Akira Lookalike Ransomware Targets Windows Users in South
A dangerous new ransomware campaign has emerged in South America, specifically targeting Windows users. This sophisticated strain closely mimics the notorious Akira ransomware. While the two may...
A dangerous new ransomware campaign has emerged in South America, specifically targeting Windows users. This sophisticated strain closely mimics the notorious Akira ransomware.
While the two may appear nearly identical on the surface, this new threat is built on an entirely different foundation — one that quietly borrows from another notorious ransomware family to carry out its attacks.
The campaign has raised serious concern within the cybersecurity community because of how convincingly it mimics Akira.
Victims who fall prey to this threat find their files encrypted and their systems held hostage by a ransom note that looks almost identical to one from Akira — complete with matching Tor URLs and similar wording.
The deception is deliberate, designed to mislead victims and possibly even seasoned investigators into misidentifying the actual threat actor behind the attack.
ESET Research analysts identified this campaign after closely examining the ransomware’s behavior and inner workings, confirming that despite its Akira-like appearance, the encryptor powering the malware is actually Babuk-based.
This discovery was significant, as Babuk is a separate ransomware family whose source code was leaked publicly years ago and has since been repurposed by various threat actors.
ESET Research noted that the operator behind this campaign is using a Babuk-based encryptor that appends the .akira extension to encrypted files, while also dropping a ransom note that mirrors Akira both in its Tor URLs and overall content.
The regional targeting of South America marks a notable shift in ransomware geography. Historically, ransomware groups have focused heavily on North American and European organizations, where larger volumes of sensitive data and higher ransom payment rates make attacks more profitable.
This latest campaign suggests that threat actors are actively expanding their reach into South American markets, possibly using this lookalike strain as a testing ground before escalating to larger or more complex operations.
The timing also aligns with a broader global trend of ransomware impersonation. Cybercriminals have increasingly adopted the tactic of mimicking well-established ransomware brands to exploit the fear and brand recognition those names carry.
By disguising their tools under the Akira name, the operators of this campaign can capitalize on Akira’s established reputation without being directly affiliated with the original group.
Inside the Babuk-Based Encryptor
At the core of this campaign lies a Babuk-derived encryptor, which provides the malware with its actual file encryption capability.
Babuk’s source code was leaked publicly years ago, and since then it has been repeatedly recycled by various threat actors to create new ransomware variants with minimal development effort.
In this case, the operator took that leaked code and dressed it up to resemble Akira — adding the .akira file extension and crafting a ransom note that closely follows Akira’s known communication style, including dark web Tor-based links for victim negotiation.
What makes this encryptor particularly effective is how seamlessly the disguise holds together.
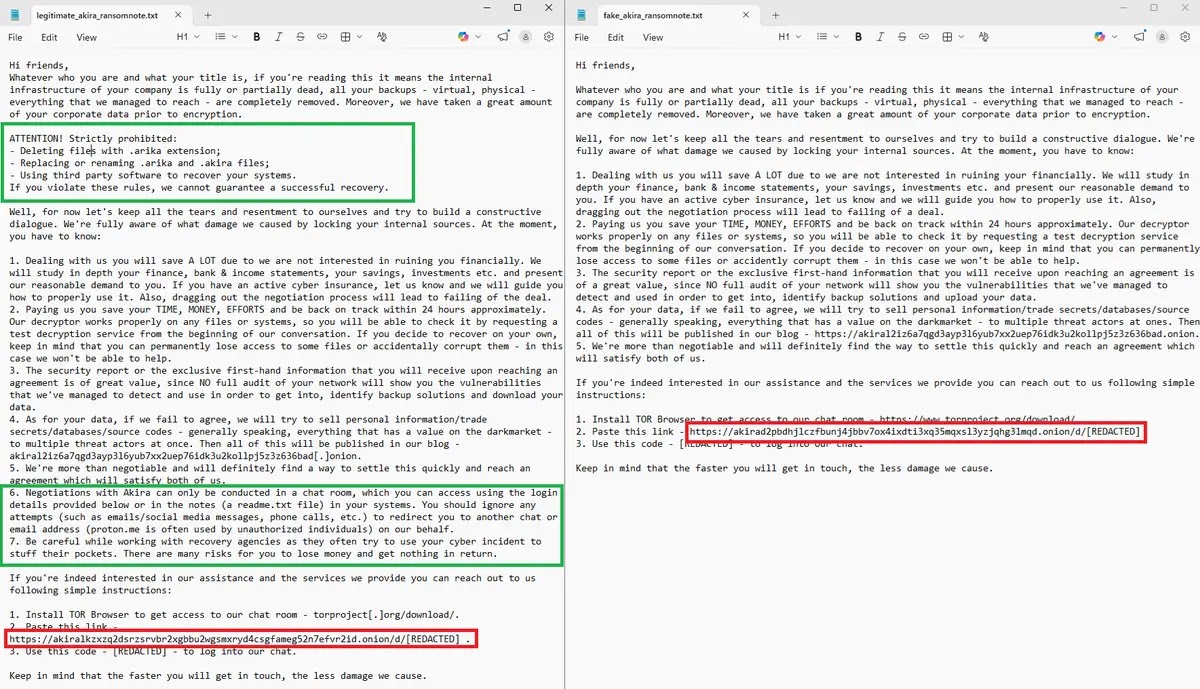
The ransom note dropped on the victim’s system mirrors Akira’s formatting and language with enough accuracy to confuse both victims and security teams.
Victims are pointed toward Tor-based URLs that closely resemble those used by the real Akira group, making it easy for organizations to misattribute the attack and potentially delay a proper and timely response.
Organizations across South America and beyond should take immediate steps to reduce their exposure to this type of threat.
Keeping all Windows systems fully patched and updated is a basic but critical step. Network segmentation can help contain damage if ransomware reaches a system.
Maintaining regular offline backups ensures recovery without paying ransom. Security teams should monitor endpoints for unexpected .akira file extensions as an early warning sign.
It is also important to avoid attributing attacks solely based on ransom note content, as this campaign clearly demonstrates how effective and misleading ransomware impersonation tactics can truly be.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.