VIPERTUNNEL Python Backdoor Hidden in Fake DLL & Hackers Hide
VIPERTUNNEL, a dangerous Python-based backdoor, is actively infiltrating enterprise networks. Threat actors deploy it hidden within fake DLL files. It also employs multiple layers of code obfuscation...
VIPERTUNNEL, a dangerous Python-based backdoor, is actively infiltrating enterprise networks. Threat actors deploy it hidden within fake DLL files. It also employs multiple layers of code obfuscation to maintain stealth and evade detection, as detailed in a recent analysis available
The attack begins with a scheduled task placed on the victim machine, configured to silently run a legitimate-looking Python interpreter, pythonw.exe, from C:ProgramDatacp49s without any command-line arguments.
This behavior is unusual in normal Windows environments, where Python is rarely invoked this way without a target script.
Instead of pointing to a script directly, the attackers modified a Python startup file called sitecustomize.py, which Python automatically loads every time the interpreter starts.
By embedding malicious code here, they guaranteed silent execution every time the scheduled task fired, leaving nothing suspicious in command-line logs.
InfoGuard Labs analysts, led by researcher Evgen Blohm, identified VIPERTUNNEL during a ransomware incident response engagement in early 2026.
The malware came to light after a persistence audit, when analysts flagged an unusual scheduled task named 523135538 that ran pythonw.exe without arguments.
Closer inspection uncovered the tampered sitecustomize.py, which used Python’s ctypes library to call the Py_GetArgcArgv API, confirm that no command-line input was present, and then silently load a file named b5yogiiy3c.dll via Python’s runpy module.
That file is not a real DLL. It is a Python script wearing a DLL extension — a simple trick to mislead analysts and security scanners. Inside, three layers of obfuscation protect the actual payload.
The malware uses Base85 encoding, AES and ChaCha20 encryption, and control-flow flattening to make reverse engineering slow and difficult.
Each layer decrypts the next and hands off execution in memory, keeping the final payload off disk at all times.
The result is a fully functional SOCKS5 proxy backdoor that connects outbound over port 443, the same port as HTTPS, blending with normal web traffic to avoid detection.
The campaign has been linked to UNC2165 and EvilCorp, with VIPERTUNNEL deployed as a persistent access and network pivot tool.
Threat hunters at InfoGuard Labs also uncovered the same obfuscation framework being used to deliver ShadowCoil, a Python-based credential stealer targeting Chrome, Edge, and Firefox browsers.
Both tools appear to share a private packer utility, and the shared obfuscation pattern alone is treated as a strong indicator of this threat cluster’s ongoing operations.
Obfuscated Loader Chain and SOCKS5 Payload
Once sitecustomize.py triggers the fake DLL, the loader starts processing a high-entropy encoded blob stored at the end of the file.
This blob passes through a custom decryption routine that uses control-flow flattening, replacing sequential code with a while True loop driven by a state variable, forcing analysts to follow each transition manually rather than reading code top to bottom.
Three full obfuscation layers must be peeled back before reaching the final payload.
The recovered payload is a structured Python script built around three classes: Wire, Relay, and Commander. Commander manages the C2 handshake and launches Relay threads on demand.
Relay handles SOCKS5 proxy logic, routing data between the C2 server and internal network targets, while Wire manages socket operations.
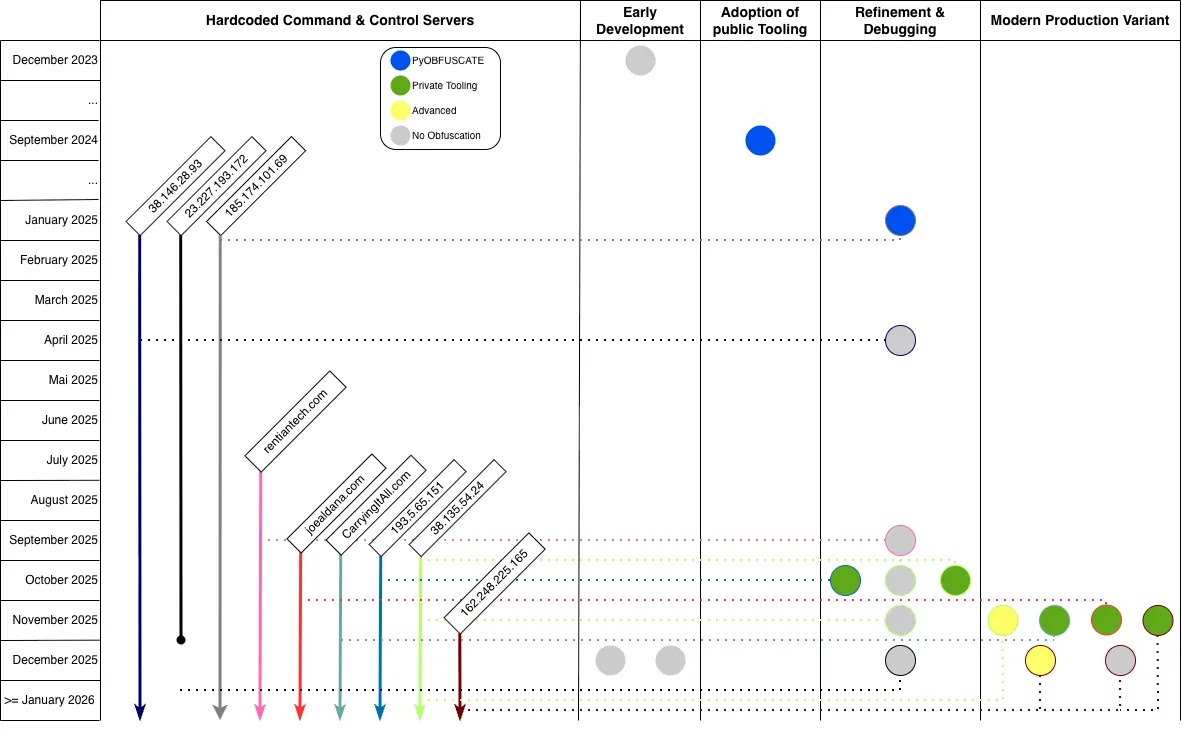
All outbound traffic runs over port 443, with hardcoded default credentials embedded as placeholders. Infrastructure analysis found nearly 30 active C2 nodes, all in the United States and running Ubuntu 22.04 LTS.
Security teams should flag pythonw.exe being called without arguments via a scheduled task and review sitecustomize.py files found outside default Python install paths.
Blocking Python processes from making unexpected outbound connections on port 443 can reduce tunnel activity.
YARA rules targeting class names Wire, Relay, and Commander, along with the error identifier ConnectionTimeoutOccuredError, provide solid detection coverage across all known VIPERTUNNEL variants.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.