ScarCruft Supply Chain Attack Hits Gaming with Platform Windows
A North Korea-aligned threat group, identified as ScarCruft, has launched a supply chain attack against a video gaming platform primarily serving ethnic Koreans in China’s Yanbian region. This...
A North Korea-aligned threat group, identified as ScarCruft, has launched a supply chain attack against a video gaming platform primarily serving ethnic Koreans in China’s Yanbian region. This sophisticated operation involved the deployment of both Windows and Android backdoors, as detailed in a
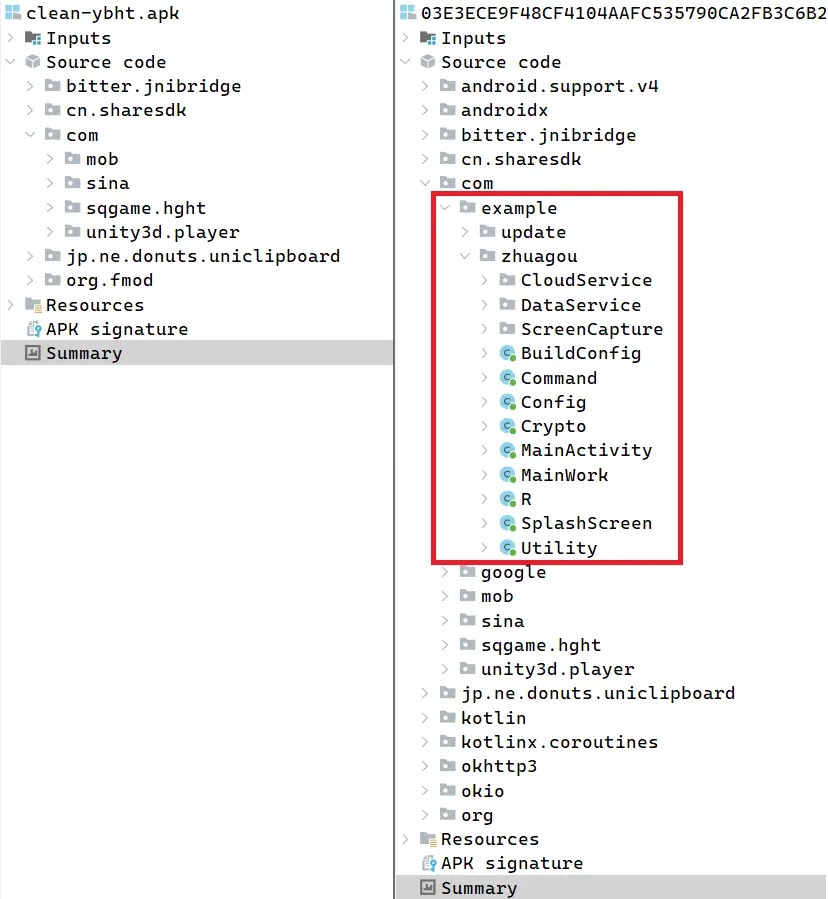
The compromised platform is sqgame, a service hosting traditional Yanbian-themed card and board games for Windows, Android, and iOS users. ScarCruft did not break into the game’s source code directly.
Instead, the group appears to have accessed the platform’s web server and repackaged the original Android game files with malicious code.
Two of the Android games on the sqgame website were trojanized to carry the BirdCall backdoor, while the Windows client was hit through a malicious update package.
The iOS version showed no signs of tampering, likely because Apple’s review process made it harder to target.
WeLiveSecurity analysts identified the full scope of this multiplatform supply chain attack, attributing it to ScarCruft with high confidence.
The team noted that Android BirdCall was a new tool in the group’s arsenal and provided the first public analysis of the Android variant.
ESET telemetry confirmed the malicious Windows update had been active since at least November 2024, delivering the first-stage RokRAT backdoor, which then dropped the more capable BirdCall backdoor onto victim machines.
ScarCruft, also tracked as APT37 or Reaper, has been active since at least 2012 and is widely considered a North Korean state-sponsored espionage group.
It primarily targets South Korea but has also hit other Asian countries, focusing on government bodies, military organizations, and industries linked to North Korean interests.
The Yanbian region, which borders North Korea and holds the largest ethnic Korean community outside the peninsula, fits the group’s targeting profile closely, especially as a crossing point for defectors.
ESET notified sqgame of the compromise in December 2025 but had received no response at the time of publication.
How the BirdCall Backdoor Works
The Android version of BirdCall, internally named “zhuagou” (Chinese for “catching dogs”), spreads through trojanized game packages hosted on the sqgame website.
The modified AndroidManifest.xml in each APK redirects the app’s startup to the backdoor’s code. Once the user opens the game, the backdoor runs silently in the background before returning control to the legitimate game, keeping the infection invisible.

On first run, the backdoor collects a full directory listing of shared storage and harvests the user’s contacts, call logs, and SMS messages.
It connects to cloud storage using hardcoded credentials and uploads data including RAM, IMEI, IP and MAC address, and geolocation.
Communication runs over HTTPS through Zoho WorkDrive accounts, and researchers found 12 separate drives used in the campaign. In some versions, audio recording via the microphone is active between 7 PM and 10 PM local time.
The backdoor also captures screenshots and steals files with extensions including .jpg, .doc, .pdf, .xls, .xlsx, .ppt, .pptx, .txt, .hwp, .m4a, and .p12.
On Windows, ScarCruft embedded a trojanized mono.dll in an sqgame update package. A downloader inside the library first checks for analysis tools and virtual environments before fetching shellcode from a compromised South Korean website that contains RokRAT.
After dropping the payload, it replaces itself with a clean copy to erase evidence. RokRAT then installs the full BirdCall backdoor on the victim machine.
Users should only install apps from trusted stores like Google Play and keep devices patched at all times.
Security teams should flag unexpected HTTPS traffic to cloud platforms from gaming applications. A full Indicators of Compromise list is available in the ESET GitHub repository for threat hunting.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.