UAT-8302 Uses Custom Malware and Open-Source Tools to Steal Data
A sophisticated China-linked hacker group, What makes UAT-8302 particularly dangerous is its ability to blend in. By pairing legitimate cloud services and open-source tools with custom-built malware,...
A sophisticated China-linked hacker group,
What makes UAT-8302 particularly dangerous is its ability to blend in. By pairing legitimate cloud services and open-source tools with custom-built malware, the group makes it harder for defenders to separate genuine network activity from a hostile intrusion.
The attackers display a high level of patience, conducting deep and methodical reconnaissance on every endpoint they can reach before pushing further into the target environment. This careful, deliberate approach is widely recognized as a hallmark of state-sponsored threat operations targeting high-value government infrastructure.
Researchers at Cisco Talos identified UAT-8302 as a China-nexus advanced persistent threat group tasked primarily with gaining and maintaining long-term access to government and related entities around the world.
Talos analysts assessed with high confidence that the group shares tooling with several previously disclosed China-nexus clusters, including a threat cluster they track as LongNosedGoblin. The overlap in tools and techniques points to a close operational relationship between these groups.
UAT-8302’s Custom Malware Arsenal
The post-compromise activity follows a familiar and thorough playbook. Once inside a network, the group collects credentials, gathers Active Directory information, and maps out the entire environment before deploying additional malware.
Tools like Impacket, custom PowerShell scripts, and open-source scanning engines are used to discover every reachable endpoint. This approach ensures that attackers fully understand the scope of the environment they now control before deciding on their next move.
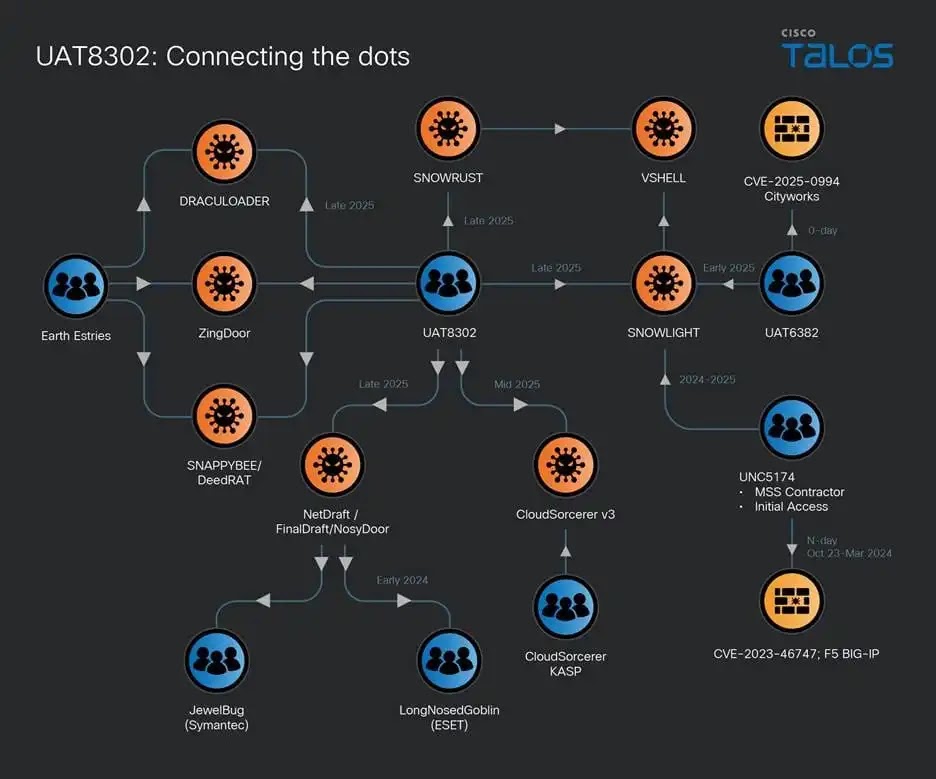
The variety of malware families deployed by UAT-8302 shows the group has access to a well-stocked toolkit. The group deploys NetDraft, a .NET-based backdoor linked to the FinDraft and SquidDoor family, alongside an updated version of the CloudSorcerer backdoor and the VSHELL implant. In one documented intrusion, the group also deployed SNAPPYBEE and ZingDoor together, a tactic independently highlighted by Trend Micro in 2024 reporting on similar China-linked activity.
