Microsoft Edge, Windows 11, LiteLLM H Hacked Pwn2Own
Pwn2Own Berlin 2026 commenced with a surge of zero-day exploits, targeting modern browsers, operating systems, and emerging AI platforms. On Day One alone, security researchers successfully hacked...
Pwn2Own Berlin 2026 commenced with a surge of zero-day exploits, targeting modern browsers, operating systems, and emerging AI platforms.
Table Of Content
On Day One alone, security researchers successfully hacked Microsoft Edge, Windows 11, and LiteLLM, earning a total of $523,000 for 24 unique vulnerabilities.
The results highlight a growing reality that AI ecosystems and core enterprise technologies are increasingly exposed to complex, chained attacks.
Edge Sandbox Escape
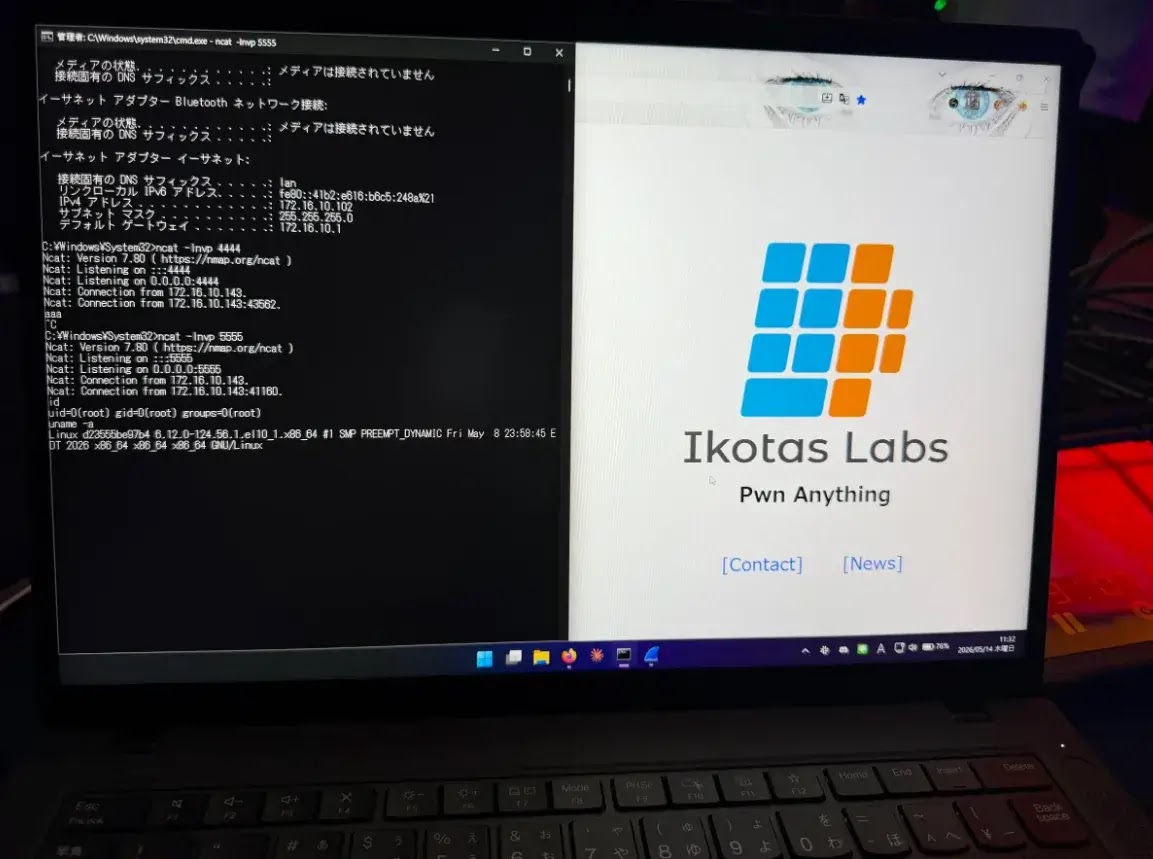
One of the most impactful demonstrations came from Orange Tsai of the DEVCORE Research Team, who executed a sophisticated sandbox escape against Microsoft Edge.
