Hackers Phish Via GitHub & Jira Notifications on Abuse Deliver
Cybercriminals are weaponizing widely trusted development and IT tools. Threat actors are now exploiting automated notification features within GitHub and Jira to deliver highly convincing phishing...
Cybercriminals are weaponizing widely trusted development and IT tools. Threat actors are now exploiting automated notification features within GitHub and Jira to deliver highly convincing phishing emails. These malicious messages originate directly from the platforms’ own servers, a tactic detailed in a recent report.
What makes this campaign so dangerous is its simplicity. Traditional phishing relies on spoofed sender addresses or fake lookalike domains that security tools can often detect.
In this case, the emails come from verified infrastructure — real servers tied to GitHub and Atlassian, the company behind Jira.
Since these emails satisfy all standard authentication requirements, including SPF, DKIM, and DMARC, most security gateways have no technical grounds to block them.
Cisco Talos analysts tracked this growing trend and published their findings on April 7, 2026. Their data shows that on February 17, 2026 — the peak day of activity — about 2.89% of all emails from GitHub’s infrastructure were tied to this abuse.
Over a five-day window, roughly 1.20% of traffic from “[email protected]” included an “invoice” lure in the subject line.
Talos researchers refer to this method as the Platform-as-a-Proxy (PaaP) model. Attackers do not need to compromise any system or break into these platforms.
They simply use the existing features — repository commits, project invitations — as channels to push malicious content. The platforms handle the delivery, complete with verified signatures and trusted branding.
In nearly all observed cases, the end goal is credential harvesting. Victims are lured into clicking fake billing alerts, fraudulent support numbers, or deceptive account warnings.
Once a user hands over login credentials, attackers gain an entry point that can lead to unauthorized access, account takeovers, and deeper network compromise.
How the Attack Works: GitHub and Jira Notification Pipelines
On GitHub, the attack begins with creating a repository. The attacker then pushes a commit with message fields loaded with social engineering content. GitHub’s commit interface has two text areas: a short mandatory summary line and a longer optional description.
The attacker places an urgent-sounding hook — such as a fake invoice or billing alert — in the summary, and fills the extended description with the full scam message, including fake phone numbers or fraudulent links.
When the commit is submitted, GitHub automatically notifies all collaborators via email, with the full message embedded in the notification body.
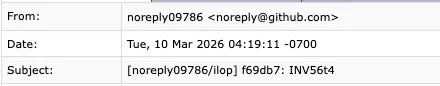
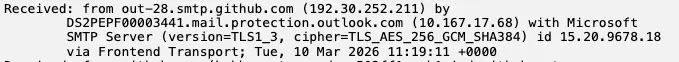
The resulting email appears as a standard GitHub notification. The raw email headers in confirm the sending server as “out-28.smtp.github.com” — a legitimate GitHub mail server with IP “192.30.252.211.”
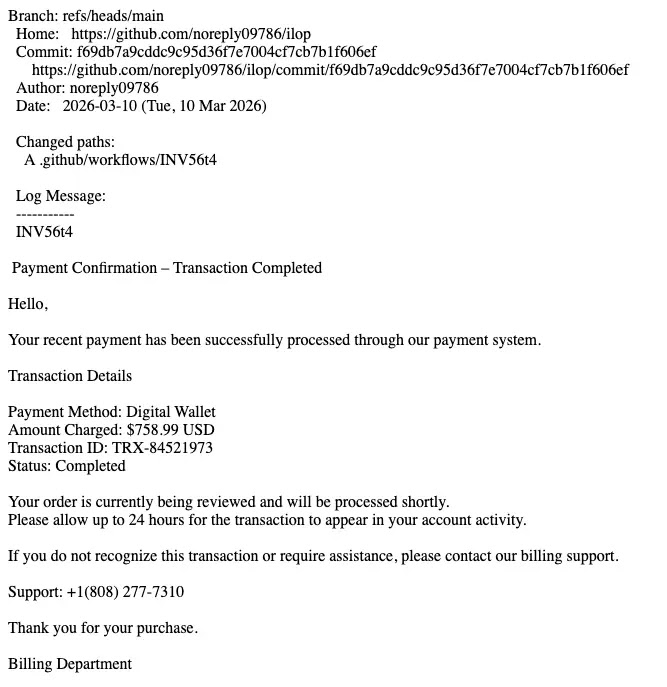
The DKIM signature carries “d=github.com” and passes all checks without raising any security flag.
The Jira approach uses a different mechanism. Attackers create a Jira Service Management project, setting a fake name — such as “Argenta” — and embedding their phishing message inside the “Welcome Message” or “Project Description” field.
Using the “Invite Customers” feature, they submit the target’s email address. Atlassian’s backend then generates an automated invite email, wrapping the attacker’s content inside its own signed and branded template.
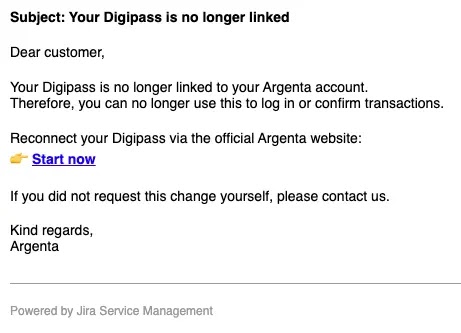
The email arrives looking exactly like an official Jira system notification, complete with Atlassian’s branding footer.
Cisco Talos recommends that organizations shift away from blindly trusting SaaS platform emails.
Security teams should integrate GitHub and Atlassian API audit logs into a SIEM or SOAR system to flag unusual activity — such as mass user invitations or project creation from unfamiliar locations — before any phishing email is sent.
Any notification carrying financial or urgency-driven content from platforms like GitHub or Jira should be flagged for review, as that content conflicts with those tools’ intended purpose.
For sensitive interactions, users should navigate directly to the official platform portal rather than clicking notification links.
Organizations are also encouraged to automate takedown reports to platform Trust and Safety teams to raise the operational cost for attackers.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.