Exploit: Hackers Take Over cPanel Abuse CVE-2026-41940
A critical authentication bypass vulnerability is actively being exploited, impacting cPanel and WebHost Manager (WHM) servers worldwide. Tracked as CVE-2026-41940 and bearing an apocalyptic maximum...
A critical authentication bypass vulnerability is actively being exploited, impacting cPanel and WebHost Manager (WHM) servers worldwide.
Tracked as CVE-2026-41940 and bearing an apocalyptic maximum severity score of 9.8, this critical flaw has essentially handed the keys to the kingdom directly to cybercriminals.
Without needing a single username or password, unauthenticated remote attackers are ruthlessly shattering security perimeters to seize absolute administrator control.
Threat actors are now aggressively weaponizing this zero-day exploit, unleashing a tidal wave of ransomware, parasitic cryptominers, and deeply embedded backdoors across vulnerable Linux environments.
Since its public disclosure in late April 2026, threat intelligence platforms have observed a massive surge in automated attacks targeting this vulnerability.
DailyDarkWeb reports that over 2,000 unique IP addresses worldwide, primarily originating from the United States, Germany, Brazil, and the Netherlands, are actively scanning for and exploiting this flaw.
Highlighting the severity of the threat, security researchers at Ctrl-Alt-Intel revealed on May 2.
That hackers successfully weaponized this vulnerability to breach Southeast Asian government and military networks, stealing nearly 4.37 GB of sensitive archives dating from 2020 to 2024.
CVE-2026-41940 Hijacks cPanel Servers
Security analysts from XLab have attributed a highly sophisticated, ongoing campaign to a covert hacking collective internally dubbed “Mr_Rot13”.
Operating quietly since at least 2020, this group has a history of deploying malicious PHP backdoors that completely evade detection on major antivirus scanning platforms.
The group earned its moniker by frequently using the Rot13 algorithm to obfuscate its command-and-control (C2) infrastructure within injected JavaScript payloads.