The exploit chained four distinct logic vulnerabilities, turning minor flaws into a full system compromise.
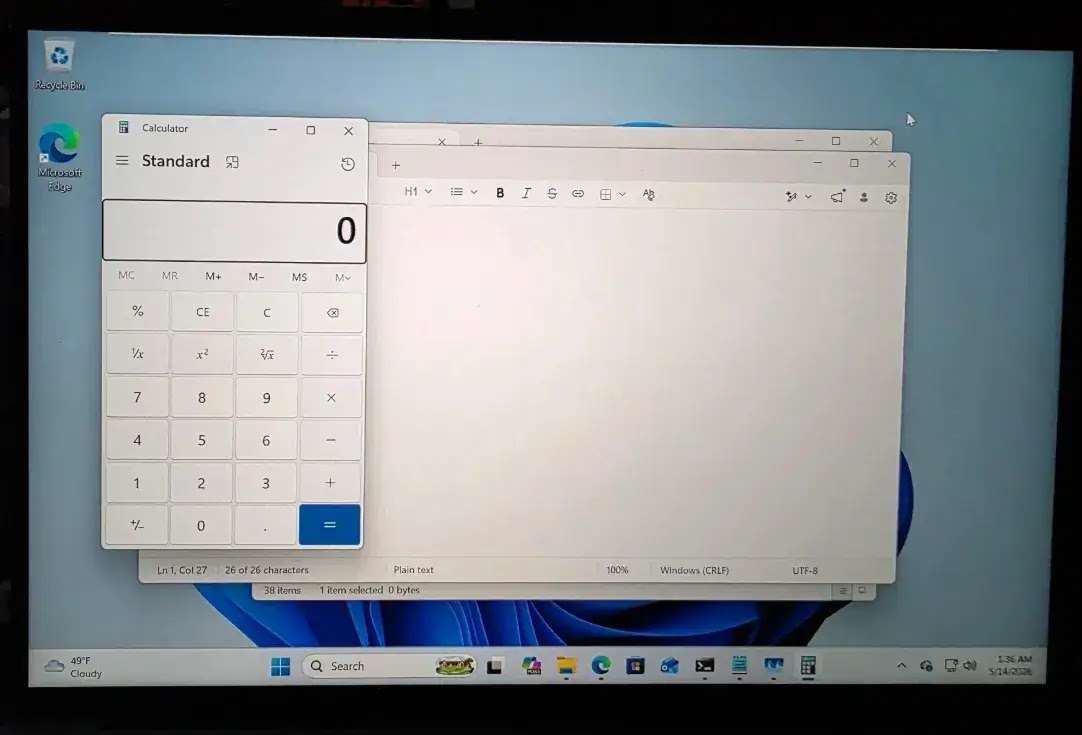
This advanced technique earned $175,000 and 17.5 Master of Pwn points, placing DEVCORE in the lead.
The attack underscores how modern browser security can still be bypassed when multiple weaknesses are combined strategically.
