Iranian MOIS Uses Multiple Hacker Personas for Cyber Campaign
Iran’s Ministry of Intelligence and Security (MOIS) orchestrates a prolonged and meticulously organized cyber campaign, employing three distinct hacker personas. These identities, known as...
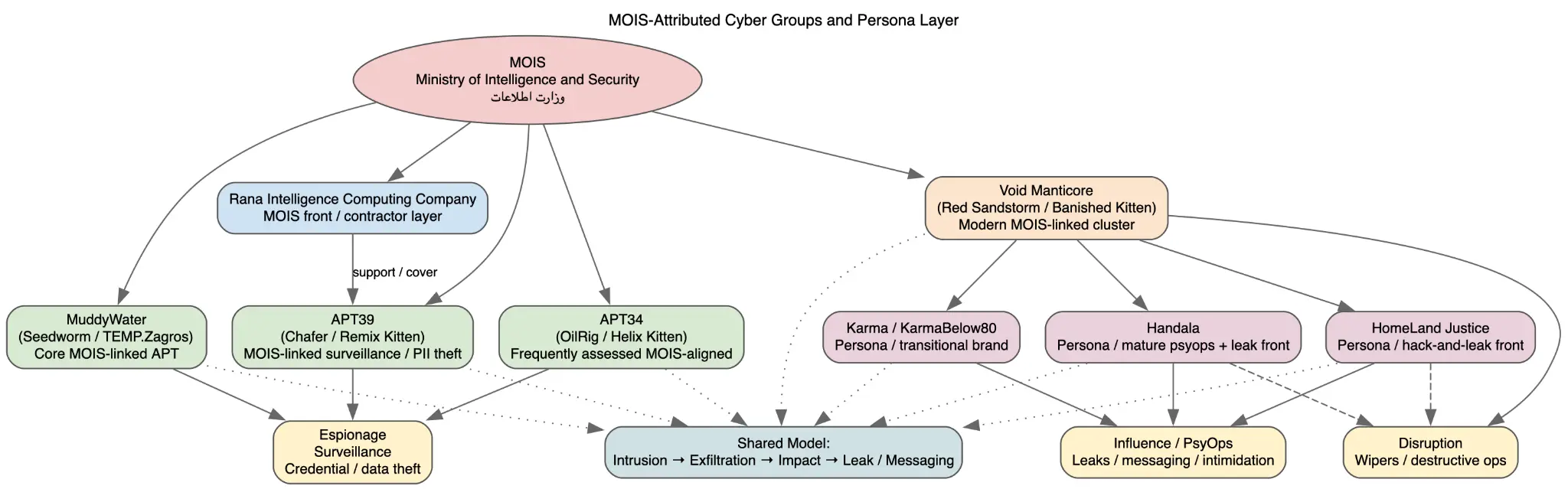
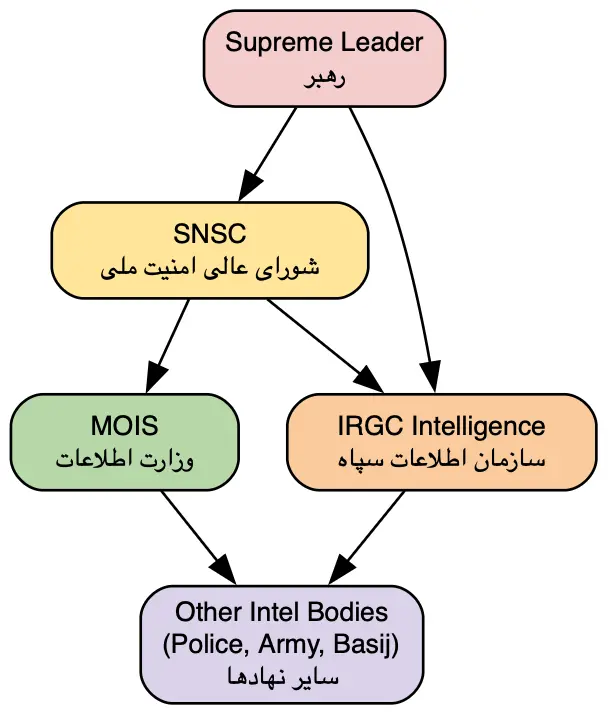
Iran’s Ministry of Intelligence and Security (MOIS) orchestrates a prolonged and meticulously organized cyber campaign, employing three distinct hacker personas.
