Feiniu NAS Infected by Netdragon Botnet Exploiting Un
A new security incident has surfaced, impacting Feiniu (fnOS) Network Attached Storage (NAS) devices. These systems are being actively targeted and infected by the Netdragon botnet, a malware strain...
A new security incident has surfaced, impacting Feiniu (fnOS) Network Attached Storage (NAS) devices.
These systems are being actively targeted and infected by the Netdragon botnet, a malware strain that first appeared in October 2024.
The attackers are leveraging undisclosed security vulnerabilities within the fnOS platform to implant malicious code.
This campaign represents a focused effort to compromise storage infrastructure, moving beyond random infections to specific, high-value hardware targets.
The infection relies on exploiting exposed services on the NAS devices to deploy an HTTP backdoor interface.
Once the attackers gain entry, they install a modular malware system consisting of a loader and a DDoS attack component.
This setup grants them the ability to execute arbitrary commands remotely and conscript the devices into a botnet army.
The compromised units are then used to launch large-scale denial-of-service attacks against various targets.
Alarmingly, the malware was observed deleting a critical private key file, rsa_private_key.pem, on the devices, posing a severe and permanent risk to data security.
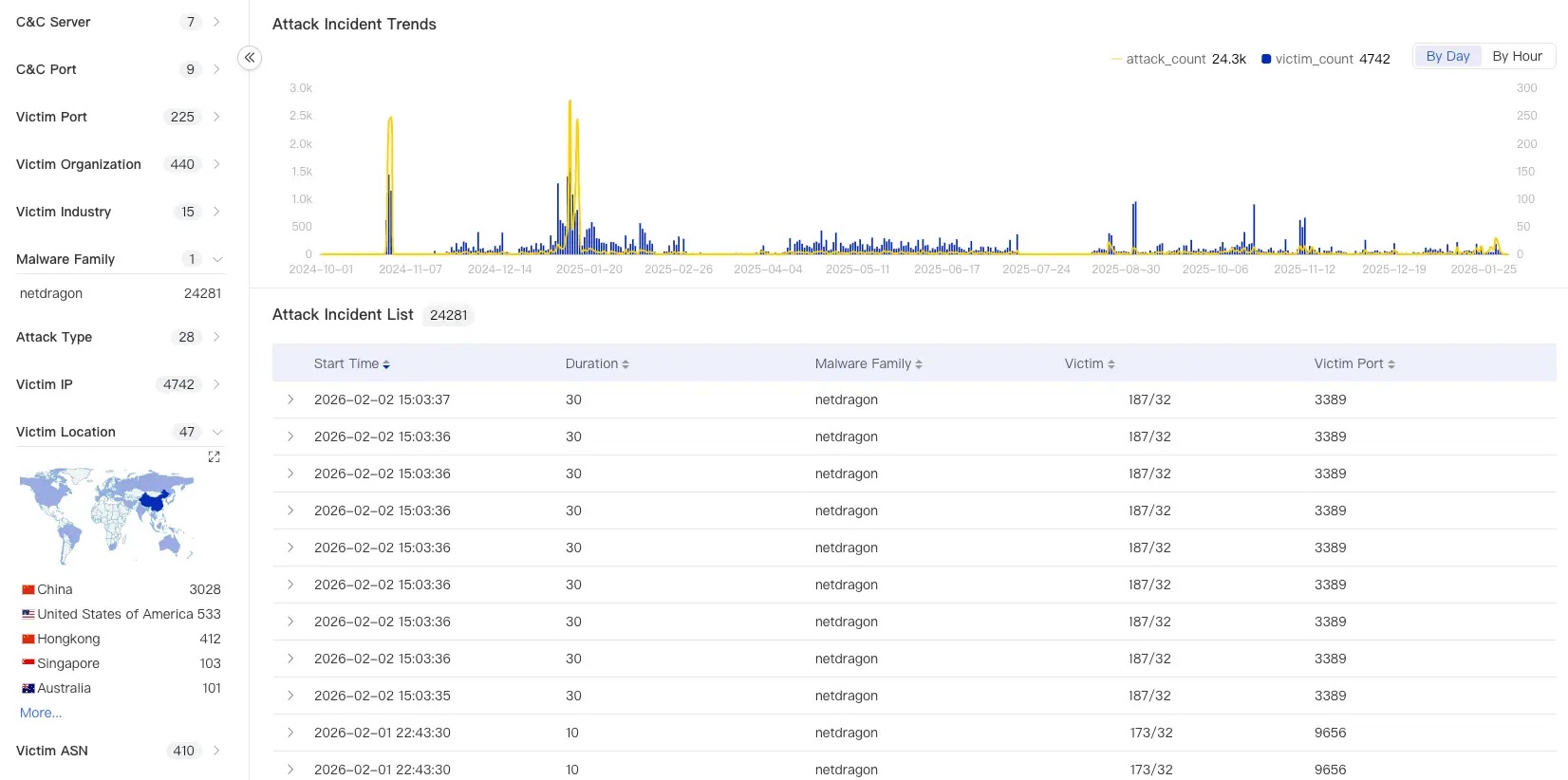
As the investigation progressed, Qi An Xin X Lab analysts identified that the campaign had successfully infected around 1,500 devices by the end of January.

Their data indicates that the victims are geographically dispersed, with significant concentrations in China, the United States, and Singapore. The affected entities span multiple industries, including software services and public administration.
Persistence and Defense Evasion Mechanisms
The Netdragon malware distinguishes itself through aggressive persistence and evasion tactics to maintain control.
It establishes a robust dual foothold by creating both systemd services in the user space and kernel modules in the kernel space.
This redundancy ensures that even if a user identifies and removes one component, the other ensures the malware survives a system reboot.
To further entrench itself, the malware actively sabotages the device’s maintenance capabilities.
It tampers with the system’s hosts file to hijack the official update domain to 0.0.0.0, effectively blocking the NAS from downloading security patches or completing system upgrades.
To remain undetected by administrators, Netdragon employs dynamic key packing to obfuscate its code, which complicates analysis.
It also hides its presence by deleting system logs and manipulating process lists to conceal its running tasks. During active attacks, it specifically disrupts network monitoring tools to mask the surge in traffic.
Recovering from this infection requires careful manual intervention since standard updates are disabled. Users should first remove any manipulated firewall rules from nft and iptables that the malware injected to block removal efforts.
It is critical to locate and delete the malicious kernel module named async_memcpys.ko and the user-mode service dockers.service.
Additionally, administrators must restore the system’s update path by fixing the hosts file and should monitor for the backdoor port 57199 to prevent reinfection.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.