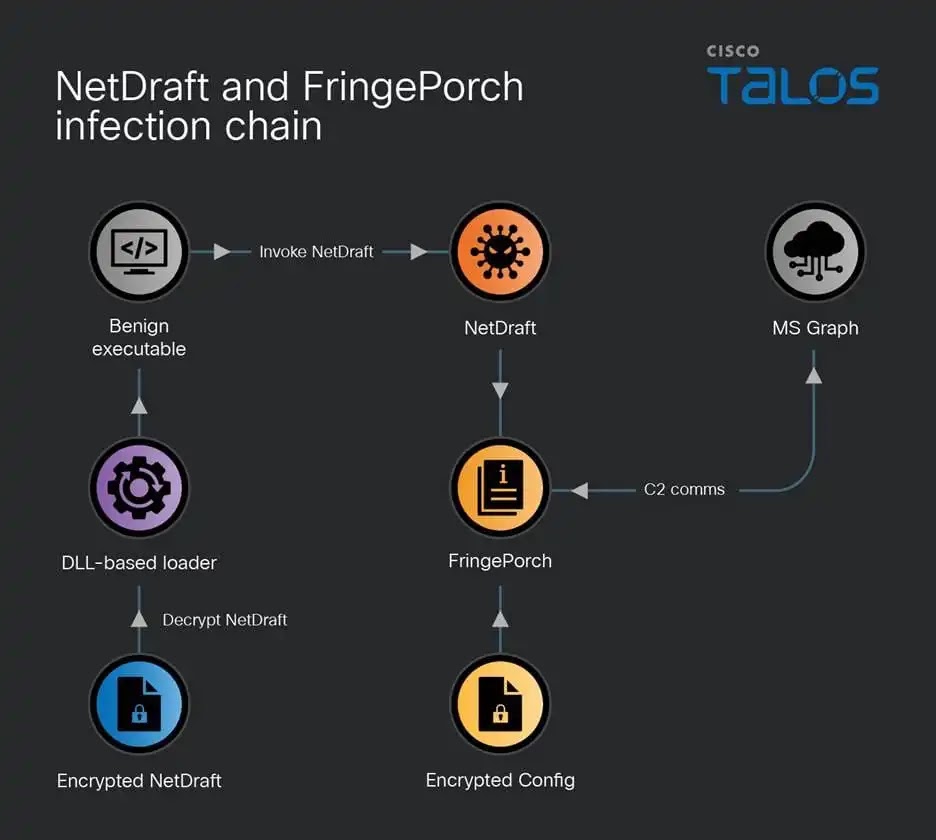
NetDraft is one of the most notable tools in UAT-8302’s arsenal. It is delivered through a DLL side-loading technique where a benign executable loads a malicious DLL-based loader, which then decodes and runs NetDraft within an existing process on the compromised system.
The malware uses the Microsoft Graph API to communicate with its OneDrive-based command-and-control server, allowing it to blend into normal cloud traffic and avoid detection. Talos tracks the embedded helper library used by NetDraft as “FringePorch.”
CloudSorcerer version 3 behaves differently depending on which process it runs inside. If injected into “dnapimg.exe,” it collects system details and pivots into explorer.exe to receive commands through a named pipe channel.
If running inside “spoolsv.exe,” it contacts a GitHub repository to pull down command-and-control information. This shape-shifting behavior makes detection harder for conventional security tools. Talos also noted the use of SNOWRUST, a Rust-based variant of the SNOWLIGHT stager seen in intrusions attributed to other China-nexus clusters.
Open-Source Tools and Lateral Movement
UAT-8302 relies heavily on open-source tools when moving through compromised networks. After gaining initial access, the group runs scanning tools including gogo, naabu, httpx, and PortQry to map services across internal networks and discover new systems to pivot toward.
Credentials are harvested from MobaXterm sessions and Active Directory using tools like adconnectdump.py and SharpGetUserLoginRDP.
To maintain persistent backdoor access, the group deploys Stowaway, a proxy tunneling tool written in Simplified Chinese, routing outside traffic into infected hosts within the enterprise. SoftEther VPN clients were also observed in use.
