Google Drive Gets Ransomware Detection & File Restoration
Ransomware detection and file restoration features are now generally available for Google Drive, Google announced. Originally launched in beta in September 2025, the updated security controls offer...
Ransomware detection and file restoration features are now generally available for Google Drive, Google announced.
Originally launched in beta in September 2025, the updated security controls offer organizations enhanced defenses against malware attacks targeting local machines and cloud synchronization.
The updated artificial intelligence model driving this release features significant performance improvements. The system now detects 14 times as many infections as the beta version.
It successfully identifies a broader range of ransomware encryption signatures. It executes these detections much faster, effectively minimizing the window of opportunity for threat actors to compromise data.
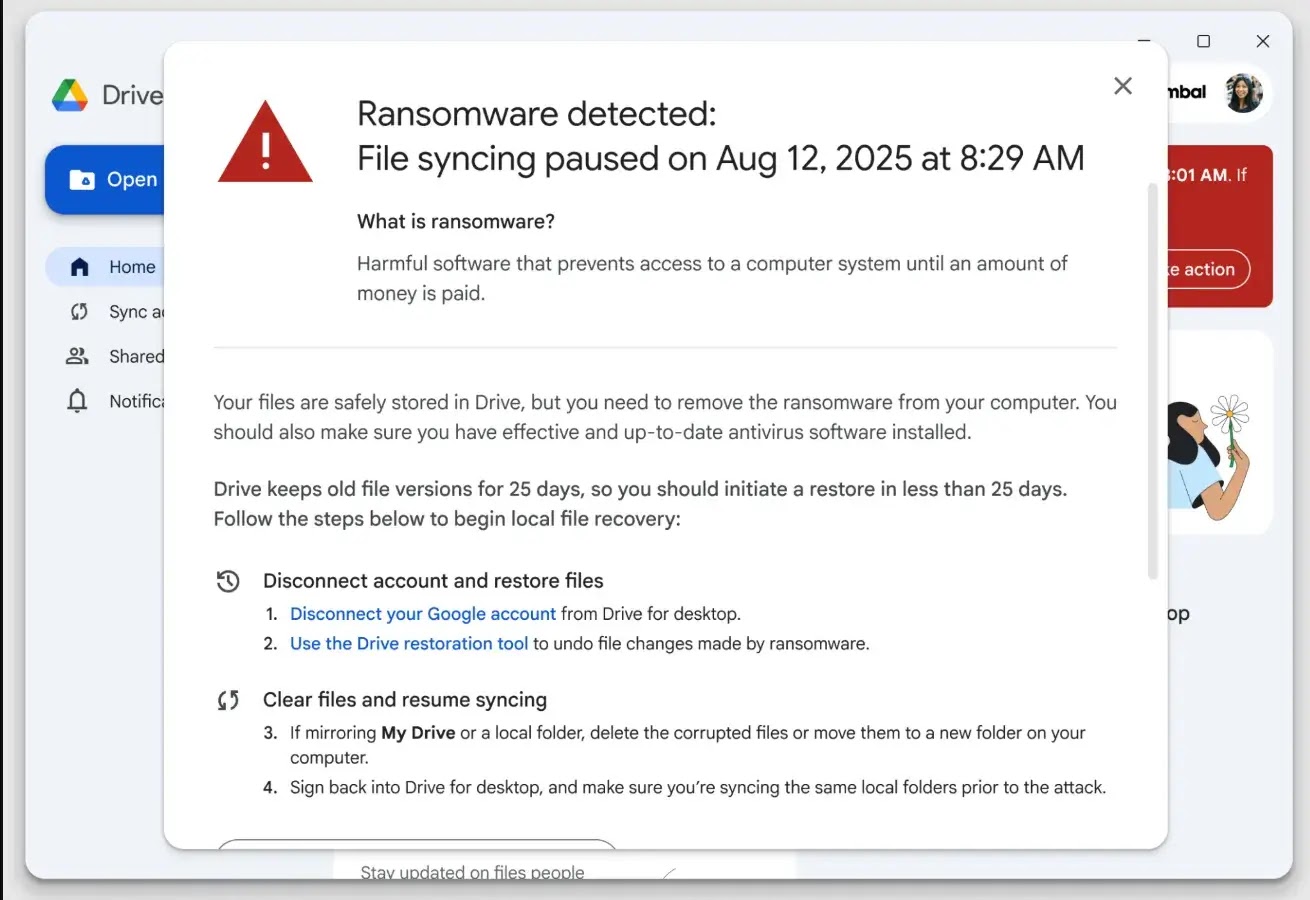
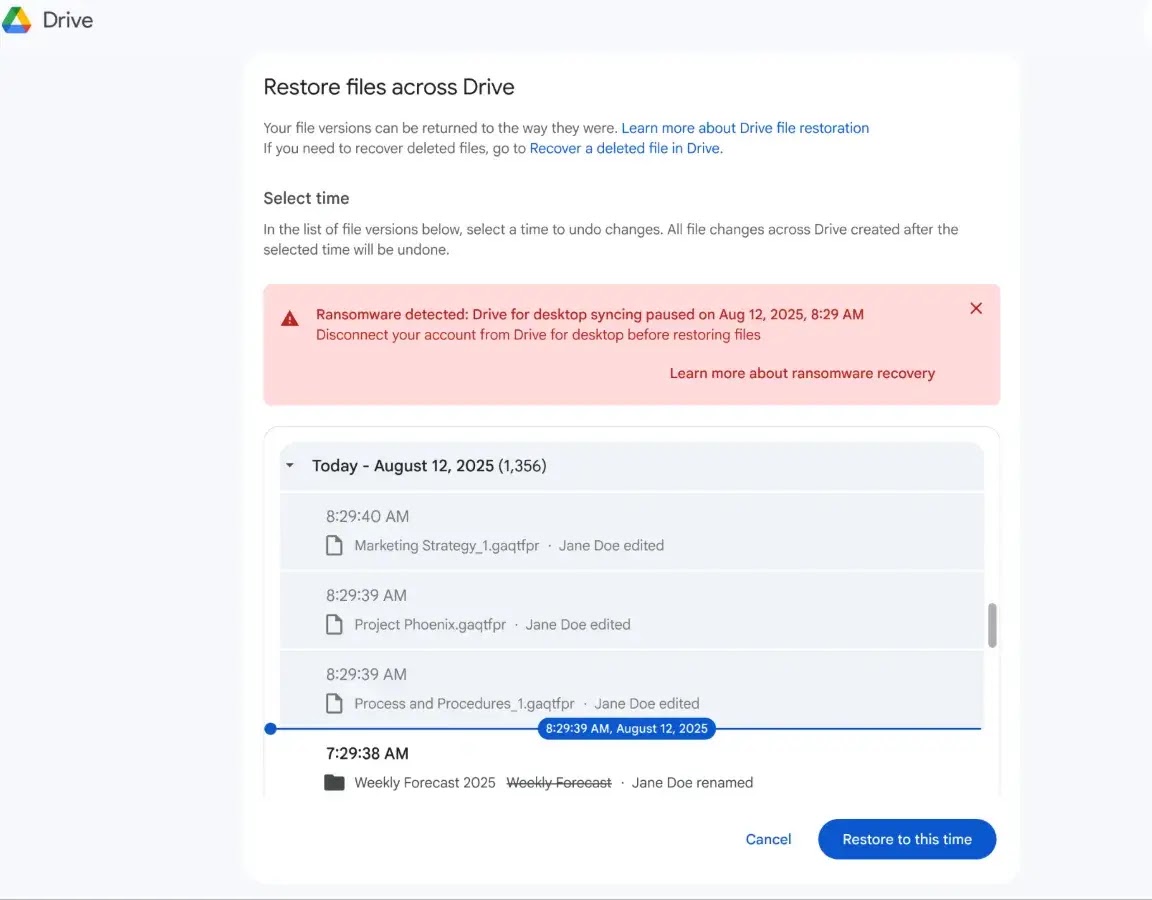
The core defense mechanism relies on the Google Drive for the desktop application. When the software detects ransomware behavior on a local endpoint, it immediately pauses file synchronization.