Recent investigations reveal that Mr_Rot13 is a highly organized operation rather than an opportunistic script-kiddie ring.
The group relies on custom, well-maintained malware and reacts dynamically to security researchers probing their infrastructure.
For example, they frequently rotate their Telegram bot tokens and upgrade their malware payloads to evade active detection and analysis.
The infection process begins when attackers exploit CVE-2026-41940 to bypass authentication, granting them immediate administrator privileges on the target server.
Without providing a username or password, the threat actors deploy a Go-based injector tool named “Payload.”
Researchers from XLab note that the code structure and logging style of this tool appear to be generated by artificial intelligence.
Once executed, the injector immediately alters the server’s root password and implants malicious SSH public keys to ensure persistent backdoor access.
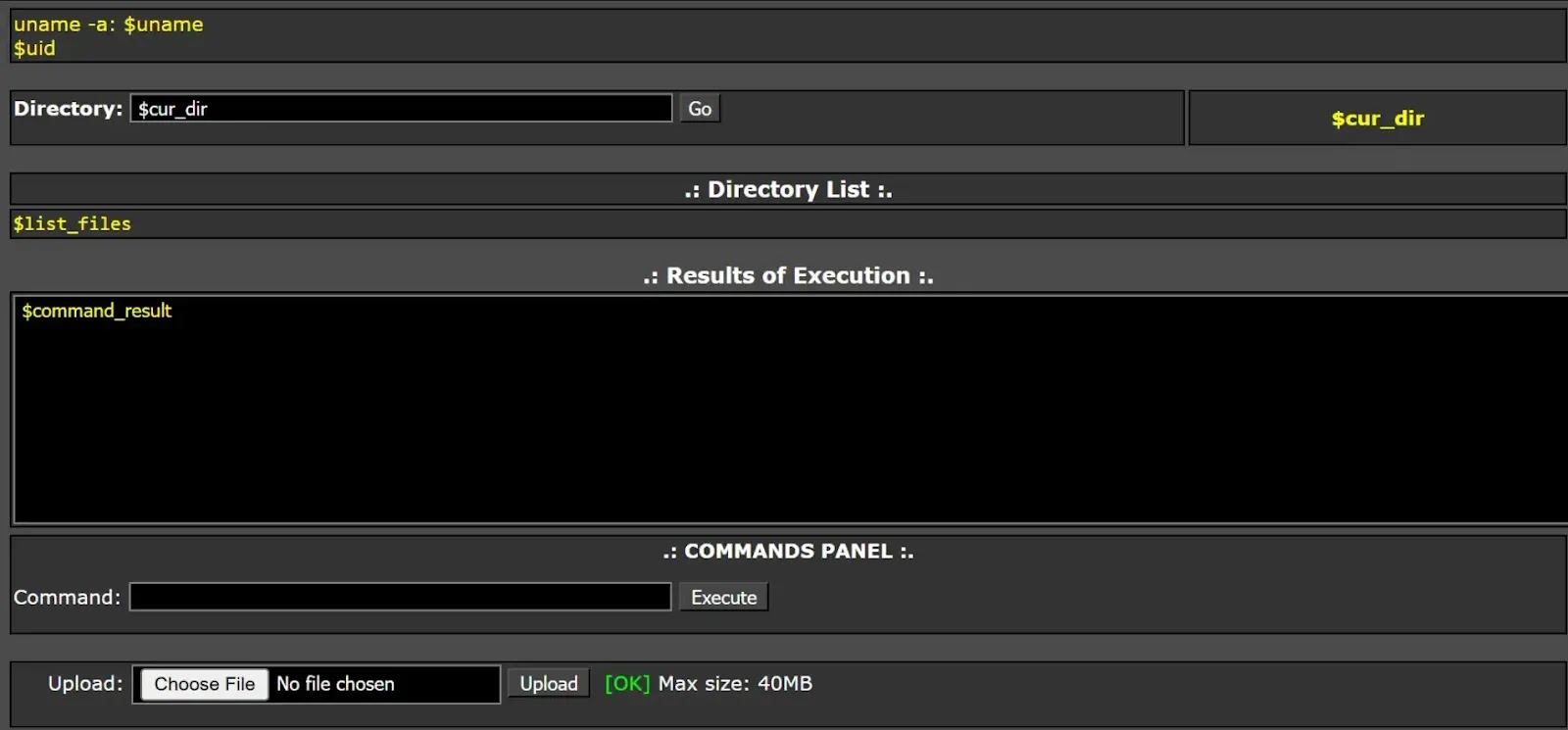
The malware then drops a custom PHP webshell known as “Cpanel-Python”. It injects malicious JavaScript into the server’s custom login pages.
This injected script actively steals user credentials, User-Agent strings, and URLs, forwarding the stolen data to a remote C2 server via an AJAX request.
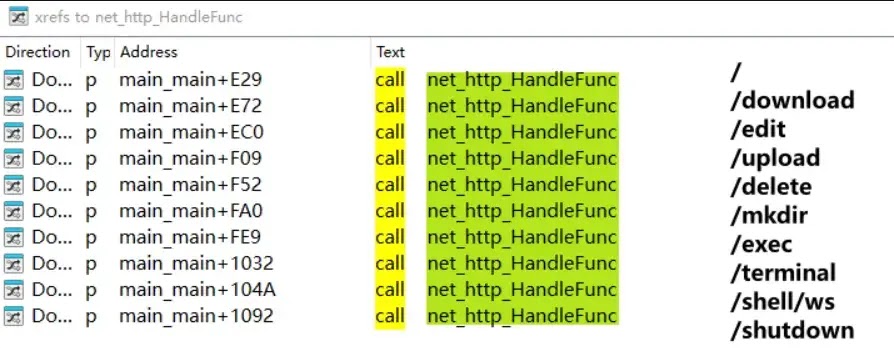
As a final step, the attackers deploy “Filemanager,” a powerful cross-platform remote control Trojan.
This Trojan supports Linux, Windows, and Darwin operating systems, allowing attackers to access a web-based console to execute remote commands and manage files.
Stolen server configurations and database credentials are then exfiltrated through dual channels, sending information back to both the group’s web domains and a dedicated Telegram bot.
Indicators of Compromise (IOCs):
Domains:
cp.dene.de[.]comwrned[.]comwpsock[.]com
MD5 Hashes:
fb1bc3f935fdeb3555465070ba2db33c9305b4ebbb4d39907cf36b62989a6af32286f126ab4740ccf2595ad1fa0c615c
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.