Crimson Collective Disconnected Brightspeed Home Internet Users
An emerging extortion group,
An emerging extortion group, Collective Disconnected Brightspeed-fiber-broadband/”>Crimson Collective Disconnected Brightspeed. The group asserts it stole data from over 1 million residential customers and Disconnected Brightspeed Home internet service.
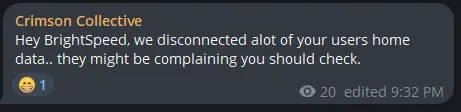
The group posted screenshots on Telegram detailing the alleged compromise and urging Brightspeed employees to “read their mails fast.”
On January 4, 2026, Crimson Collective announced possession of extensive customer datasets from Brightspeed, a major ISP serving rural and suburban areas across 20 states.
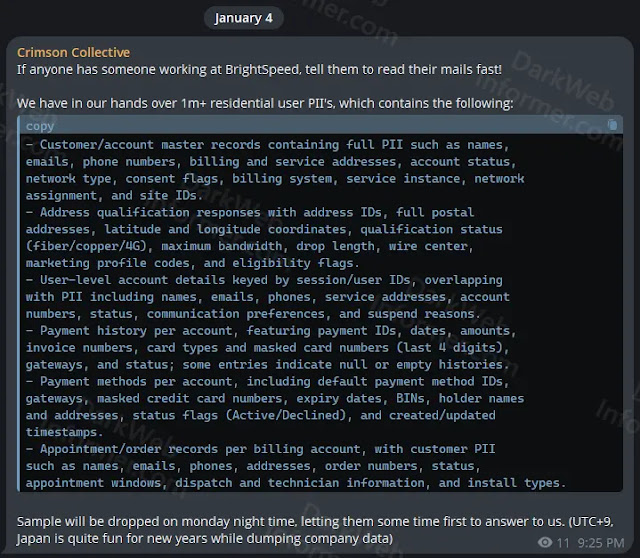
The post listed compromised records, including customer master files with full PII such as names, emails, phone numbers, billing/service addresses, account status, and network details like fiber/copper/4G types, bandwidth limits, and geolocation coordinates.
Additional data encompasses payment histories (IDs, amounts, masked card numbers with last four digits, expiry dates, BINs, holder info), appointment records with technician dispatch details, marketing profiles, and suspension reasons.
The actors released data samples on January 5 as threatened, and claimed a “sophisticated attack” enabling user disconnections from ISP service, which was later clarified as home internet, not mobile.
They are offering the full dataset for three Bitcoin (about $276,370), with plans to leak it online within a week if unsold.
Brightspeed’s Response
Brightspeed confirmed it is “investigating reports of a cybersecurity event” and takes network security seriously, promising updates to customers, staff, and authorities.
Spokesperson Gene Rodriguez Miller emphasized rigorous threat monitoring but declined to provide specifics on the claims. No evidence of service outages has been widely reported, though the group alleges proactive disruptions.
Crimson Collective gained notoriety in 2025 for breaching Red Hat’s GitLab repositories, exfiltrating 570GB of data that later impacted 21,000 Nissan customers’ PII.
They collaborated with Scattered Lapsus$ Hunters (ShinyHunters-linked) for extortion and have targeted AWS environments via credential abuse. The group has not disclosed intrusion methods for Brightspeed but hinted at ignored pre-disclosure emails.
Affected customers face risks of phishing, identity theft, and targeted attacks from exposed PII and partial payment data, though full cards or passwords were not claimed stolen.
Cybersecurity experts urge monitoring accounts and enabling MFA, as the incident highlights vulnerabilities in telecom infrastructure. Federal probes may follow, given Brightspeed’s critical role. As of January 7, no full breach confirmation exists, but samples appear authentic per the researcher’s cross-checks.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.