Government agencies should keep endpoint detection tools updated to flag these threat signatures, monitor outbound traffic to cloud platforms like OneDrive and GitHub for unusual patterns, and regularly audit scheduled tasks and DLL side-loading behavior across all managed endpoints.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| SHA256 | 1139b39d3cc151ddd3d574617cf11360812785019 7e9695fef0b6d78df82d6ca | NetDraft / FringePorch |
| SHA256 | e56c49f42522637f401d15ac2a2b6f3423bfb2d5d37d071f0172ce9dc688d4b | NetDraft / FringePorch |
| SHA256 | 51f0cf80a56f322892eed3b9f5ecae45f143132360 0edbaea5cd1f28b437f6f2 | NetDraft / FringePorch |
| SHA256 | 35b2a5260b21ddb145486771ec2b1e4dc1f5b7f2275309e139e4abc1da0c614b | VSHELL |
| SHA256 | 199bd156c81b2ef4fb259467a20eacaa9d861eeb2 002f1570727c2f9ff1d5dab | VSHELL |
| SHA256 | 071e662fc5bc0e54bcfd49493467062570d0307dc46f0fb51a68239d281427c6 | ZingDoor |
| SHA256 | 74098b17d5d95e0014cf9c7f41f2a4e4be8baefc2b0eb42d39ae05a95b08ea5 | gogo |
| SHA256 | 2b627f6afe1364a7d0d832ccba87ef33a8a39f30a70a5f395e2a3cb0e2161cb3 | gogo |
| SHA256 | 7c593ca40725765a0747cc3100b43a29b88ad1708ef77e915ab02686c0153001 | Stowaway |
| SHA256 | f859a67ceebc52f0770a222b85a5002195089ee442eac4bea761c29be994e2ea | Stowaway |
| SHA256 | 7d9c70fc36143eb33583c30430dcb40cf9d306067594cc30ffd113063acd6292 | anypoxy |
| SHA256 | 57GER1bb59491f7289b94ab0130d7065d74d2459a802a7550ebf8cd0828f0a09c4d38 | PortQry scan tool |
| SHA256 | 843f8aea7842126e906cadbad8d81fa456c184fb5372c6946978a4fe115edb1c | DracuLoader |
| SHA256 | 4109f15056414f25140c7027092953264944664480dd53f086acb8e07d9fccab7 | SoftEther VPN |
| SHA256 | 3dec6703b2cbc6157eb67e80061d27f9190c8301c9dd60eb0be1e8b096482d7e7 | SoftEther VPN |
| SHA256 | 9f115e9b32111e4dc29343a2671ab10a2b38448657b24107766dc14ce528fceb | SharpGetUserLoginRDP |
| SHA256 | b19bfca2fc3fdabf0d0551c2e66be895e49f92aedac56654b1b0f51ec66e74042 | SharpGetUserLoginRDP |
| SHA256 | 45cd169bf9cd7298d972425ad0d4e98512f29de4560a155101ab7427e4f4123f4 | PortQry |
| SHA256 | fb6cebadd49d202c8c7b5cdd641bd16aac8258429e8face365a94bd32e253b00 | PortQry |
| Domain | www[.]drivelivelime[.]com | NetDraft C2 domain |
| URL | hxxps[://]www[.]drivelivelime[.]com/x | NetDraft C2 URL |
| URL | hxxps[://]www[.]drivelivelime[.]com/p | NetDraft C2 URL |
| Domain | msiidentity[.]com | C2 domain |
| URL | hxxps[://]msiidentity[.]com/pw | C2 URL |
| Domain | trafficmanagerupdate[.]com | C2 domain |
| URL | hxxp[://]trafficmanagerupdate[.]com/index[.]php | C2 URL |
| Domain | update-kaspersky[.]workers[.]dev | C2 domain (Cloudflare Worker) |
| IP Address | 85[.]209[.]156[.]3 | Stowaway proxy / C2 server |
| URL | hxxp[://]85[.]209[.]156[.]3:8080/wagent[.]exe | Malware download URL |
| URL | hxxp[://]85[.]209[.]156[.]3:8082/wagent[.]exe | Malware download URL |
| IP Address | 185[.]238[.]189[.]41 | C2 server |
| IP Address | 103[.]27[.]108[.]55 | C2 server |
| IP Address | 38[.]54[.]32[.]244 | Malware staging server |
| URL | hxxp[://]38[.]54[.]32[.]244/Rar[.]exe | RAR archive download |
| IP Address | 45[.]140[.]168[.]62 | C2 server |
| IP Address | 88[.]151[.]195[.]133 | C2 server |
| IP Address | 156[.]238[.]224[.]82 | C2 server |
| IP Address | 45[.]135[.]135[.]100 | C2 server (anypoxy) |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.