10 Best Full Disk Encryption Tools in 2026
AxCrypt’s tools and features prove highly advantageous for businesses operating under strict confidentiality protocols and policies. The best use of their tools for securing the sharing of...
AxCrypt’s tools and features prove highly advantageous for businesses operating under strict confidentiality protocols and policies.
Table Of Content
The best use of their tools for securing the sharing of public keys will be made by businesses and agencies that collaborate with numerous stakeholders across all endpoints.
AxCrypt provides essential security tools for encryption, editing encrypted files, secure file deletion, password generation, and password storage. Its streamlined interface lets users encrypt and decrypt data quickly using a drag-and-drop method.
The straightforward yet effective tools AxCrypt provides make encryption hassle-free and easy. Additionally, AxCrypt has features that let users access encrypted data on their mobile devices.
Features
- All temporary and plaintext files that have been encrypted are destroyed.
- The secured file is automatically updated after being opened and saved.
- Files that have been encrypted cannot be changed without detection.
- The password management tool lets you safely save passwords and codes online.
- AxCrypt folders are created after automatically detecting cloud storage programs on your PC.
| What Could Be Better? | What Could Be Better ? |
|---|---|
| 1. Open source, under the GNU General Public License. | 1. If the PC’s local security is compromised, the software is very hazardous. |
| 2. The UI is easy to use and learn. | 2. Enterprise businesses might prefer an advanced solution. |
| 3. Possesses a feature for managing passwords. | |
| 4. Secures data with simple yet effective encryption. |
7. Linux Unified Key Setup
Year: 2004
Clemens Fruhwirth developed the Linux Unified Key Setup (LUKS), a disk encryption specification initially created for GNU/Linux.
LUKS specifies a platform-independent standard on-disk format for use in various security tools. It aims to provide a standardized and compatible format for disk encryption software.
This not only makes it easier for different software to work together and interact with one another, but it also ensures that every piece of software uses password management in a safe and well-documented way.
LUKS is frequently used to provide full disk encryption, which encrypts the root partition of an operating system installation and guards against unauthorized access to the operating system files.
Since the encrypted device’s contents are arbitrary, any file system, including swap partitions, can be encrypted.
Features
- Device Mapper Crypt (dm-crypt) is LUKS’ kernel module for block device encryption.
- It strengthens passphrases against dictionary assaults.
- Backup keys can be added to LUKS services’ multiple vital slots.
- Data on encrypted block devices can be anything.
- Encrypt partitions on your Linux machine.
| What Could Be Better? | What Could Be Better ? |
|---|---|
| 1.LUKS protects data with strong disk encryption. | 1. Remembering your LUKS password or key might make data recovery difficult. |
| 2. Open-source standards are public and security-audited. | 2. LUKS encryption of large drives takes time. |
| 3. LUKS is highly supported in Linux, making it easy to install and use. | |
| 4. LUKS hides volumes for added security. |
8. Dm-crypt
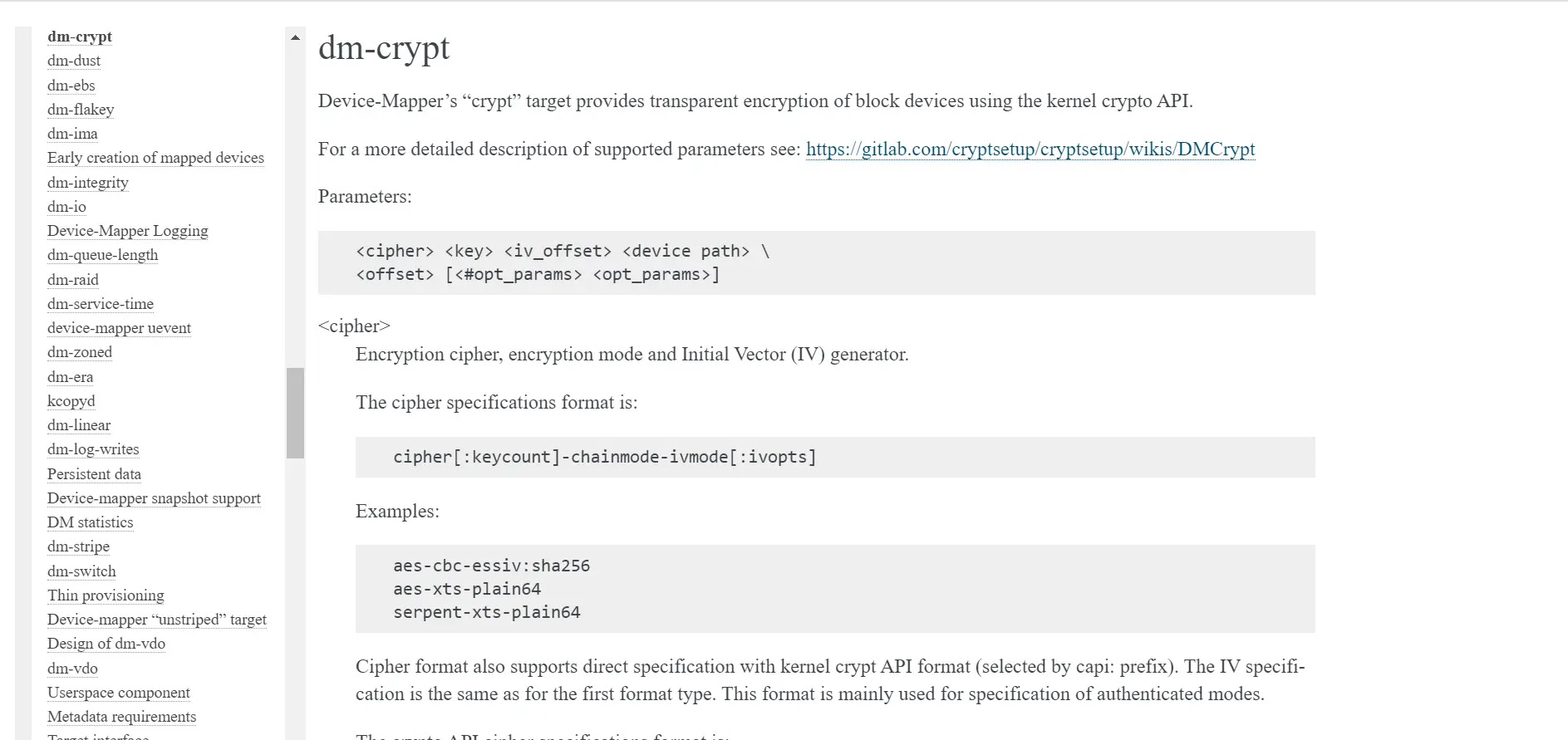
Block devices are transparently encrypted using the kernel Crypto API by Device-Mapper’s “crypt” target. Some Linux distributions permit the use of dm-crypt on the root file system.
