New xlabs_v1 Botnet Targets Minecraft Servers Through ADB-Exposed
A newly identified botnet, xlabs_v1, is now actively targeting Minecraft game servers. This threat exploits Android devices where the Android Debug Bridge (ADB) port remains open and exposed to the...
A newly identified botnet, xlabs_v1, is now actively targeting Minecraft game servers. This threat exploits Android devices where the Android Debug Bridge (ADB) port remains open and exposed to the internet, a vulnerability extensively detailed in a recent
The xlabs_v1 botnet targets any internet-facing device running ADB on TCP port 5555, including Android TV boxes, set-top boxes, smart TVs, residential routers, and IoT hardware that ships with ADB enabled by default.
Once the attacker gains entry through the open ADB port, the bot binary is silently dropped into the device’s /data/local/tmp/ directory, executed, and the device joins a growing fleet used for paid DDoS attacks.
The botnet focuses on game-server disruption, with a dedicated RakNet flood variant built specifically to attack Minecraft servers, and the distribution server even serves the bot binary over TCP port 25565, the default Minecraft server port.
Hunt.io analysts identified the operation in early April 2026 during routine monitoring of bulletproof-hosting netblocks.
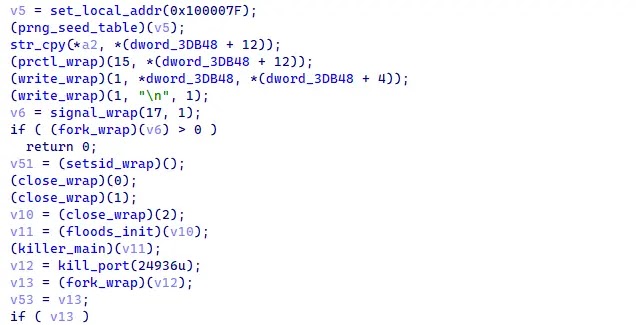
Their open directory tool, AttackCapture, flagged an exposed directory on a Netherlands-hosted server at 176.65.139[.]44 with no authentication required.
The openly accessible toolkit included two ELF binaries, infection payloads, proxy credentials, and a target placeholder, giving researchers a complete picture of the operation.
Cross-referencing a production ARM32 binary with an unstripped development build allowed analysts to recover the C2 domain, operator handle, and authentication token.
The operator behind xlabs_v1 goes by the handle Tadashi, a value encrypted inside every build of the bot.
The entire operation runs inside a single bulletproof /24 netblock by Offshore LC in the Netherlands (AS214472), where the C2 server, staging host, and distribution infrastructure all reside.
![IP 176.65.139[.]44 showing Mirai classification on TCP 80, two AttackCapture open directory flags, and hosting under Offshore LC (Source - Hunt.io)](https://hackersradar.com/wp-content/uploads/2026/05/content_1777906829_6449.jpg)
A co-located Monero cryptomining campaign using the VLTRig toolkit was also observed on the same netblock, though whether it shares the same operator could not be confirmed from the captured files alone.
Inside the Infection Mechanism
Once the bot lands on a victim device, it moves through several steps designed to stay hidden.
It first blocks the SIGINT signal to stop the launching process from interrupting it, captures an infection-vector tag from a startup argument, and then zeros that argument so it cannot be seen in standard process listings.
The bot then decrypts its internal string table using ChaCha20 encryption, which holds the C2 domain, operator handle, and authentication token.
After the cryptographic step, the bot overwrites its process name with /bin/bash using a system call, making it look like a normal shell process to any administrator checking running processes.
It then detaches from the terminal session, closes all standard input and output handles, and runs silently in the background, making the infection difficult to spot during routine checks, though it does not defeat dedicated security software.
The bot connects to its C2 server at xlabslover[.]lol over TCP port 35342, sending a registration message with the device hostname, CPU count, RAM size, and per-build authentication token.
If the outbound connection fails, it opens a fallback listener on TCP port 26721, punching through the firewall using five different iptables paths to keep the operator’s re-entry channel open.
Before establishing C2 communication, xlabs_v1 scans running processes and kills any competing malware it finds, including a hard-coded rival bot at TCP port 24936.
A bandwidth-profiling routine also opens 8,192 parallel sockets to the nearest Speedtest server, measuring upstream capacity so the operator can price-tier infected devices for customers.
Defenders are advised to disable ADB on all internet-facing Android and IoT devices, block outbound connections to TCP port 35342, monitor for /bin/bash processes running without a controlling terminal, check for files at /data/local/tmp/arm7, and treat any outbound traffic to xlabslover[.]lol or pool[.]hashvault[.]pro as a sign of active infection.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.