This automated response prevents newly encrypted files from being uploaded to the Google Workspace environment and from overwriting healthy cloud data.
New Ransomware Protection Capabilities
To receive local desktop alerts during an incident, users must run the Google Drive for desktop version 114 or later.
Older versions will still sever the synchronization connection during an attack, but they will not display the pop-up notifications.
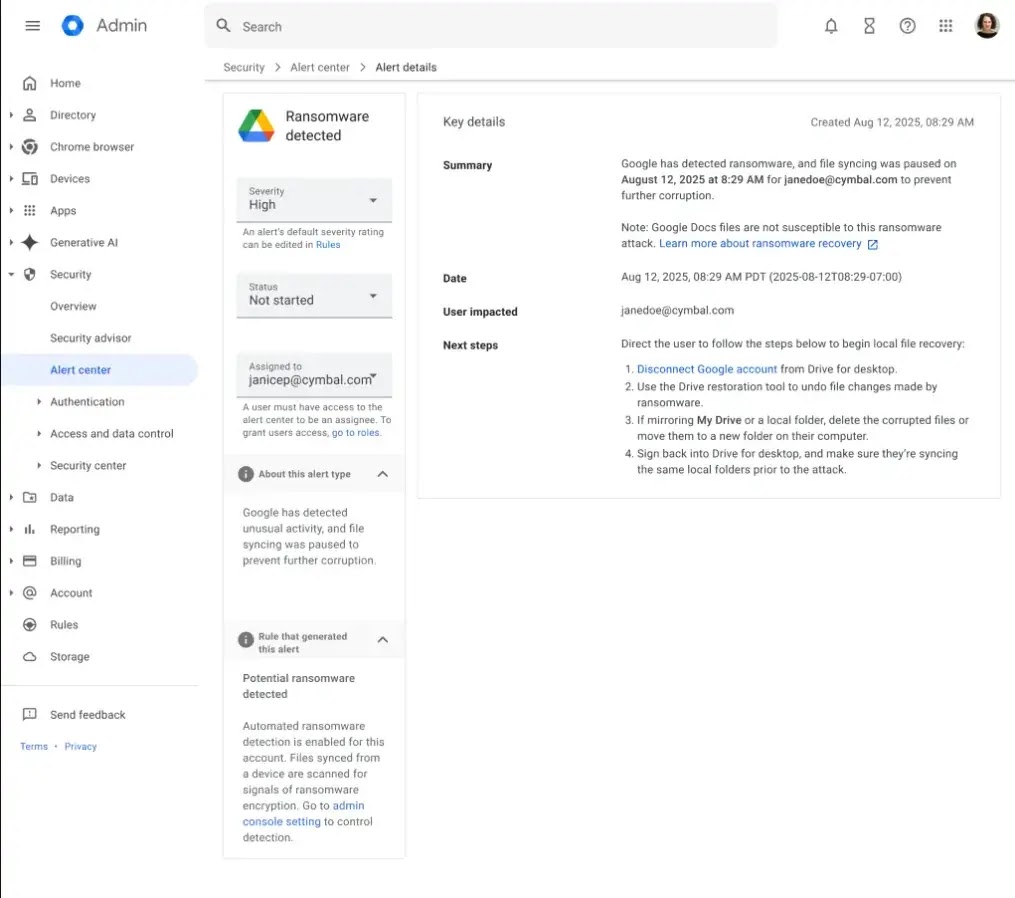
When a detection event occurs, the platform automatically dispatches warning emails to both the affected end-user and the domain administrators.
Security teams can also track these incidents through dedicated alerts generated in the Admin console security center.
Following a contained ransomware attack, the newly introduced file restoration interface allows users to recover their data efficiently.
Victims can select multiple compromised files and revert them in bulk to their pre-infection versions.
This capability accelerates incident recovery times and provides a reliable mechanism to restore access without submitting to extortion demands.
- AI-Powered Detection: Detects 14× more ransomware infections with faster and broader coverage.
- Automated Threat Isolation: Instantly pauses sync to protect Google Workspace data.
