Christmas Phishing Surge: Docusign Spoofing Chains Identity
The holiday season marks a significant surge in sophisticated phishing attacks, combining two dangerous tactics: credential harvesting via spoofed Docusign notifications and identity theft through...
The holiday season marks a significant surge in sophisticated phishing attacks, combining two dangerous tactics: credential harvesting via spoofed Docusign notifications and identity theft through fraudulent loan application forms.
These coordinated campaigns exploit the seasonal chaos of overloaded inboxes and financial stress that peaks during Christmas Phishingthe New Year period.
Threat actors are taking advantage of the trust users place in familiar business workflows, particularly document review processes, to compromise both personal and corporate data on an unprecedented scale.
The attack campaign relies on convincing users that they need to review completed documents during the busy holiday period.
Fraudsters send emails appearing to come from Docusign with authentic-looking branding and footers, but these messages originate from suspicious domains like jritech.shop rather than legitimate Docusign servers.
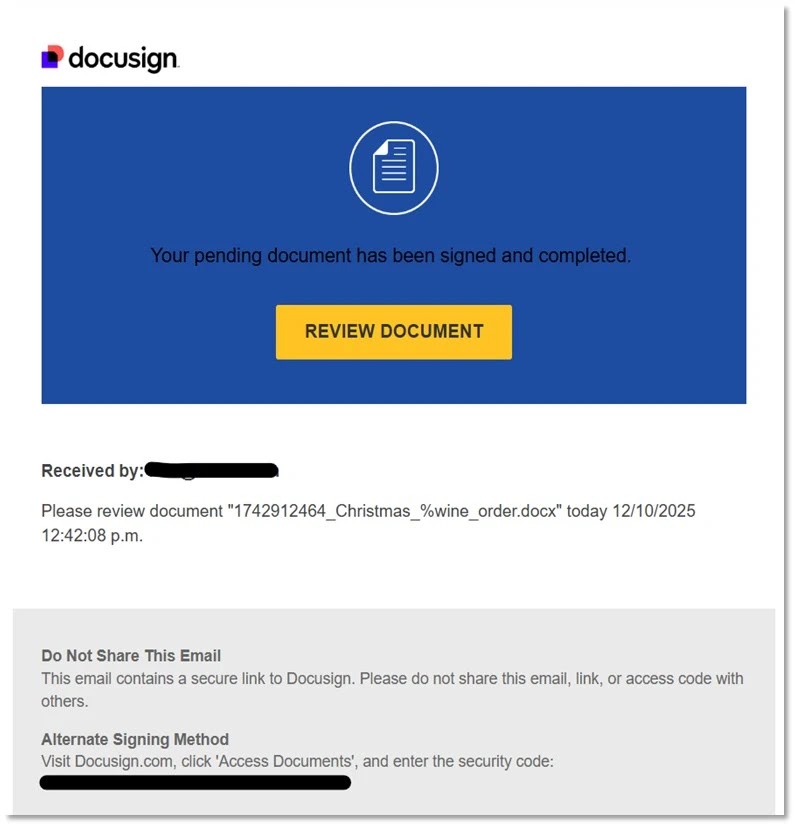
The emails reference fake Christmas-themed documents such as wine orders, creating a sense of legitimacy that encourages quick clicks without verification.
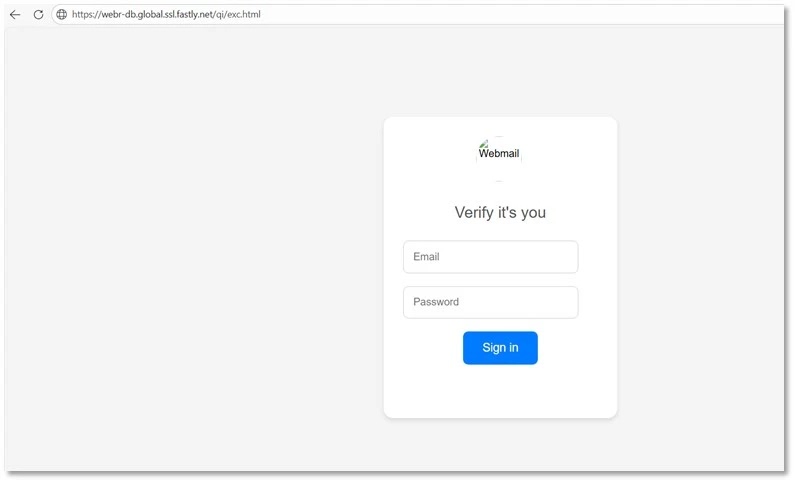
When users click the Review Document button, they are redirected through multiple hosting platforms including Fastly, Glitch, and Surge.sh before landing on credential harvesting pages designed to steal corporate email logins.