These identities, known as Homeland Justice, Karma/KarmaBelow80, and Handala, were widely believed to be independent hacktivist groups.
However, a detailed investigation has now confirmed that all three are part of a single, state-directed operation controlled by the Iranian government.
The campaign blends cyber intrusions, sensitive data theft, destructive attacks, and psychological influence operations into one fully coordinated strategy targeting governments and organizations across multiple countries.
The story began in 2022 when a group calling itself “Homeland Justice” launched a series of attacks against the Government of Albania. What made this operation stand out was the level of planning involved.
Iranian state actors had already gained access to Albanian government systems approximately fourteen months before going public with their attacks.
They used this access to steal sensitive documents, deploy destructive tools, and make high-profile public announcements claiming credit for the damage.
This combination of hacking and deliberate public messaging turned a technical attack into a carefully staged influence event with significant geopolitical effects.
DomainTools analysts identified that the same threat actor later pivoted to a new persona called “Karma,” and then “KarmaBelow80,” shifting focus to Israeli organizations in late 2023.
Researchers noted that the underlying tools, infrastructure, and attack methods remained fully consistent across these rebranded campaigns.
Shared domain patterns, the consistent use of Telegram for command-and-control communications, and repeated technical behaviors across what appeared to be separate groups gave DomainTools high confidence to assess all of them as one connected system operating directly under MOIS authority.
By 2024 and continuing into 2026, the operation evolved under the “Handala” banner. Named after the well-known Palestinian cartoon character, the Handala persona focused heavily on information operations, including curated data leaks and targeted harassment of journalists, dissidents, and Israeli-connected individuals.
The Justice Department responded in March 2026, announcing the seizure of four linked domains: Handala-Hack.to, Karmabelow80.org, Justicehomeland.org, and Handala-Redwanted.to.
These domains had been actively used to publish stolen data, claim responsibility for attacks, and call for violence against specific named individuals.
The overall threat actor is tracked as “Void Manticore” by security researchers and also referenced as MOIST GRASSHOPPER in DomainTools reporting.
The group is directly linked to Iran’s MOIS and represents one of the most active state-linked cyber influence ecosystems currently in operation.
Its methods go well beyond simple hacking, combining long-term network access with psychological pressure, data weaponization, and carefully timed public releases that are designed to shape public opinion and behavior in targeted countries.
Multi-Persona Infrastructure and Deception Tactics
One of the most notable aspects of this campaign is how it uses multiple branded identities to serve distinct operational goals while sharing a single backend infrastructure.
Homeland Justice handles destructive operations against Albania. Karma and KarmaBelow80 targeted Israeli entities during a defined period, while Handala now serves as the primary vehicle for influence and information warfare.
This structure allows Iran’s intelligence service to segment its messaging and targeting while maintaining the outward appearance of completely separate, unconnected hacktivist groups.
The technical infrastructure connecting these personas includes shared hosting patterns, overlapping domain registration behaviors, and the reuse of identical malware components across operations.
The group deployed wiper tools to permanently destroy data, alongside ransomware-style encryption used not for financial gain but purely to maximize operational disruption.
Tools like Rhadamanthys, a commercial infostealer available on darknet forums, appeared in Handala-linked operations paired with custom wipers in phishing campaigns impersonating software updates from vendors such as F5.
Security organizations and government agencies recommend monitoring for suspicious exploitation of internet-facing services such as Microsoft SharePoint, the initial access method used in the Albania campaign.
Organizations should implement strict network segmentation, regularly audit privileged account activity, and deploy endpoint detection tools capable of identifying manual intrusion behavior.
Threat intelligence teams should monitor domain infrastructure associated with MOIST GRASSHOPPER and block domains flagged in the Justice Department’s March 2026 seizure to reduce ongoing exposure.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.