Chinese Threat Actors Hosted 18,000 Active C2 Servers Across 48
Threat actors linked to Chinese hosting infrastructure have established a massive network of over 18,000 active command-and-control (C2) servers, spanning 48 hosting providers, in recent months. This...
Threat actors linked to Chinese hosting infrastructure have established a massive network of over 18,000 active command-and-control (C2) servers, spanning 48 hosting providers, in recent months.
This widespread abuse highlights a serious issue in how malicious infrastructure can hide within trusted networks and cloud services.
Traditional threat hunting methods that focus on individual IP addresses or domain names often miss the bigger picture because attackers constantly change these indicators to avoid detection.
The research reveals that these C2 servers make up about 84 percent of all malicious activity observed within Chinese hosting environments during the three-month analysis period.
Phishing infrastructure accounts for around 13 percent, while malicious open directories and public indicators of compromise together represent less than 4 percent of detected threats.
This shows that command-and-control operations dominate the threat landscape, with attackers preferring stable infrastructure that can coordinate ongoing campaigns across multiple targets.
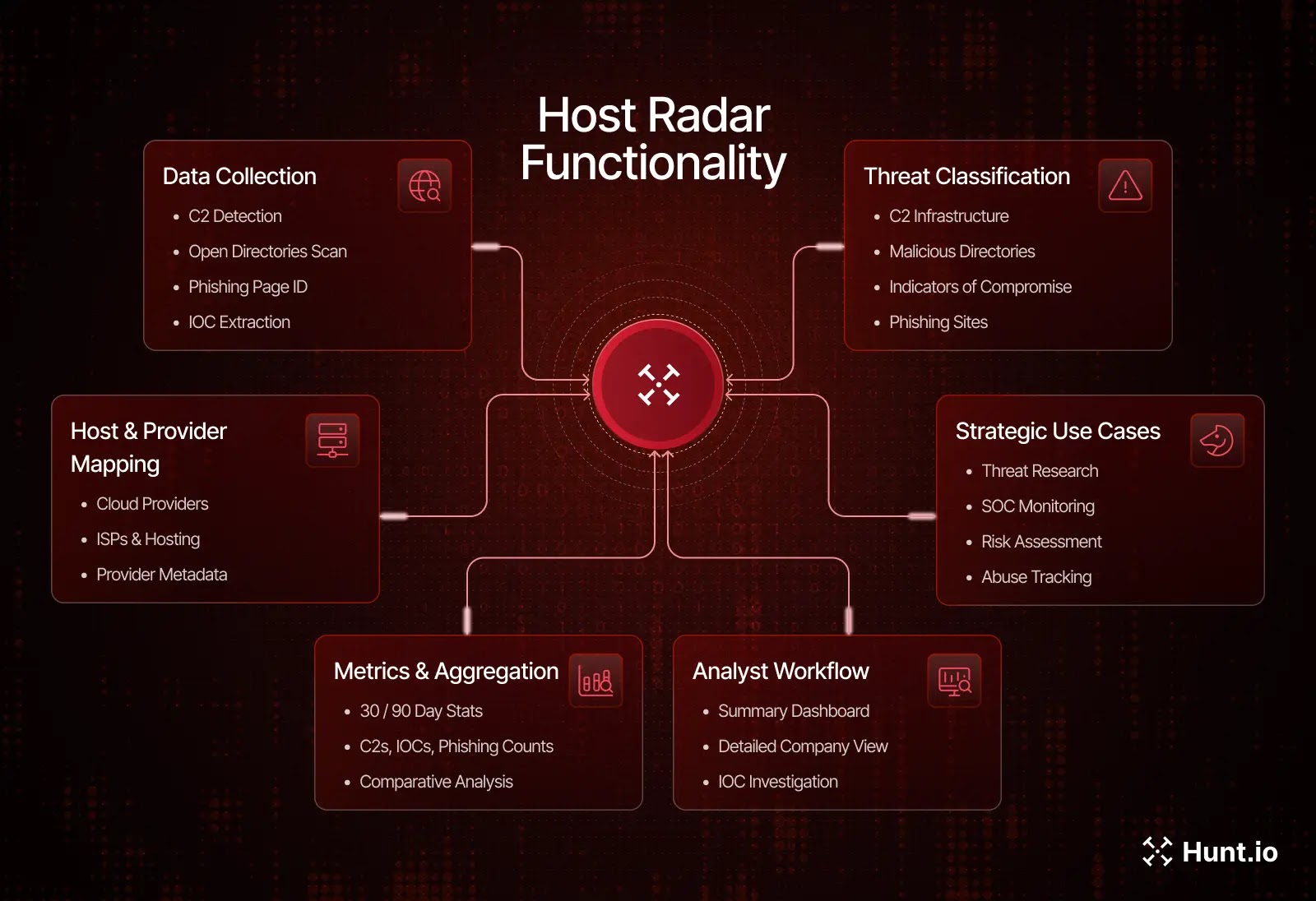
Hunt.io analysts identified this extensive infrastructure network using their Host Radar platform, which combines C2 detection, phishing identification, open directory scanning, and indicator extraction into a single intelligence system.
Rather than treating each malicious artifact as isolated, the platform maps these threats back to the hosting providers and network operators where they exist. This approach reveals long-running abuse patterns even when individual IP addresses change frequently.
China Unicom emerged as the largest host of malicious infrastructure, accounting for nearly half of all observed C2 servers with approximately 9,000 detections.
Alibaba Cloud and Tencent each hosted around 3,300 C2 servers, showing that major cloud platforms are heavily targeted by threat actors who value their rapid provisioning and high availability.
These three providers alone represent the majority of detected malicious command-and-control infrastructure within China.
Infrastructure Concentration and Malware Distribution
The malware families operating through this infrastructure show clear patterns of repeated framework abuse. Mozi botnet dominates with 9,427 unique C2 IP addresses, representing more than half of all observed command-and-control activity.
The ARL framework follows with 2,878 C2 endpoints, suggesting extensive misuse of post-exploitation and red-team tooling for malicious purposes.

Cobalt Strike appears with 1,204 detections, while Vshell and Mirai round out the top five with 830 and 703 C2 servers respectively.
This concentration means defenders can focus monitoring efforts on shared infrastructure patterns rather than chasing individual malware variants that constantly evolve.
The data shows that cybercrime operations, botnet infrastructure, and state-linked espionage tools coexist within the same hosting environments.
Campaigns ranging from commodity remote access trojans to sophisticated APT operations leverage these providers, creating a complex threat ecosystem where traditional indicator-based defenses struggle to maintain effectiveness.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.