- Real-Time Alerts: Notifies users and admins via desktop popups, email, and Admin console.
- Version-Aware Protection: Enables full alerts on Drive for desktop v114+ while older versions still stop sync.
- Bulk File Restoration: Allows multiple files to be reverted to pre-infection versions quickly.
- Improved Recovery Workflow: Provides a streamlined interface for faster incident response.
- Endpoint & Cloud Integration: Secures both local machines and Google Drive simultaneously.
Google reports that thousands of users have successfully tested this recovery tool during the beta phase.
These real-world tests demonstrated the tool’s scalability and reliability during post-incident response operations.
Deployment and Availability
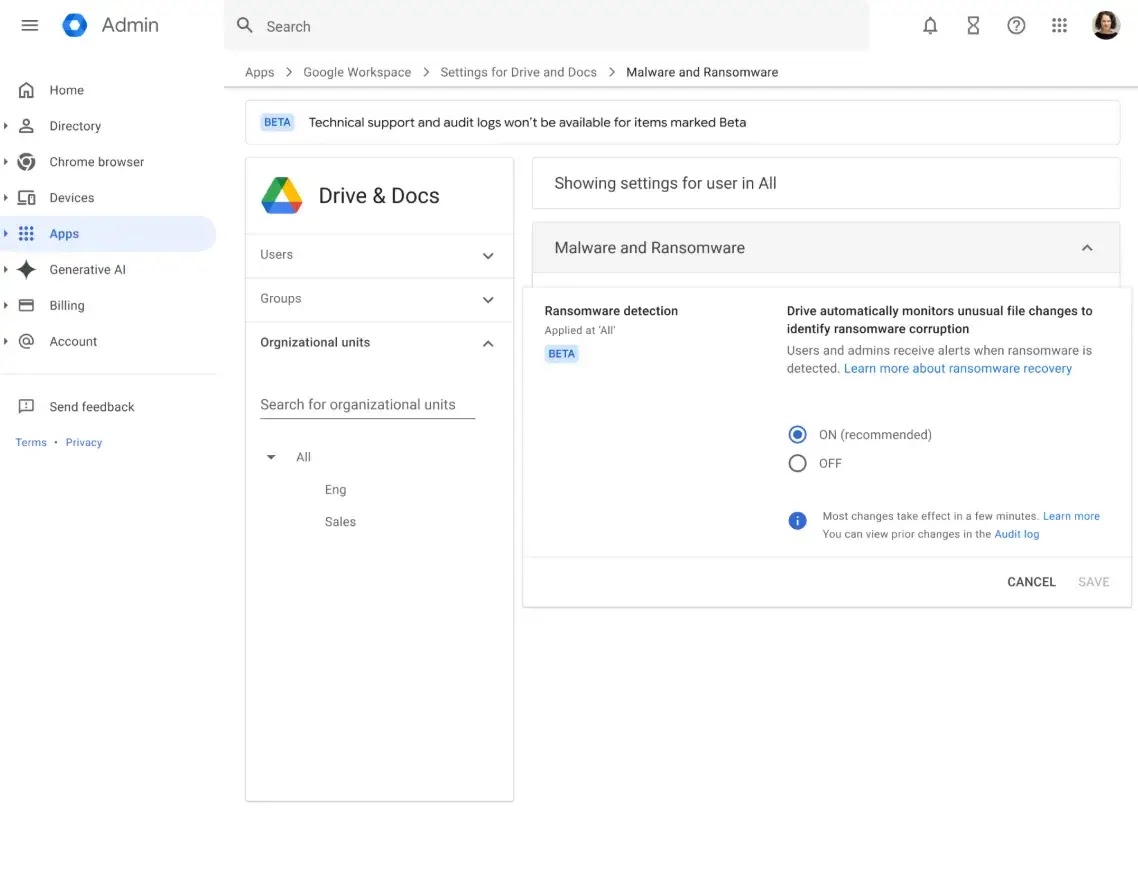
