New Helpdesk Impersonation Abuses Microsoft Attackers Teams
A new and deceptive The attack starts simply. A threat actor, operating from a separate Microsoft tenant, sends an unsolicited Teams message to a target employee while posing as internal IT support...
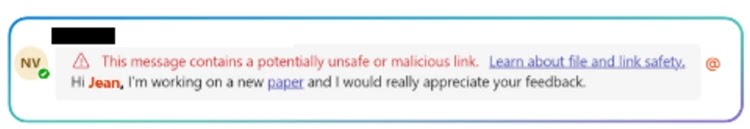
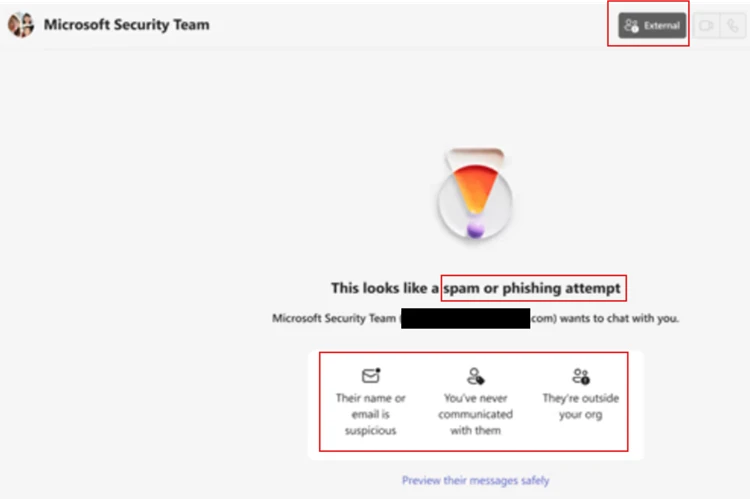
The attack starts simply. A threat actor, operating from a separate Microsoft tenant, sends an unsolicited Teams message to a target employee while posing as internal IT support staff.
Since the contact arrives through a familiar collaboration platform rather than a suspicious email, many employees instinctively lower their guard.
The attacker then convinces the victim to ignore built-in external contact warnings and approve a remote assistance session through Microsoft Quick Assist.
Once this step is completed, the attacker has full interactive control of the victim’s device, usually in under a minute.
Microsoft Defender Security Research analysts identified this intrusion playbook, noting that the attack relies entirely on human-operated decisions rather than traditional software exploits.
Researchers highlighted that this attack chain blends into routine IT activity, making it very difficult to detect without proper event correlation across identity, endpoint, and collaboration telemetry.
Once inside, the attacker wastes no time. Within 30 to 120 seconds of gaining remote access via Quick Assist, they run rapid reconnaissance commands to check user privileges, gather host details, and assess network connectivity.
If the system has sufficient access, the attacker deploys a staged payload into directories like ProgramData and uses DLL side-loading to run malicious code through trusted, digitally signed applications.
Tools such as AcroServicesUpdater2_x64.exe, ADNotificationManager.exe, and DlpUserAgent.exe were observed loading attacker-supplied modules from non-standard paths, allowing malicious code to execute under a trusted application’s identity.
The true scale of damage becomes clear quickly, as attackers used Windows Remote Management (WinRM) to pivot toward high-value targets like domain controllers and used the file-sync tool Rclone to transfer sensitive business documents to external cloud storage.
How DLL Side-Loading Enables Persistent Control
The core infection mechanism in this campaign is DLL side-loading, a technique where attackers exploit the way Windows loads application support libraries.
When a legitimate, digitally signed application starts, Windows searches for required DLL files in specific folder locations.
Attackers place their own malicious DLLs in those same paths, causing the trusted application to unknowingly load and execute the attacker’s code in its place.
In this campaign, sideloaded modules acted as intermediary loaders that decrypted hidden configuration data stored inside the Windows registry rather than writing anything suspicious to disk.
This behavior closely aligns with intrusion frameworks like Havoc, which use registry-backed storage to preserve encrypted command-and-control (C2) configuration across system reboots and remediation attempts.
Since this activity runs inside a trusted, vendor-signed process, conventional security tools often struggle to flag it as malicious.
Once the C2 channel was active, the compromised process began sending encrypted outbound HTTPS traffic over TCP port 443 to attacker-controlled cloud infrastructure, blending into regular business network activity.
Attackers also installed additional remote management software as a secondary access channel and leveraged WinRM sessions to move laterally across the network toward identity systems.
Organizations should take the following actions to reduce exposure from this attack type.
- Treat unsolicited external Teams contact from claimed IT staff as suspicious and verify through known internal channels first.
- Restrict Quick Assist and remote management tools to authorized IT roles only.
- Enable Attack Surface Reduction (ASR) rules and Windows Defender Application Control (WDAC) to prevent DLL sideloading from user-writable locations like ProgramData and AppData.
- Enforce Conditional Access requiring MFA and compliant devices for all administrative sessions.
- Enable Safe Links for Teams and Zero-hour Auto Purge (ZAP) to retroactively catch malicious messages.
- Restrict WinRM to authorized management workstations and monitor for Rclone or similar data-sync tools in the environment.
- Train employees to identify external tenant indicators in Teams and set up a verbal authentication phrase between helpdesk staff and end users.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.