Windows 11 Privilege Escalations
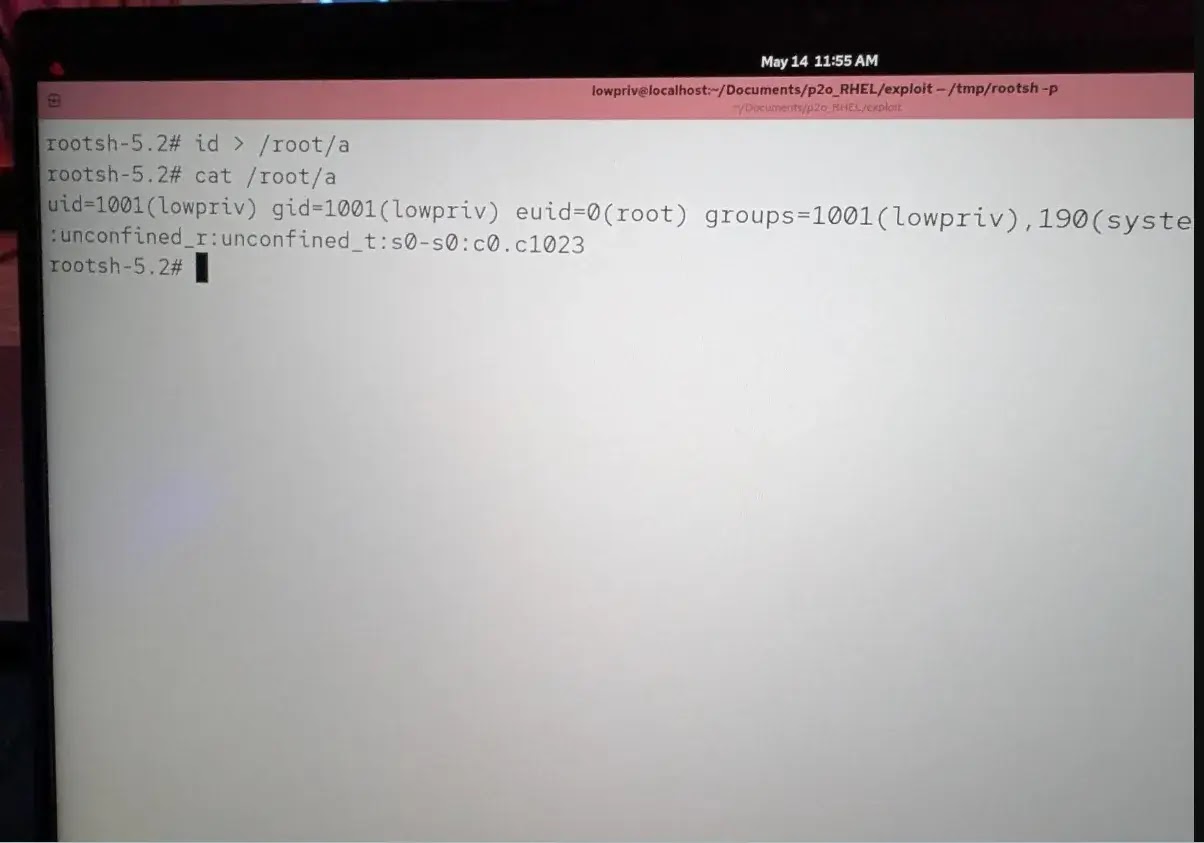
Microsoft Windows 11 emerged as another major target, with several successful privilege escalation attacks throughout the day.
