppData directory.
This file then registers itself in the Windows registry under HKCUSoftwareMicrosoftWindowsCurrentVersionRun, ensuring the malware launches automatically at startup without requiring administrative privileges.
Once active, Pulsar RAT deploys a multi-stage infection chain that extracts and executes embedded PowerShell loaders while minimizing disk artifacts that could alert security systems.
Point Wild analysts identified the malware operating through living-off-the-land techniques and in-memory payload delivery methods.
The PowerShell stage decrypts and injects Donut-generated shellcode directly into legitimate Windows processes like explorer.exe, employing delayed execution and a watchdog mechanism to maintain resilient persistence.
Decryption of the shellcode reveals a heavily obfuscated .NET payload implementing full-featured stealer and remote access capabilities that target credentials, surveillance, and system control.
The malware demonstrates advanced anti-analysis techniques including anti-virtualization, anti-debugging, and process injection detection.
Stolen data encompasses browser credentials, cryptocurrency wallets, VPN configurations, gaming platform accounts, and messaging application tokens.
All harvested information gets compressed into ZIP archives and exfiltrated over Discord webhooks and Telegram bots, with messages labeled “stealer by @aesxor” to help attackers track infected victims.
Persistence and Evasion Mechanisms
Pulsar RAT ensures long-term access through dual-layer persistence using both Windows Scheduled Tasks and registry Run keys as fallback.
The malware creates a scheduled task configured to run at user logon with highest available privileges, while simultaneously writing the executable path under the current user Run key.
This redundancy guarantees execution survives even in restricted environments where one persistence method might be blocked or monitored.
Detection efforts face significant challenges due to the malware’s continuous background monitoring threads that watch for debuggers, virtual machines, and injection attempts.
When analysis tools like x64dbg, WinDbg, dnSpy, or IDA are detected through window enumeration or API checks, the malware immediately terminates itself to avoid examination.
This self-protection extends to hardware breakpoint detection, PEB debugging flags, and handle manipulation techniques that together form a comprehensive anti-analysis framework designed to resist reverse engineering.
Organizations should implement behavioral detection systems capable of identifying in-memory shellcode injection, monitor registry Run key modifications, and scrutinize unusual PowerShell execution patterns.
Network monitoring for connections to known command-and-control servers at 185.132.53.17:7800 and blocking Discord/Telegram exfiltration channels can also help contain active infections.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.