Hackers Exploit HWMonitor to Load Malicious Abuse Legitimate
Threat actors are once again exploiting trusted software, turning legitimate tools against their users. A new attack campaign has been uncovered, where HWMonitor, a widely used hardware monitoring...
Threat actors are once again exploiting trusted software, turning legitimate tools against their users. A new attack campaign has been uncovered, where HWMonitor, a widely used hardware monitoring utility developed by CPUID, is being weaponized to silently deliver the STX RAT remote access trojan. This tactic is detailed in
The campaign begins with a trojanized archive distributed through a compromised download link. Victims who click the link receive a ZIP file that appears to contain a legitimate HWMonitor installation package.
Once extracted, the archive drops both the genuine HWMonitor_x64.exe binary and a malicious DLL file named CRYPTBASE.dll into the same folder. Because users generally trust widely used software utilities, the trojanized installer remains an effective and very difficult-to-detect initial access vector.
Analysts at Gurucul, who analyzed this threat in detail, noted that the malicious archive was distributed through a URL hosted on a Cloudflare R2 storage bucket. Their investigation revealed a sophisticated multi-stage execution chain designed to evade detection while delivering the final STX RAT payload entirely in memory, leaving very little forensic trace behind on the infected system.
The overall impact of this campaign is significant and far-reaching. Once the RAT is active on a machine, attackers gain the ability to monitor and capture the victim’s screen, harvest detailed system information, identify installed security products, and establish persistent remote control. The presence of campaign tracking identifiers embedded within the malware strongly suggests the operators are running coordinated, large-scale infection efforts across multiple targets at the same time.
Hackers Abuse Legitimate HWMonitor Binary
The core trick in this attack relies on a well-known technique called DLL sideloading. When HWMonitor_x64.exe launches, Windows looks for CRYPTBASE.dll in the application’s local folder before checking the system path.
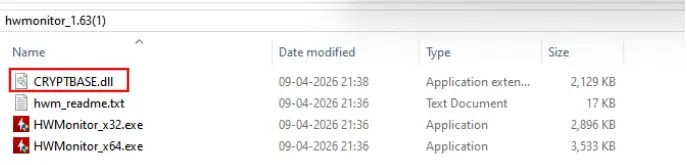
Attackers exploit this predictable behavior by placing their own malicious CRYPTBASE.dll in that same directory, causing the trusted executable to unknowingly load attacker-controlled code instead of the legitimate Windows system library.
Once the malicious DLL is loaded, it spawns two separate threads inside DllMain. The first thread initializes the malicious execution chain, while the second quietly loads the legitimate system DLL to preserve normal application behavior and reduce suspicion. This dual-thread design is deliberate, as it keeps HWMonitor appearing fully functional while the attack runs silently in the background, completely hidden from the victim user.
STX RAT Multi-Stage Payload Delivery
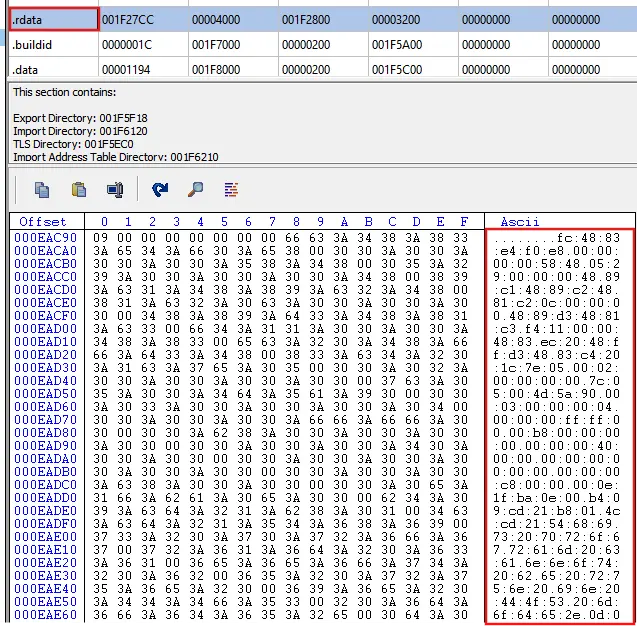
After the sideloading stage completes, the malware enters a multi-stage reflective loading process that drops the final STX RAT payload entirely in memory, never writing any files to disk. The malicious DLL extracts obfuscated data from its .rdata section, allocates executable memory using VirtualAlloc, and passes execution through several decryption stages before reaching the final payload. Because nothing suspicious lands on disk, traditional file-based security detection methods are far less effective against this kind of approach.
STX RAT is packed with capabilities built for long-term surveillance and data theft. It uses API hashing to resolve Windows functions at runtime without exposing readable import table entries, making static analysis significantly harder.
The RAT checks the Process Environment Block for a debugger flag to detect analysis tools, and it also enumerates installed security products including antivirus and EDR solutions such as Avast, Bitdefender, SentinelOne, and CarbonBlack. It silently captures screenshots, collects hostname, username, and OS details, and communicates with its command-and-control server through JSON-based messages over HTTPS.
Security teams are advised to monitor for suspicious DLL loading activity, particularly cases where system DLLs appear to load from application directories rather than the standard Windows system path.
Blocking unsigned or unexpected DLL loads, enabling memory-based threat detection, and watching for unusual outbound HTTPS connections to unfamiliar endpoints are all practical defensive steps. Gurucul SIEM can assist security operations teams by providing visibility into DLL sideloading activity, reflective in-memory execution, and command-and-control traffic patterns tied to campaigns of this nature.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| URL | hxxp://pub-fd67c956bf8548b7b2cc23bb3774ff0c[.]r2[.]dev/hwmonitor_1[.]63[.]zip | Malware distribution URL (trojanized HWMonitor archive) |
| URL | hxxps://welcome.supp0v3[.]com/d/callback | STX RAT command-and-control callback endpoint |
| File Hash (MD5) | mf1619fdif (HWMonitor_1.63 malware.zip) | Trojanized ZIP archive |
| File Hash (MD5) | ab2ffaagj7bfebf3fh (STXBASE.dll) | Malicious sideloaded DLL (Stage 2 Loader) |
| File Hash (MD5) | DmS3lj37mDhh3Bj52B2EfkAiMf1dNi9Ad4Fg8Ad | Stage 3 Loader payload |
| File Hash (MD5) | ADABj55k2Ehdg4AFddhd4Dkk4ij4DAFg8Ad | Stage 4 Loader payload |
| File Hash (MD5) | MBFek2jiNAfmiF7Bj2Ei2BijfD2BmfkA2E | Stage 5 Loader payload |
| File Hash (MD5) | kle7BfliimA4ili77kjh7fedekj4Djhhlj | STX RAT final payload |
| File Name | HWMonitor_x64.exe | Legitimate binary abused for DLL sideloading |
| File Name | CRYPTBASE.dll | Malicious DLL placed in application directory |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.