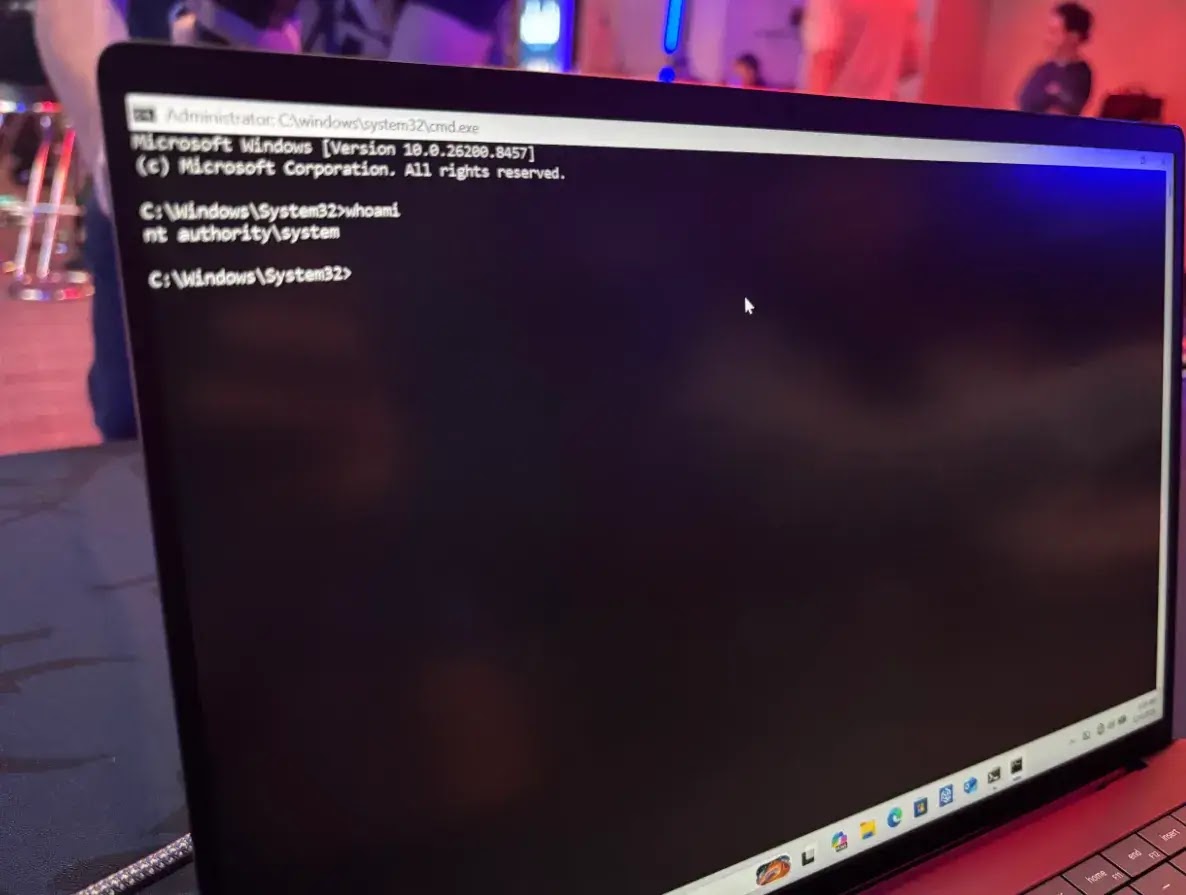
Additional researchers later demonstrated attacks using heap-based buffer overflows and use-after-free vulnerabilities.
Angelboy and TwinkleStar03 of DEVCORE exploited an improper access control flaw to gain elevated privileges.
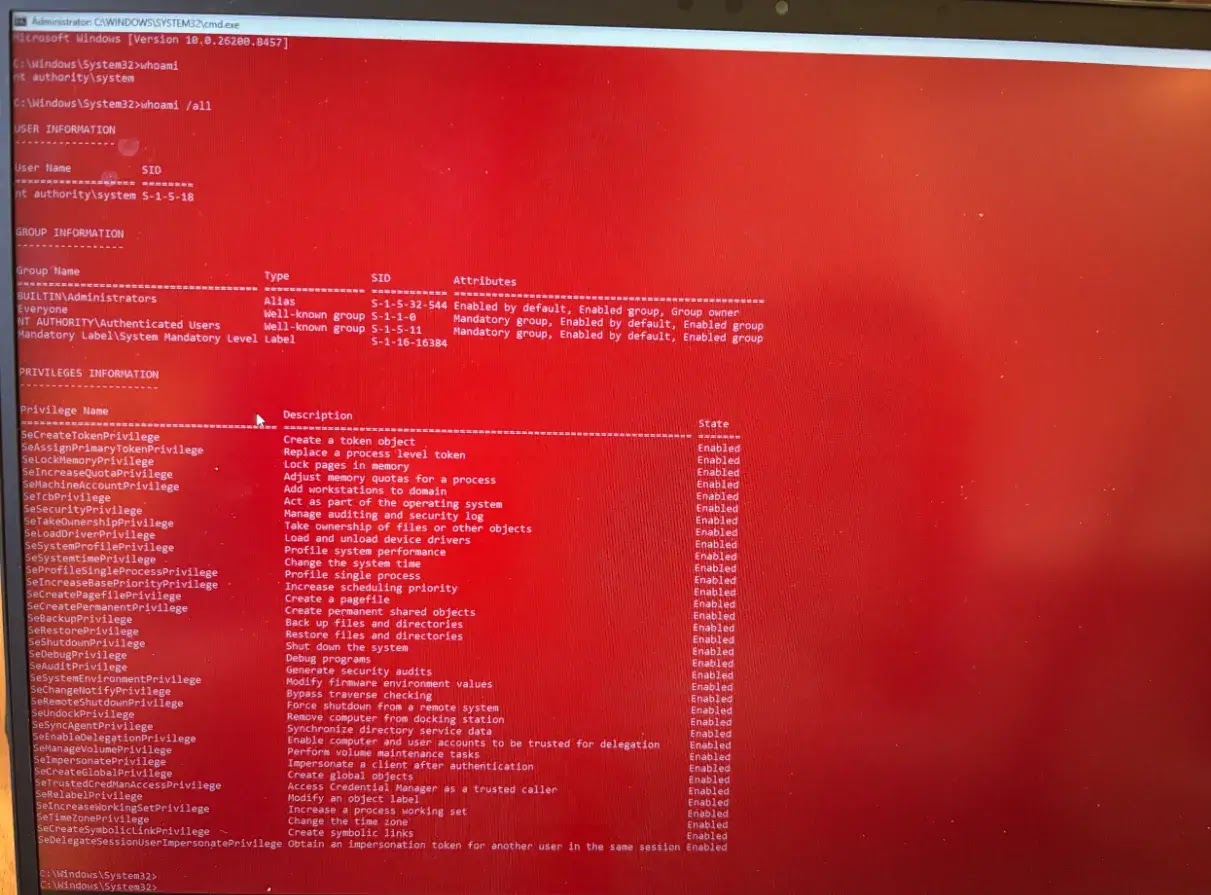
These repeated compromises show that even mature operating systems remain vulnerable to memory corruption and access control issues.
LiteLLM Exploited
AI infrastructure faced serious scrutiny, with LiteLLM falling to a full-chain exploit by researcher k3vg3n.
The attack combined three vulnerabilities, including Server-Side Request Forgery (SSRF) and code injection, allowing full system takeover.
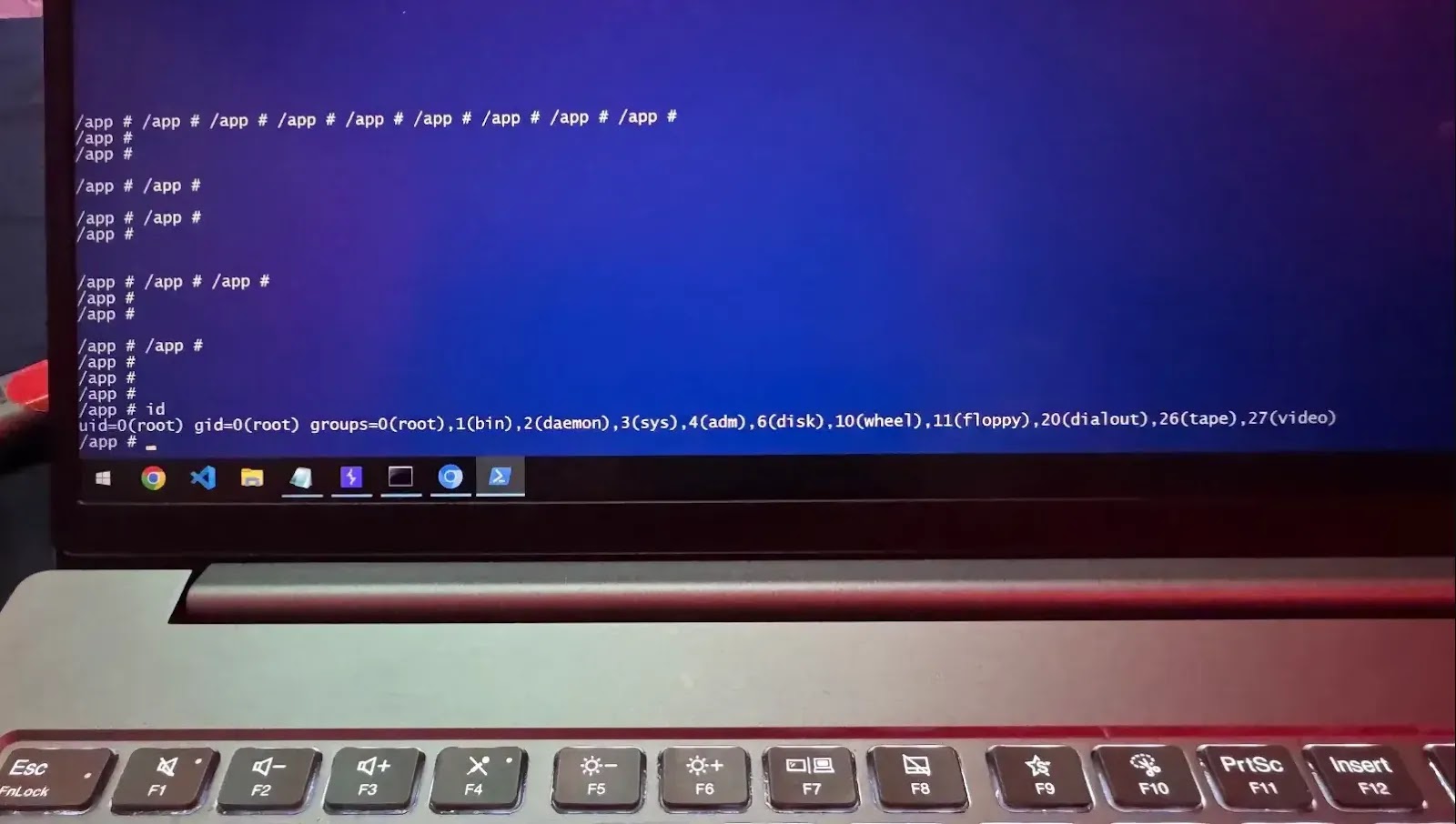