Forcepoint analysts identified this sophisticated threat chain during their X-Labs research in late December, tracking how the attacks are structured and discovering the supporting infrastructure that enables the fraud.
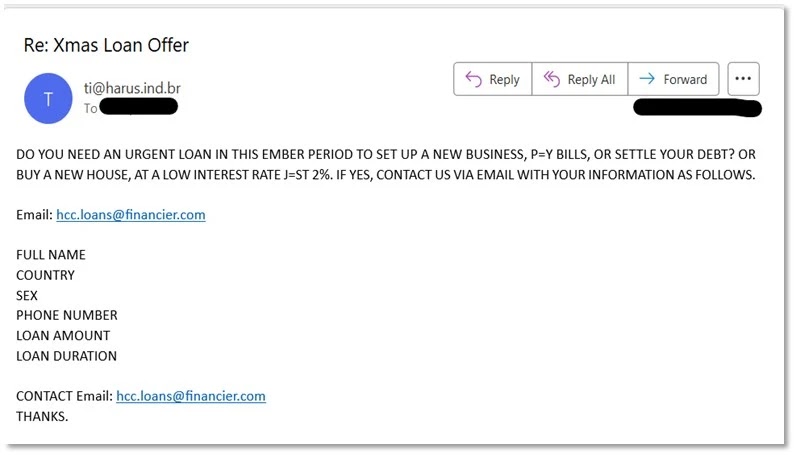
The researchers noted that the second wave of the campaign introduces a separate but complementary attack vector targeting personal financial information rather than corporate credentials.
These holiday loan spam emails promise quick cash, low interest rates, and urgent approvals to capture sensitive personal data.
The core attack mechanism involves a multi-stage identity theft questionnaire hosted on christmasscheercash.com that walks victims through a deceptive data collection process.
The form begins innocuously by asking how much money the victim needs, with options ranging from 100 to 50,000 dollars.
It then gradually progresses to requesting basic information like name, email, and phone number, which appears normal for any loan application.
The questionnaire continues by asking about home ownership, vehicle ownership, employer details, and income information, maintaining the facade of legitimacy throughout this phase.
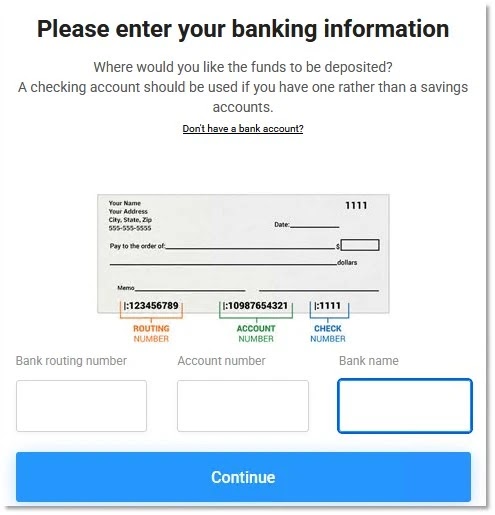
However, the true objective becomes clear in the final stages when the form requests complete banking information. Victims are asked to provide routing numbers, account numbers, and other sensitive details under the pretense of depositing loan funds.
After submission, users are redirected to additional fraud sites like thepersonalfinanceguide.com, which request the same information again and expose victims to endless loan offer spam.
This handoff pattern is standard in identity theft ecosystems designed to maximize data capture and monetization across multiple fraudulent platforms.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.