These operating system distributions usually use initrd to ask the user to enter a passphrase at the console or insert an intelligent card before starting the system.
In Linux kernel versions 2.6 and later, as well as DragonFly BSD, dm-crypt is a transparent block device encryption subsystem.
It is a component of the device mapper infrastructure and uses the kernel’s Crypto API’s cryptographic routines.
Device mapper targets can be stacked on top of one another, and dm-crypt is implemented as one of them.
Consequently, it can encrypt entire disks (including removable media), partitions, software RAID volumes, logical volumes, and files.
Features
- Since Ciphershed is open-source, anyone can access its source code.
- The cipher shed interface lets you unmount the virtual disk after use.
- Virtual volumes cannot be accessed without a password.
- For brute force protection, volumes are encrypted with strong ciphers.
- You can also develop a covert operating system that is accessible when needed and invisible.
| What is Good? | What Could Be Better? |
|---|---|
| 1. Enables full disk encryption. | 1. All encryption parameters must be handled with extreme care. |
| 2.dm-crypt secures disks from illegal access. | 2. There is only one encryption key and no way to change it. |
| 3. Encrypts partitions smoothly, minimizing OS disturbances. | |
| 4. Open-source solutions are transparent and security-audited |
9. NordLocker
NordLocker is an easy-to-use tool for file encryption. It enables secure data storage and sharing. NordLocker uses strong encryption to secure our files by dragging and dropping them to a Locker folder.
A locker is an encrypted folder in NordLockers. Along with the configuration information, it includes your files.
The files you store in a locker are only accessible by you unless you grant access to others using the “Add user access” function in the NordLocker application.
NordLocker was designed specifically to encrypt files. It can and excels at encrypting any file format. Public-key cryptography makes it safe to share files with strangers because your password is never revealed.
NordLocker encrypts and decrypts your files using Argon2, AES256, ECC (with XChaCha20, EdDSA, and Poly1305 ciphers), and other advanced cryptography ciphers.
Features
- Easily sync and safeguard files
- Available via Android, iOS, Windows, Mac OS, and Linux browser apps.
- Create lockers and folders for your files, then store them locally or online.
- Any size file can be encrypted.
- Your Nord Locker cloud files are always encrypted.
| What is Good? | What Could Be Better ? |
|---|---|
| 1. an elegant drag-and-drop layout | 1. Neither Linux nor mobile clients |
| 2. Storage of encrypted files on desktops and the cloud | 2. A two-factor authentication option is not available. |
| 3. Directly access lockers to open, modify, and save files. | |
| 4. It is safe for users to share encrypted files. |
10. Ciphershed
Ciphershed is a free encryption tool for protecting the privacy and security of our data. It was originally a fork of the TrueCrypt project. Cross-platform Ciphershed is offered for Windows, Mac OS X, and GNU/Linux.
Because there are no packages for CipherShed on OS X or Linux, users of those operating systems must compile it. Your files and data can be encrypted using encrypted containers that you make with CipherShed.
Solid and secure, this encryption can be used for various files, including financial records, priceless information, sensitive information, and other things you want to keep private.
CipherShed is a safe and sophisticated encryption tool that will help you securely store sensitive data and encrypt it so that no one else can access it without your permission.
Features
- Since Ciphershed is open-source, anyone can access its source code.
- The cipher shed interface lets you unmount the virtual disk after use.
- Virtual volumes cannot be accessed without a password.
- Volumes are encrypted with solid ciphers to prevent brute-force attacks.
- You can also develop a covert operating system that is accessible when needed and invisible.
| What is Good? | What Could Be Better? |
|---|---|
| 1. It is an open-source program that is completely free. | 1. It is difficult to improve key derivation. |
| 2. It is compatible with Windows, OS X, and Linux. | 2.Inexperienced users face 151-page steps. |
| 3. Ciphershed’s portable installer just extracts files. | |
| 4. For best results, advanced users should use Ciphershed. |








No Comment! Be the first one.