The exploit earned $40,000 and highlighted how AI frameworks, especially those handling external inputs and APIs, can introduce critical security gaps if not properly hardened.
AI and Developer Tools Under Pressure
Other AI-focused targets also experienced successful compromises. OpenAI Codex was exploited using a CWE-150 flaw by Compass Security researchers.
NVIDIA’s Megatron Bridge was breached multiple times due to overly permissive allow lists and path-traversal vulnerabilities.
Meanwhile, IBM X-Force researchers successfully exploited a single bug in the NV Container Toolkit.
These findings reinforce concerns that AI and developer tooling ecosystems are still maturing in terms of secure design and threat resilience.
Not every attempt succeeded. Several researchers failed to exploit targets such as OpenAI Codex and Oracle Autonomous AI Database within the time limit.
Additionally, multiple “collision” cases were recorded, where working exploits relied on previously known vulnerabilities.
While still rewarded, these cases highlight a persistent issue: organizations failing to promptly patch known security flaws.
According to Zero Day Initiative, Day One results from Pwn2Own Berlin 2026 reveal a major shift in the threat landscape.
Attackers are no longer focused solely on traditional software but are actively targeting AI platforms, inference engines, and developer tools.
With DEVCORE leading the competition and more high-value targets ahead, the event is expected to uncover even deeper vulnerabilities in the coming days, offering a stark warning to vendors and enterprises alike.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.