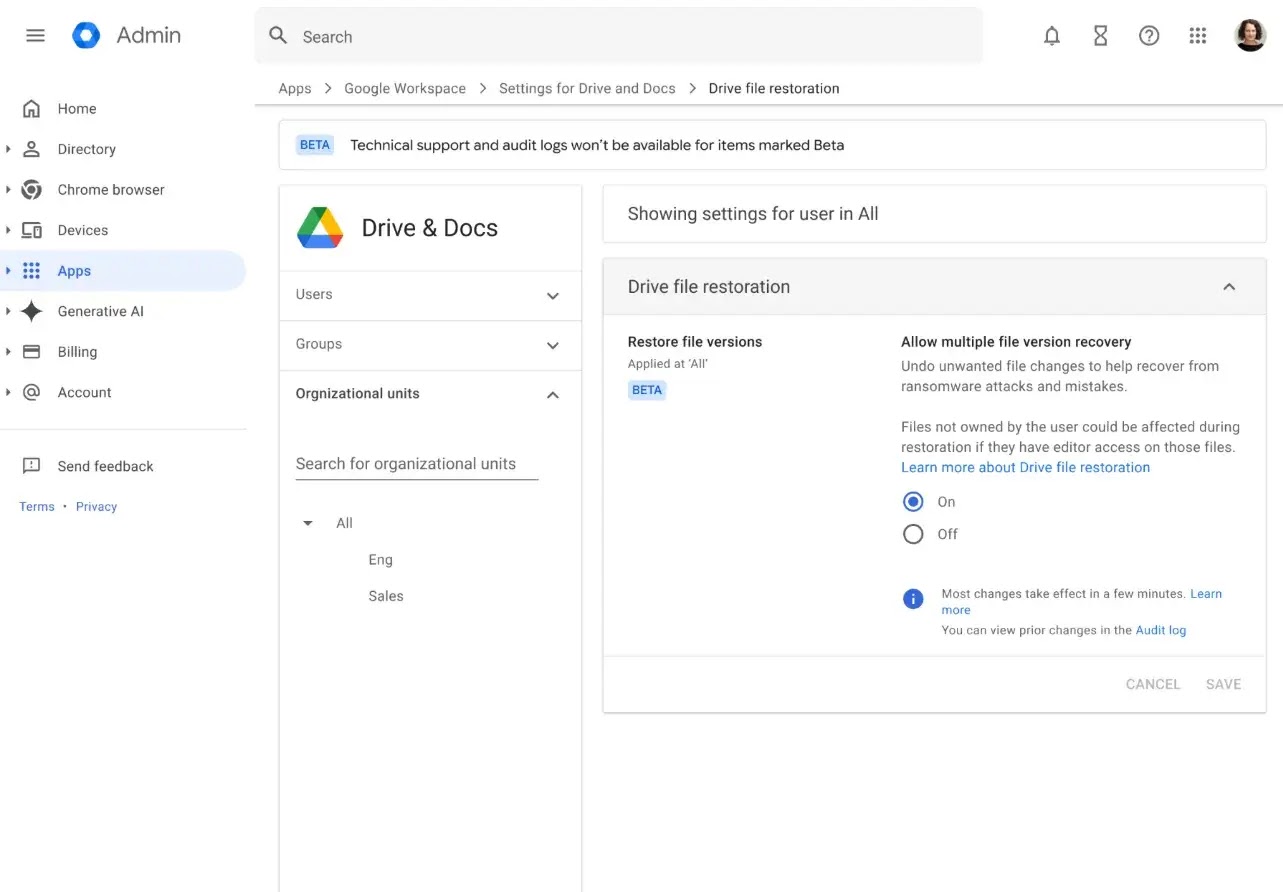
Both the detection and restoration features are enabled by default for organizations.
Administrators can manage these configurations at the Organizational Unit level in the Google Workspace Admin console, under Drive and Docs settings.
Availability depends on the specific Google account type and licensing tier:
- File restoration is accessible to all Google Workspace customers, Individual subscribers, and personal Google accounts.
- Ransomware detection is supported for Business Standard and Plus editions.
- Enterprise Starter, Standard, and Plus tiers include the automated detection capabilities.
- Education Standard and Plus, alongside Frontline Standard and Plus, also receive the detection tools.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.