DShield Captures Self-Propagating SSH Worm Expl Sensor Exploit
DShield sensors have detected a sophisticated, self-propagating worm capable of fully compromising Linux systems in just four seconds via SSH brute-force attacks. This rapidly spreading threat,...
DShield sensors have detected a sophisticated, self-propagating worm capable of fully compromising Linux systems in just four seconds via SSH brute-force attacks. This rapidly spreading threat, analyzed in detail as “Four Seconds to Botnet,” has prompted warnings from security researchers. Further technical deep dives are available, including a SANS Internet Storm Center diary and a report from OffSec’s Radar platform.
This new threat combines traditional credential stuffing techniques with modern cryptographic command verification, creating a fast-moving botnet that specifically targets devices with weak authentication mechanisms.
The attack demonstrates how vulnerable systems remain when default passwords are left unchanged, particularly on Internet of Things devices like Raspberry Pi computers.
The malware operates with remarkable efficiency, completing its entire attack lifecycle within seconds of initial contact.
Once an attacker gains access through weak credentials, a compact bash script measuring just 4.7 kilobytes gets uploaded and executed immediately.
This script establishes multiple layers of persistence, eliminates competing malware processes, and connects the compromised device to command and control infrastructure using Internet Relay Chat networks.
Internet Storm Center researchers identified this threat after analyzing traffic captured by DShield honeypot sensors deployed specifically to detect SSH-based attacks.
The investigation revealed that the malware originated from a compromised Raspberry Pi device in Germany, which was itself a victim of the same attack chain.
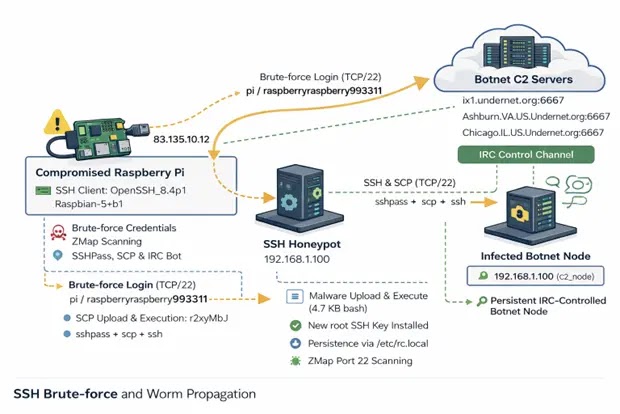
This worm-like propagation pattern allows the botnet to spread exponentially across vulnerable systems connected to the internet.
The attack begins when the malware successfully authenticates using common default credentials, particularly targeting Raspberry Pi devices with username “pi” and passwords like “raspberry” or “raspberryraspberry993311”.
After gaining access, the script immediately creates persistence mechanisms through modified system files and scheduled tasks.
It then kills processes associated with competing botnets and cryptocurrency miners, ensuring exclusive control over system resources.
Advanced Command Verification Through Cryptographic Signatures
What distinguishes this particular threat from typical SSH worms is its implementation of cryptographically signed command verification.
The malware contains an embedded RSA public key that validates all instructions received from the command and control operator before execution. This security measure prevents unauthorized parties from hijacking compromised devices within the botnet.
After establishing persistence, the compromised device joins multiple IRC networks across different geographic locations.
The bot connects to a specific channel named “#biret” where it awaits further instructions.
To propagate further, the malware installs scanning tools including Zmap and sshpass on each infected system, enabling the worm to conduct rapid port scans across 100,000 random IP addresses.
Organizations can protect themselves by disabling password-based SSH authentication and implementing key-based authentication instead.
Additional defenses include removing default user accounts on Raspberry Pi devices, deploying fail2ban for brute-force protection, and implementing network segmentation to isolate IoT devices from critical infrastructure.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.